1. Article purpose[edit | edit source]
This section details the TF-A BL2 stage (Trusted Firmware-A Boot Loader stage 2) used as FSBL (First Stage Boot Loader).
TF-A BL2 is the FSBL for ST boot chain. It is loaded by the ROM code in internal SYSRAM.
The main goal of this stage is to configure the DDR to load (and authenticate) other components from a FIP binary.
2. Device tree[edit | edit source]
TF-A BL2 is based on device tree configuration. It uses the same device tree as the kernel but keeping only the mandatory nodes for the boot stage (to reduce binary size) thanks to a dedicated device tree file (such as fdts/stm32mp15-bl2.dtsi ).
The device tree is part of the final STM32 file in order to be authenticated by the ROM code and loaded at the same time in the SYSRAM.
It must be configured or updated depending on your platform.
3. STM32 binary file[edit | edit source]
To be properly loaded into SYSRAM by the ROM code, the TF-A BL2 firmware needs to be encapsulated in a binary that starts with a STM32 header.
The STM32 header information is mandatory for the ROM code to be able to load, authenticate and start the firmware.
As the ROM code can only load a single binary, the STM32 file must embed in a single image, the header, the device tree and the BL2 binary firmware.
TF-A BL2 is part of the trusted boot and can be signed to be authenticated by ROM code. See Secure boot process for more details.
4. Binary mapping[edit | edit source]
Below the TF-A BL2 mapping including the STM32 header layout:
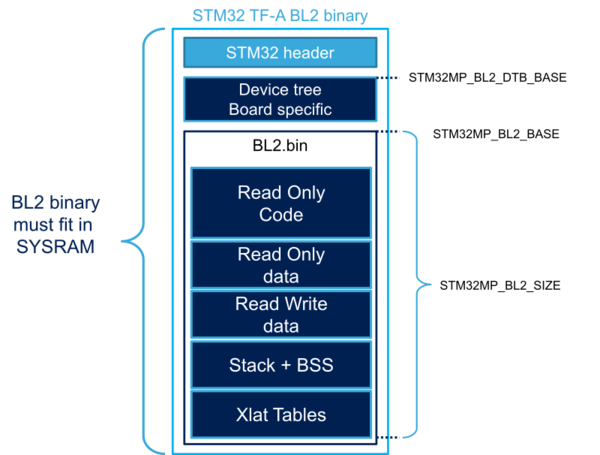
The different sizes can be customized depending on build options and device tree customization. All sizes can be changed in the platform definition file. STM32MP1 platform uses plat/st/stm32mp1/stm32mp1_def.h :
- STM32MP_BL2_DTB_BASE: device tree base address in SYSRAM with its associated SIZE
- STM32MP_BL2_BASE: start address from which the code is loaded and executed
- STM32MP_BL2_SIZE, which cannot exceed SYSRAM size.
5. Boot device[edit | edit source]
5.1. External memory[edit | edit source]
TF-A BL2 needs to access storage devices to load the other software components. By default, it uses the boot device selected by boot pins or OTP.
The selected device needs to be properly set up:
- Device tree configuration (all devices)
- BL2 boot device configuration for Flash memories .
Each device support needs a specific framework in the BL2 firmware.
By default, STMicroelectronics chose to select one single device support per binary. A BL2 with full storage support cannot fit in the SYSRAM size.
Storage build flags allow the BL2 firmware to be configured to support the requested boot storage.
5.2. Serial mode (USB/UART)[edit | edit source]
The Programmer mode (USB or UART boot device) requires the complete FIP binary to start the load image process as previously explained. This is achieved by loading the complete FIP binary into DDR before starting the normal boot sequence. The FIP load address configurable with DWL_BUFFER_BASE parameter. The default value is in plat/st/$PLAT/platform.mk (e.g. plat/st/stm32mp1/platform.mk for STM32MP1 series)
6. DDR[edit | edit source]
TF-A BL2 needs to set up the DDR to load the next binaries. DDR settings come from the device tree and must be adapted by the customer depending on DDR type, DDR configuration and boards. This can be done using STM32CubeMX.
On STM32MP2 series, the DDR PHY needs a firmware. This binary firmware has to be included inside the FIP file. It will be loaded in the PHY during boot process when initializing DDR.
6.1. DDR encryption[edit | edit source]
On STM32MP13x lines ![]() , a region of the DDR can be encrypted, thanks to DDRMCE.
, a region of the DDR can be encrypted, thanks to DDRMCE.
On STM32MP2 series, the DDR encryption is managed by the DDR RISAF peripheral (RISAF4).
The configuration is done in TF-A Firmware configuration device tree, with the DDR encryption configuration.
7. Clock management[edit | edit source]
An initial clock tree must be set up to allow accessing the DDR and the external storage devices.
It also improves the performance by increasing the default CPU speed and the storage transfer speed.
8. FIP[edit | edit source]
The Firmware Image Package (FIP)[1] is a TF-A archive binary that encapsulates bootloader images into a single archive.
It can also contain other data such as certificates that are required to complete the boot process.
See the page How to configure TF-A FIP for more information.
9. FCONF[edit | edit source]
The Firmware Configuration Framework (FCONF)[2] is a way to offer more flexibility in the firmware.
It is used to provide most of the platform-specific data that were previously hard coded inside the firmware. This framework uses device tree (one or multiple) that are passed to the firmware during load processing. BL2 uses it for several purposes:
- list images to be loaded, with their load addresses and max sizes
- DDR firewall configuration
- describe the chain of trust parameters
TF-A BL2 configuration is done with a dedicated device tree file named FW_CONFIG. More details about the FW_CONFIG file are given by the page How to configure TF-A FW CONFIG.
10. Authentication[edit | edit source]
TF-A BL2 manages authentication thanks to Trusted Board Boot activation.