1. Article purpose
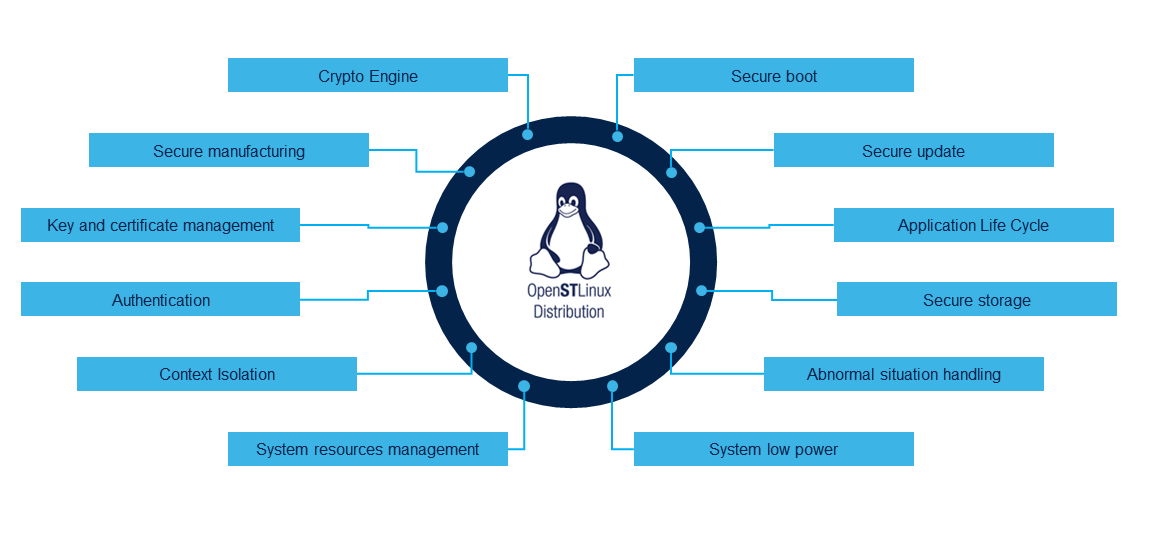
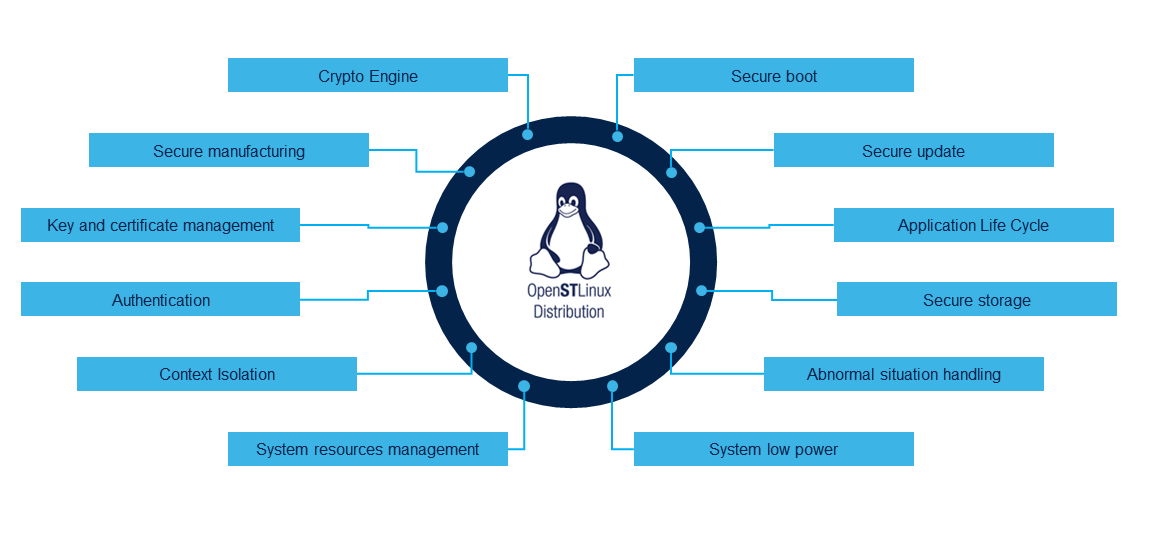
OpentSTLinux distribution is following the STM32Trust[1]
reference by integrating by default some security and secure system functionalities.
Click on the following figure to explore them.
| Applicable for | STM32MP13x lines, STM32MP15x lines, STM32MP21x lines, STM32MP23x lines, STM32MP25x lines |
OpentSTLinux distribution is following the STM32Trust[1]
reference by integrating by default some security and secure system functionalities.
Click on the following figure to explore them.
Discover STM32 application processors and get ready with industry 4.0 on st.com site
If you have any question or request concerning this wiki or if you see some pages with some mistake, you can report them using ST Support Center or ST Community MPU Forum.