1. Article purpose[edit | edit source]
The purpose of this article is to:
- briefly introduce the DDRCTRL and DDRPHYC peripherals and their main features,
- indicate the peripheral instances assignment at boot time and their assignment at runtime (including whether instances can be allocated to secure contexts),
- list the software frameworks and drivers managing the peripherals,
- explain how to configure the peripherals.
2. Peripheral overview[edit | edit source]
The DDRCTRL and DDRPHYC peripherals are used to configure the physical interface to the external DDR memory. Access to the DDR memory can be filtered via the TZC controller on STM32MP1 series or via RISAF on STM32MP2 series.
Notice that it is possible to perform DDR bandwidth measurement thanks to the DDRPERFM internal peripheral.
Refer to the STM32 MPU reference manuals for the complete list of features, and to the software frameworks and drivers, introduced below, to see which features are implemented.
3. Peripheral usage[edit | edit source]
This chapter is applicable in the scope of the OpenSTLinux BSP running on the Arm® Cortex®-A processor(s), and the STM32CubeMPU Package running on the Arm® Cortex®-M processor.
3.1. Boot time assignment[edit | edit source]
The DDRCTRL and DDRPHYC peripherals are kept secure and used by the FSBL to initialize the access to the DDR where it loads the SSBL (U-Boot) for execution.
STMicroelectronics wishes to make the DDR memory configuration as easy as possible, for this reason a dedicated application note has been published by series (for STM32MP1 series [1] and for STM32MP2 series[2]) and a DDR tuning function is available in STM32CubeMX tool in order to generate the device tree configuration that is given to the FSBL to perform this initialization.
3.1.1. On STM32MP1 series[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given boot time context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given boot time context.
- ☑ means that the peripheral is assigned by default to the given boot time context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32 MPU reference manuals.
| Domain | Peripheral | Boot time allocation | Comment | |||
|---|---|---|---|---|---|---|
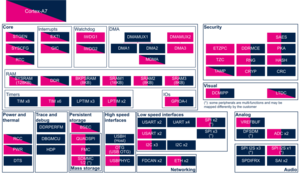
| Instance | Cortex-A7 secure (ROM code) |
Cortex-A7 secure (TF-A BL2) |
Cortex-A7 nonsecure (U-Boot) | |||
| Core/RAM | DDRCTRL | DDR | ☑ | ⬚ | ||
3.1.2. On STM32MP2 series[edit | edit source]
3.1.2.1. For A35-TD flavor  [edit | edit source]
[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given boot time context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given boot time context.
- ☑ means that the peripheral is assigned by default to the given boot time context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32 MPU reference manuals.
| Domain | Peripheral | Boot time allocation | Comment | |||
|---|---|---|---|---|---|---|
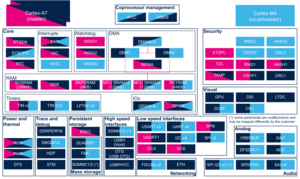
| Instance | Cortex-A35 secure (ROM code) |
Cortex-A35 secure (TF-A BL2) |
Cortex-A35 nonsecure (U-Boot) | |||
| Core/RAM | DDRCTRL & DDRPHYC | DDR | ✓ | ⬚ | Assignment is controlled by the RCC RIF 104 resource that also include the PLL2 control. | |
3.1.2.2. For M33-TD flavor  [edit | edit source]
[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given boot time context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given boot time context.
- ☑ means that the peripheral is assigned by default to the given boot time context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32 MPU reference manuals.
| Domain | Peripheral | Boot time allocation | Comment | ||||
|---|---|---|---|---|---|---|---|
| Instance | Cortex-A35 secure (ROM code) |
Cortex-A35 secure (TF-A BL2) |
Cortex-A35 nonsecure (U-Boot) |
Cortex-M33 secure (MCUboot) | |||
| Core/RAM | DDRCTRL & DDRPHYC | DDR | ✓ | Assignment is controlled by the RCC RIF 104 resource that also include the PLL2 control. | |||
3.2. Runtime assignment[edit | edit source]
The DDRCTRL and DDRPHYC peripherals are accessed at runtime by the secure world of the cold boot CPU (see the Boot chain overview for details) to put the DDR in self-refresh state before going into Stop or Standby low power mode:
- On STM32MP13x lines
 , OP-TEE is default located in DDR and it jumps into TF-A BL2 resident code in SYSRAM to configure the DDRCTRL and DDRPHYC
, OP-TEE is default located in DDR and it jumps into TF-A BL2 resident code in SYSRAM to configure the DDRCTRL and DDRPHYC - On STM32MP15x lines
 , OP-TEE is either located in SYSRAM (with CFG_STM32MP1_OPTEE_IN_SYSRAM=y, so it embeds the services to configure the DDRCTRL and DDRPHYC) or in DDR (see previous STM32MP13x lines
, OP-TEE is either located in SYSRAM (with CFG_STM32MP1_OPTEE_IN_SYSRAM=y, so it embeds the services to configure the DDRCTRL and DDRPHYC) or in DDR (see previous STM32MP13x lines  case)
case) - On STM32MP2 series,
- for A35-TD flavor
 : TF-A BL31 secure monitor is running in SYSRAM and configure the DDRCTRL and DDRPHYC after low power request
: TF-A BL31 secure monitor is running in SYSRAM and configure the DDRCTRL and DDRPHYC after low power request - for M33-TD flavor
 : the low power firmware is running in RETRAM and configure the DDRCTRL and DDRPHYC
: the low power firmware is running in RETRAM and configure the DDRCTRL and DDRPHYC
- for A35-TD flavor
On Standby exit, the ROM code loads the FSBL-A that again configures the DDRCTRL and DDRPHYC before proceeding with the wake-up procedure or for M33-TD flavor ![]() jump in the RETRAM low power firmware.
jump in the RETRAM low power firmware.
DDR memory access is controlled by:
3.2.1. On STM32MP13x lines  [edit | edit source]
[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given runtime context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given runtime context.
- ☑ means that the peripheral is assigned by default to the given runtime context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
Refer to How to assign an internal peripheral to an execution context for more information on how to assign peripherals manually or via STM32CubeMX.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32MP13 reference manuals.
| Domain | Peripheral | Runtime allocation | Comment | ||
|---|---|---|---|---|---|
| Instance | Cortex-A7 secure (OP-TEE) |
Cortex-A7 nonsecure (Linux) | |||
| Core/RAM | DDRCTRL | DDR | ☑ | ⬚ | |
3.2.2. On STM32MP15x lines  [edit | edit source]
[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given runtime context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given runtime context.
- ☑ means that the peripheral is assigned by default to the given runtime context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
Refer to How to assign an internal peripheral to an execution context for more information on how to assign peripherals manually or via STM32CubeMX.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possiblities might be described in STM32MP15 reference manuals.
| Domain | Peripheral | Runtime allocation | Comment | |||
|---|---|---|---|---|---|---|
| Instance | Cortex-A7 secure (OP-TEE) |
Cortex-A7 nonsecure (Linux) |
Cortex-M4 (STM32Cube) | |||
| Core/RAM | DDRCTRL | DDR | ☑ | ⬚ | ||
3.2.3. On STM32MP21x lines  and STM32MP23x lines
and STM32MP23x lines  [edit | edit source]
[edit | edit source]
3.2.3.1. For A35-TD flavor  [edit | edit source]
[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given runtime context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given runtime context.
- ☑ means that the peripheral is assigned by default to the given runtime context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
Refer to How to assign an internal peripheral to an execution context for more information on how to assign peripherals manually or via STM32CubeMX.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32MP21 reference manuals and in STM32MP23 reference manuals.
| Domain | Peripheral | Runtime allocation | Comment | ||||
|---|---|---|---|---|---|---|---|
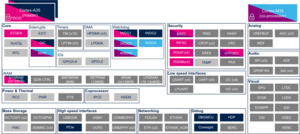
| Instance | Cortex-A35 secure (OP-TEE / TF-A BL31) |
Cortex-A35 nonsecure (Linux) |
Cortex-M33 secure (TF-M) |
Cortex-M33 nonsecure (STM32Cube) | |||
| Core/RAM | DDRCTRL & DDRPHYC | DDR | ✓OP-TEE ✓TF-A BL31 |
⬚ | ☐ | ⬚ | Assignment is controlled by the RCC RIF 104 resource that also include the PLL2 control. |
3.2.3.2. For M33-TD flavor  [edit | edit source]
[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given runtime context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given runtime context.
- ☑ means that the peripheral is assigned by default to the given runtime context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
Refer to How to assign an internal peripheral to an execution context for more information on how to assign peripherals manually or via STM32CubeMX.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32MP21 reference manuals and in STM32MP23 reference manuals.
| Domain | Peripheral | Runtime allocation | Comment | ||||
|---|---|---|---|---|---|---|---|
| Instance | Cortex-A35 secure (OP-TEE / TF-A BL31) |
Cortex-A35 nonsecure (Linux) |
Cortex-M33 secure (TF-M) |
Cortex-M33 nonsecure (STM32Cube) | |||
| Core/RAM | DDRCTRL & DDRPHYC | DDR | ✓ | ⬚ | Assignment is controlled by the RCC RIF 104 resource that also include the PLL2 control. | ||
3.2.4. On STM32MP25x lines  [edit | edit source]
[edit | edit source]
3.2.4.1. For A35-TD flavor  [edit | edit source]
[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given runtime context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given runtime context.
- ☑ means that the peripheral is assigned by default to the given runtime context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
Refer to How to assign an internal peripheral to an execution context for more information on how to assign peripherals manually or via STM32CubeMX.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32MP25 reference manuals.
| Domain | Peripheral | Runtime allocation | Comment | |||||
|---|---|---|---|---|---|---|---|---|
| Instance | Cortex-A35 secure (OP-TEE / TF-A BL31) |
Cortex-A35 nonsecure (Linux) |
Cortex-M33 secure (TF-M) |
Cortex-M33 nonsecure (STM32Cube) |
Cortex-M0+ (STM32Cube) | |||
| Core/RAM | DDRCTRL & DDRPHYC | DDR | ✓OP-TEE ✓TF-A BL31 |
⬚ | ☐ | ⬚ | Assignment is controlled by the RCC RIF 104 resource that also include the PLL2 control. | |
3.2.4.2. For M33-TD flavor  [edit | edit source]
[edit | edit source]
Click on ![]() to expand or collapse the legend...
to expand or collapse the legend...
Check boxes illustrate the possible peripheral allocations supported by the OpenSTLinux BSP:
- ⬚ means that the peripheral can be assigned to the given runtime context, but this configuration is not supported in OpenSTLinux BSP.
- ☐ means that the peripheral can be assigned to the given runtime context.
- ☑ means that the peripheral is assigned by default to the given runtime context and that the peripheral is mandatory for the OpenSTLinux BSP.
- ✓ is used for system peripherals that cannot be unchecked because they are hardware connected in the device.
Refer to How to assign an internal peripheral to an execution context for more information on how to assign peripherals manually or via STM32CubeMX.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possibilities might be described in STM32MP25 reference manuals.
| Domain | Peripheral | Runtime allocation | Comment | |||||
|---|---|---|---|---|---|---|---|---|
| Instance | Cortex-A35 secure (OP-TEE / TF-A BL31) |
Cortex-A35 nonsecure (Linux) |
Cortex-M33 secure (TF-M) |
Cortex-M33 nonsecure (STM32Cube) |
Cortex-M0+ (STM32Cube) | |||
| Core/RAM | DDRCTRL & DDRPHYC | DDR | ✓ | ⬚ | Assignment is controlled by the RCC RIF 104 resource that also include the PLL2 control. | |||
4. Software frameworks and drivers[edit | edit source]
Below are listed the software frameworks and drivers managing the DDRCTRL and DDRPHYC peripherals for the embedded software components (mainly low power sequences, initialization is always handled by TF-A BL2).
4.1. On STM32MP13x lines  [edit | edit source]
[edit | edit source]
- TF-A BL2:
- drivers/st/ddr/ (files with stm32mp1_ and stm32mp_ prefixes)
4.2. On STM32MP15x lines  [edit | edit source]
[edit | edit source]
- TF-A BL2:
- drivers/st/ddr/ (files with stm32mp1_ and stm32mp_ prefixes)
- OP-TEE: (if OP-TEE is in SYSRAM with STM32MP1_OPTEE_IN_SYSRAM)
4.3. On STM32MP2 series[edit | edit source]
- TF-A BL2:
- drivers/st/ddr/ ((files with stm32mp2_ and stm32mp_ prefixes)
- drivers/st/ddr/phy/phyinit/src/
- drivers/st/ddr/phy/phyinit/usercustom/
- TF-M:
- DDR FW binary <ddr_type>_pmu_train.bin is present in TF-A directory drivers/st/ddr/phy/firmware/bin/stm32mp2/ and in GIT repository: https://github.com/STMicroelectronics/stm32-ddr-phy-binary
5. How to assign and configure the peripheral[edit | edit source]
The DDRCTRL and DDRPHYC device tree configuration is generated via STM32CubeMX tool, according to the DDR characteristics (type, size, frequency, speed grade). This configuration is applied during boot time by the FSBL (see boot chain overview).
6. References[edit | edit source]