1. Article purpose[edit | edit source]
The purpose of this article is to:
- briefly introduce the USBH peripheral and its main features,
- indicate the peripheral instances assignment at boot time and their assignment at runtime (including whether instances can be allocated to secure contexts),
- list the software frameworks and drivers managing the peripheral,
- explain how to configure the peripheral.
2. Peripheral overview[edit | edit source]
The USBH peripheral is used to interconnect other systems with STM32 MPU devices, using USB standard.
The USBH peripheral is a USB Host controller supporting high-speed (480 Mbit/s) using an EHCI controller, and full- and low- speeds (12 and 1.5 Mbit/s) through OHCI controller.
The USBH peripheral supports the following PHY interfaces:
| SoC | Number of physical ports (UTMI+) | USBH peripheral PHY interfaces |
|---|---|---|
| STM32MP1 series | 2 | USBPHYC internal peripheral |
| STM32MP2 series | 1 | USB2PHY internal peripheral |
The supported standards are:
- Universal Serial Bus Revision 2.0 Specification[1], Revision 2.0, April 27, 2000
- USB 2.0 Link Power Management Addendum Engineering Change Notice to the USB 2.0 specification[2], July 16, 2007
- Enhanced Host Controller Interface Specification for Universal Serial Bus[3], Revision 1.0, March 12, 2002
- EHCI v1.1 Addendum[4], August 2008
- Open Host Controller Interface Specification for USB[5], Release 1.0a, September 14, 1999
- USB 2.0 Transceiver Macrocell Interface (UTMI) Specification[6], Version 1.05, March 29, 2001
- UTMI+ Specification[7], Revision 1.0, February 25, 2004
Refer to the STM32 MPU reference manuals for the complete list of features, and to the software frameworks and drivers, introduced below, to see which features are implemented.
3. Peripheral usage[edit | edit source]
This chapter is applicable in the scope of the OpenSTLinux BSP running on the Arm® Cortex®-A processor(s), and the FwST-M Package running on the Arm® Cortex®-M processor.
3.1. Boot time assignment[edit | edit source]
3.1.1. On STM32MP1 series[edit | edit source]
The USBH peripheral is usually not used at boot time. But it may be used by the SSBL (see Boot chain overview), for example to boot a kernel stored on a USB key (mass storage).
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given boot time context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given boot time context.
- ☑ means that the peripheral is assigned by default to the given boot time context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32 MPU reference manuals.
| Domain | Peripheral | Boot time allocation | Comment | |||
|---|---|---|---|---|---|---|
| Instance | Cortex-A7 secure (ROM code) |
Cortex-A7 secure (TF-A BL2) |
Cortex-A7 nonsecure (U-Boot) | |||
| High speed interface | USBH (USB Host) | USBH (USB Host) | ☐ | |||
3.1.2. On STM32MP2 series[edit | edit source]
3.1.2.1. For A35-TD flavor  [edit | edit source]
[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given boot time context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given boot time context.
- ☑ means that the peripheral is assigned by default to the given boot time context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32 MPU reference manuals.
| Domain | Peripheral | Boot time allocation | Comment | |||
|---|---|---|---|---|---|---|
| Instance | Cortex-A35 secure (ROM code) |
Cortex-A35 secure (TF-A BL2) |
Cortex-A35 nonsecure (U-Boot) | |||
| High speed interface | USBH | USBH | ⬚ | ☐ | ||
3.1.2.2. For M33-TD flavor  [edit | edit source]
[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given boot time context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given boot time context.
- ☑ means that the peripheral is assigned by default to the given boot time context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32 MPU reference manuals.
| Domain | Peripheral | Boot time allocation | Comment | ||||
|---|---|---|---|---|---|---|---|
| Instance | Cortex-A35 secure (ROM code) |
Cortex-A35 secure (TF-A BL2) |
Cortex-A35 nonsecure (U-Boot) |
Cortex-M33 secure (MCUboot) | |||
| High speed interface | USBH | USBH | ⬚ | ☐ | ⬚ | ||
3.2. Runtime assignment[edit | edit source]
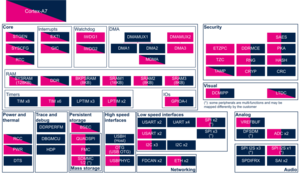
3.2.1. On STM32MP13x lines  [edit | edit source]
[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given runtime context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given runtime context.
- ☑ means that the peripheral is assigned by default to the given runtime context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
Refer to How to assign an internal peripheral to an execution context for more information on how to assign peripherals manually or via STM32CubeMX.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32MP13 reference manuals.
| Domain | Peripheral | Runtime allocation | Comment | ||
|---|---|---|---|---|---|
| Instance | Cortex-A7 secure (OP-TEE) |
Cortex-A7 nonsecure (Linux) | |||
| High speed interface | USBH (USB Host) | USBH (USB Host) | ☐ | ||
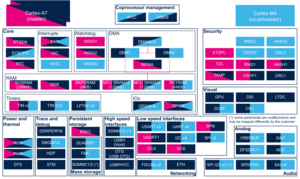
3.2.2. On STM32MP15x lines  [edit | edit source]
[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given runtime context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given runtime context.
- ☑ means that the peripheral is assigned by default to the given runtime context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
Refer to How to assign an internal peripheral to an execution context for more information on how to assign peripherals manually or via STM32CubeMX.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possiblities might be described in STM32MP15 reference manuals.
| Domain | Peripheral | Runtime allocation | Comment | |||
|---|---|---|---|---|---|---|
| Instance | Cortex-A7 secure (OP-TEE) |
Cortex-A7 nonsecure (Linux) |
Cortex-M4 (STM32Cube) | |||
| High speed interface | USBH (USB Host) | USBH (USB Host) | ☐ | ⬚ | ||
3.2.3. On STM32MP21x lines  and STM32MP23x lines
and STM32MP23x lines  [edit | edit source]
[edit | edit source]
The tables below are applicable to any TD flavor (A35-TD or M33-TD) ![]() .
.
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given runtime context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given runtime context.
- ☑ means that the peripheral is assigned by default to the given runtime context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
Refer to How to assign an internal peripheral to an execution context for more information on how to assign peripherals manually or via STM32CubeMX.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32MP21 reference manuals and in STM32MP23 reference manuals.
| Domain | Peripheral | Runtime allocation | Comment | ||||
|---|---|---|---|---|---|---|---|
| Instance | Cortex-A35 secure (OP-TEE / TF-A BL31) |
Cortex-A35 nonsecure (Linux) |
Cortex-M33 secure (TF-M) |
Cortex-M33 nonsecure (STM32Cube) | |||
| High speed interface | USBH | USBH | ⬚OP-TEE | ☐ | ⬚ | ⬚ | |
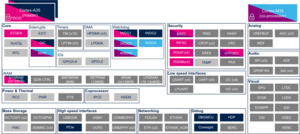
3.2.4. On STM32MP25x lines  [edit | edit source]
[edit | edit source]
The tables below are applicable to any TD flavor (A35-TD or M33-TD) ![]() .
.
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given runtime context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given runtime context.
- ☑ means that the peripheral is assigned by default to the given runtime context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
Refer to How to assign an internal peripheral to an execution context for more information on how to assign peripherals manually or via STM32CubeMX.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32MP25 reference manuals.
| Domain | Peripheral | Runtime allocation | Comment | |||||
|---|---|---|---|---|---|---|---|---|
| Instance | Cortex-A35 secure (OP-TEE / TF-A BL31) |
Cortex-A35 nonsecure (Linux) |
Cortex-M33 secure (TF-M) |
Cortex-M33 nonsecure (STM32Cube) |
Cortex-M0+ (STM32Cube) | |||
| High speed interface | USBH | USBH | ⬚OP-TEE | ☐ | ⬚ | ⬚ | ||
4. Software frameworks and drivers[edit | edit source]
Below are listed the software frameworks and drivers managing the USBH peripheral for the embedded software components listed in the above tables.
- Linux®: USB framework
- U-Boot: USB framework (common/usb.c ) and drivers (ehci-generic.c , ohci-generic.c )
5. How to assign and configure the peripheral[edit | edit source]
The peripheral assignment can be done via the STM32CubeMX graphical tool (and manually completed if needed).
This tool also helps to configure the peripheral:
- partial device trees (pin control and clock tree) generation for the OpenSTLinux software components,
- HAL initialization code generation for the STM32CubeMPU Package.
The configuration is applied by the firmware running in the context in which the peripheral is assigned.
For Linux kernel and U-boot configuration, please refer to USBH device tree configuration.
6. References[edit | edit source]
- ↑ Universal Serial Bus Revision 2.0 Specification
- ↑ ECN USB 2.0 Link Power Management Addendum
- ↑ Enhanced Host Controller Interface Specification for Universal Serial Bus
- ↑ Enhanced Host Controller Interface Specification: Addendum
- ↑ Open Host Controller Interface Specification for USB
- ↑ USB 2.0 Transceiver Macrocell Interface (UTMI) Specification
- ↑ UTMI+ Specification