Registered User m (Remove comments) |
Registered User Tag: 2017 source edit |
||
| (177 intermediate revisions by 10 users not shown) | |||
| Line 1: | Line 1: | ||
{{ApplicableFor | |||
{{ | |MPUs list=STM32MP13x, STM32MP15x, STM32MP23x, STM32MP25x | ||
|MPUs checklist=STM32MP13x, STM32MP15x, STM32MP23x, STM32MP25x | |||
}} | |||
== Purpose == | == Purpose == | ||
Secure boot is a key feature to guarantee a secure platform. <br><br /> | Secure boot is a key feature to guarantee a secure platform. <br><br/> | ||
[[ | [[Boot_chain_overview|STM32MPU boot sequence]] supports a trusted boot chain that ensures that the loaded images are authenticated and checked in integrity before being used. | ||
{{Warning| The secure boot feature availability is | {{Warning| The secure boot feature availability is limited to the {{MicroprocessorDevice | device=13 | security=Advanced}}, {{MicroprocessorDevice | device=15 | security=Advanced}} and {{MicroprocessorDevice | device=25 | security=Advanced}}.}} | ||
When the chip is [[Device_life_cycle|'''secured unlocked''']] the secure boot is '''not enforced''', this means that: | |||
* authentication and integrity are not ensured | |||
* authentication is not mandatory | |||
* when required, the authentication may fail | |||
* an image may be encrypted but not authenticated | |||
The ROM code logs error and goes on processing until it jumps to FSBL. | |||
The goal is to help developers to debug the secure boot chain. | |||
When the chip is [[Device_life_cycle|'''secured locked''']], the secure boot is '''enforced''', this means that: | |||
* authenticity and integrity are ensured | |||
* authentication is mandatory | |||
* only authenticated images may be encrypted | |||
For details about secure boot features on {{MicroprocessorDevice | device=13}} and {{MicroprocessorDevice | device=2}} see [[#Secure_boot_on_STM32MP13x_lines_and_STM32MP2_series|Secure boot on STM32MP13 lines and STM32MP2 series]]<br> | |||
[[File: | For details about secure boot features on {{MicroprocessorDevice | device=15}} see [[#Secure_boot_on_STM32MP15x_lines|Secure boot on STM32MP15 lines]]<br> | ||
For details about the closing and setup of the chip for enforced secure boot see [[#Operating guidances|Operating guidances]] | |||
== Secure boot on {{MicroprocessorDevice | device=13}} and {{MicroprocessorDevice | device=2}} == | |||
=== Overview === | |||
STM32 MPU provides authentication processing with ECDSA <ref>https://en.wikipedia.org/wiki/Elliptic_Curve_Digital_Signature_Algorithm</ref> verification algorithm, based on ECC <ref>https://en.wikipedia.org/wiki/Elliptic-curve_cryptography</ref>. ECDSA offers better result than RSA with a smaller key. STM32 MPU relies on a 256 bits ECDSA key.<br> | |||
[[File:STM32MP21 secure boot full.png|center|810x810px]] | |||
The figure above shows the steps implied in secure boot: | |||
# [[#Keys generation|Keys generation]] | |||
# [[#Keys registration|Keys registration]] | |||
# Image [[#Image encryption|encryption]] and [[#Image signing|signing]] | |||
# [[#Image authentication |Image authentication with key revocation and version anti-rollback]] | |||
# [[#Image decryption|Image decryption]] | |||
=== Keys generation === | |||
The first step is to generate the necessary keys with [[KeyGen_tool|STM32 KeyGen tool]]. | |||
'''Authentication keys'''<br> | |||
:* The [[KeyGen_tool|STM32 KeyGen tool]] generates eight ECC pair of keys that are used to sign the images. <br> | |||
:* The [[KeyGen_tool|STM32 KeyGen tool]] also generates a file containing the hash of the table of eight (algo+public key) hashes (*PKHTH*) that are used to authenticate the public key on the target. | |||
'''Encryption / Decryption key'''<br> | |||
:* The [[KeyGen_tool|STM32 KeyGen tool]] generates the encryption/decryption master key (EDMK) that is used to derive the decryption key used to encrypt and decrypt the image payload. | |||
<center> | |||
{| class="st-table" | |||
|+ | |||
! | |||
!{{MicroprocessorDevice | device=13}} | |||
!{{MicroprocessorDevice | device=21}} | |||
!{{MicroprocessorDevice | device=23}}and {{MicroprocessorDevice | device=25}} | |||
|- | |||
|'''ECC keys''' | |||
|Private key: 256 bits | |||
Public keys: 512 bits | |||
(brainpool256T1, P-256 NIST) | |||
|Private key: 256 or 384 bits | |||
Public keys: 512 or 768 bits | |||
(brainpool256T1, P-256 NIST, brainpool384T1 or P-384 NIST) | |||
|Private key: 256 bits | |||
Public key: 512 bits | |||
(brainpool256T1 or P-256 NIST) | |||
|- | |||
|'''PKHTH''' | |||
|256 bits | |||
|256 bits | |||
|256 bits | |||
|- | |||
|'''EDMK''' | |||
|128 bits | |||
|128 or 256 bits | |||
|128 bits | |||
|} | |||
</center> | |||
=== | === Keys registration === | ||
PKHTH and EDMK shall be stored in BSEC non volatile memory (OTP words). | |||
Table below shows which OTP shall be used, depending on the serie. | |||
==== | <center> | ||
{| class="st-table" | |||
|+ | |||
! rowspan="2" | | |||
! rowspan="2" style="vertical-align:top;text-align:left;" |{{MicroprocessorDevice | device=13}} | |||
! colspan="2" style="vertical-align:top;text-align:center;" |{{MicroprocessorDevice | device=21}} | |||
! colspan="2" style="vertical-align:middle;text-align:center;" |{{MicroprocessorDevice | device=23}}and {{MicroprocessorDevice | device=25}} | |||
|- | |||
! style="vertical-align:middle;text-align:center;" |BOOTROM_CONFIG_8.oem_key2_enable | |||
(OTP WORD 17 bit 8) | |||
= 0 | |||
! style="vertical-align:middle;text-align:center;" |BOOTROM_CONFIG_8.oem_key2_enable | |||
(OTP WORD 17 bit 8) | |||
= 1 | |||
! style="vertical-align:middle;text-align:center;" |BOOTROM_CONFIG_8.oem_key2_enable | |||
(OTP WORD 17 bit 8) | |||
= 0 | |||
! style="vertical-align:middle;text-align:center;" |BOOTROM_CONFIG_8.oem_key2_enable | |||
(OTP WORD 17 bit 8) | |||
= 1 | |||
|- | |||
|'''PKHTH''' | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP13_OTP_mapping#PKHTH|OTP WORD 24 to 31]] | |||
| style="vertical-align:middle;text-align:center;" |N/A | |||
| style="vertical-align:middle;text-align:center;" |N/A | |||
| style="vertical-align:middle;text-align:center;" |N/A | |||
| style="vertical-align:middle;text-align:center;" |N/A | |||
|- | |||
|'''PKHTH for FSBL-A''' | |||
| style="vertical-align:middle;text-align:center;" |N/A | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP21_OTP_mapping#OEM_KEY1_ROT0|OEM_KEY1_ROT<br>(OTP WORD 152 to 159)]] | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP21_OTP_mapping#OEM_KEY1_ROT0|OEM_KEY1_ROT<br>(OTP WORD 152 to 159)]] | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP23-25_OTP_mapping#OEM_KEY1_ROT|OEM_KEY1_ROT<br>(OTP WORD 144 to 151)]] | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP23-25_OTP_mapping#OEM_KEY1_ROT|OEM_KEY1_ROT<br>(OTP WORD 144 to 151)]] | |||
|- | |||
|'''PKHTH for FSBL-M''' | |||
| style="vertical-align:middle;text-align:center;" |N/A | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP21_OTP_mapping#OEM_KEY1_ROT0|OEM_KEY1_ROT<br>(OTP WORD 152 to 159)]] | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP21_OTP_mapping#OEM_KEY2_ROT0|OEM_KEY2_ROT<br>(OTP WORD 160 to 167)]] | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP23-25_OTP_mapping#OEM_KEY1_ROT|OEM_KEY1_ROT<br>(OTP WORD 144 to 151)]] | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP23-25_OTP_mapping#OEM_KEY2_ROT|OEM_KEY2_ROT<br>(OTP WORD 152 to 159)]] | |||
|- | |||
|'''EDMK''' | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP13_OTP_mapping#EDMK|OTP WORD 92 to 95]] | |||
| style="vertical-align:middle;text-align:center;" |N/A | |||
| style="vertical-align:middle;text-align:center;" |N/A | |||
| style="vertical-align:middle;text-align:center;" |N/A | |||
| style="vertical-align:middle;text-align:center;" |N/A | |||
|- | |||
|'''EDMK for FSBL-A''' | |||
| style="vertical-align:middle;text-align:center;" |N/A | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP21_OTP_mapping#OEM_KEY1_EDMK0|OEM_KEY1_EDMK<br>(OTP WORD 356 to 363)]] | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP21_OTP_mapping#OEM_KEY1_EDMK0|OEM_KEY1_EDMK<br>(OTP WORD 356 to 363)]] | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP23-25_OTP_mapping#OEM_KEY1_EDMK|OEM_KEY1_EDMK<br>(OTP WORD 364 to 367)]] | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP23-25_OTP_mapping#OEM_KEY1_EDMK|OEM_KEY1_EDMK<br>(OTP WORD 364 to 367)]] | |||
|- | |||
|'''EDMK for FSBL-M''' | |||
| style="vertical-align:middle;text-align:center;" |N/A | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP21_OTP_mapping#OEM_KEY1_EDMK0|OEM_KEY1_EDMK<br>(OTP WORD 356 to 363)]] | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP21_OTP_mapping#OEM_KEY2_EDMK0|OEM_KEY2_EDMK<br>(OTP WORD 348 to 355)]] | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP23-25_OTP_mapping#OEM_KEY1_EDMK|OEM_KEY1_EDMK<br>(OTP WORD 364 to 367)]]. | |||
| style="vertical-align:middle;text-align:center;" |[[STM32MP23-25_OTP_mapping#OEM_KEY2_EDMK|OEM_KEY2_EDMK<br>(OTP WORD 360 to 363)]] | |||
|} | |||
</center> | |||
===Image signing=== | |||
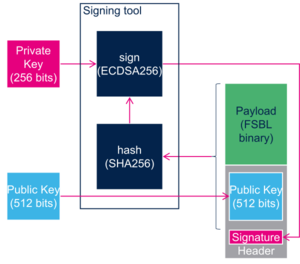
[[File:STM32MP21 image signing.png|right|500x500px]] | |||
*Eight signing keys available. | |||
*Public Keys are hashed and this table of hashes is stored in the [[STM32 header for binary files|header]]. | |||
*Each key is identified by its index in the table. | |||
*The index of the key used for signing, the activate key index, are stored in the [[STM32 header for binary files|header]]. | |||
*Using a key revokes all the keys with lower index. | |||
*All series support ECDSA algorithms : | |||
**P-256 NIST | |||
**Brainpool 256T1 | |||
* In addition {{MicroprocessorDevice|device=21}}supports: | |||
** P-384 NIST | |||
**Brainpool 384T1 | |||
: (The ECDSA algorithm is stored in the [[STM32 header for binary files|header]]) | |||
<br clear="all"> | |||
===Image authentication=== | |||
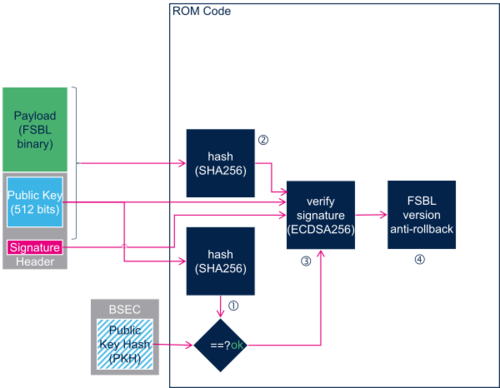
[[File:STM32MP21 image authentication.png|right|500x500px]] | |||
The EDCSA verification follows the process below:<br> | |||
#The ROM code computes the SHA256 hash of the Table of Public Hashes available in the [[STM32 header for binary files|header]]. | |||
#Then, it compares this hash with the one stored in BSEC non-volatile memory in [[STM32 MPU ROM code secure boot#Keys registration|PKHTH]]. If it is different, the authentication process fails, otherwise it continues. | |||
# The ROM code computes the SHA256 hash of the “Public key” available in the signed file<ref group="Note">"Public key" hash is in fact the hash of (Algorithm id + Public key)</ref>. | |||
#Then, it checks this “Public key”: | |||
#* It checks that the active key index stored in the [[STM32 header for binary files|header]] is greater or equal to the "min active key index" stored in BSEC non-volatile memory. If this is not the case, the authentication process fails, otherwise it continues<br> | |||
#*It compares the hash of of the “Public key” previously computed to the one corresponding to the active key index in the Table of Public Hashes. If it is different, the authentication process fails, otherwise it continues | |||
#The ROM code computes the SHA256 of the FSBL payload plus the file [[STM32 header for binary files|header]]. | |||
#It uses the “Public key” that has just been authenticated to verify that the signature stored in the [[STM32 header for binary files|header]] is a valid signature of this hash. If the verification fails, then the authentication process fails, otherwise the authentication is successful and the ROM code goes on with the boot process. | |||
#The ROM code ends the authentication process by if needed, updating the "min active key index" and the "min FSBL version" in the BSEC non volatile memory. | |||
#;Key revocation:The "min active key index" stored in [[STM32MP13_OTP_mapping#signing key id monotonic counter| OTP WORD 22]] on {{MicroprocessorDevice | device=13}} and [[STM32MP2_OTP_mapping#signing key id monotonic counter| OTP WORD 17]] or [[STM32MP2_OTP_mapping#signing key id monotonic counter| OTP WORD 22]] on {{MicroprocessorDevice | device=2}} is updated if the active key index that was used is greater that it. | |||
#;Anti rollback:The ROM code checks that the FSBL version contained in the [[STM32 header for binary files|header]] is greater or equal to the "min FSBL version" stored in [[STM32MP13_OTP_mapping#version monotonic counter| OTP WORD 4]] on {{MicroprocessorDevice | device=13}} or [[STM32MP2_OTP_mapping#version monotonic counter| OTP WORD 12]] or [[STM32MP2_OTP_mapping#version monotonic counter| OTP WORD 19]] on {{MicroprocessorDevice | device=2}}. If not the authentication process fails, otherwise the ROM code updates the "min FSBL version" and continues the boot process. | |||
<references group="Note" /> | |||
The | ===Image encryption=== | ||
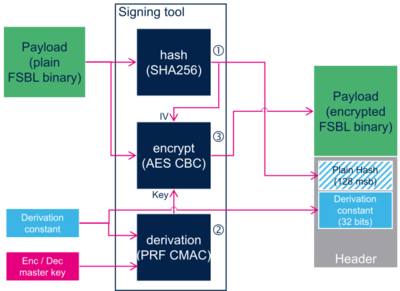
[[File:STM32MP13 image encryption.png|right|400x400px]] | |||
#The host calculates the SHA256 hash of FSBL binary, and stores the 128 most significant bits of it in the [[STM32 header for binary files|header]]. | |||
#The host calculates the PRF CMAC derivation of the Encryption Decryption Master Key ([[STM32 MPU ROM code secure boot#Keys registration|EDMK]]) with a derivation constant to generate the encryption key, and stores the derivation constant in the [[STM32 header for binary files|header]]. | |||
#The host uses the encryption key to encrypt the FBSL binary with AES algorithm. AES Initial Vector (IV) consists in the 128 most significant bits of the hash. | |||
<br clear="all"> | |||
=== Image | ===Image decryption=== | ||
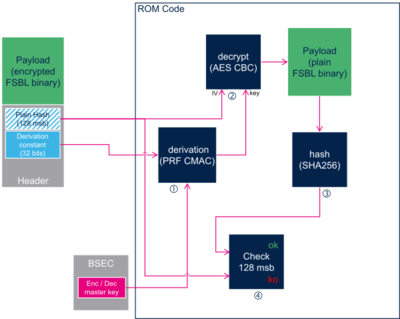
[[File:STM32MP13_image_decryption.png |right|400px]] | |||
#The ROM code calculates the PRF CMAC derivation of the Encryption Decryption Master Key ([[STM32 MPU ROM code secure boot#Keys registration|EDMK]]) stored in [[BSEC_internal_peripheral|BSEC]] non-volatile memory, with the derivation constant stored in the [[STM32 header for binary files|header]], and obtains the decryption key. | |||
#The ROM code uses the decryption key to decrypt the FBSL binary with AES algorithm. AES Initial Vector (IV) consists in the 128 most significant bits of plain image hash stored in the [[STM32 header for binary files|header]]. | |||
#The ROM code calculates the SHA256 hash of the plain FSBL binary, | |||
#The ROM code compares the 128 most significant bits of this hash with the ones stored in the [[STM32 header for binary files|header]] , if the verification fails, then the decryption process fails, otherwise the decryption is successful, and the ROM code goes on with the boot process. | |||
<br clear="all"> | |||
Note that as shown in "Image encryption" figure above the decryption process is optional and when enabled always occurs on an authenticated image. | |||
==Secure boot on {{MicroprocessorDevice | device=15}}== | |||
=== | === Overview=== | ||
STM32 MPU provides authentication processing with ECDSA <ref>https://en.wikipedia.org/wiki/Elliptic_Curve_Digital_Signature_Algorithm</ref> verification algorithm, based on ECC <ref>https://en.wikipedia.org/wiki/Elliptic-curve_cryptography</ref>. ECDSA offers better result than RSA with a smaller key. STM32 MPU relies on a 256 bits ECDSA key.<br> | |||
= | [[File:STM32MP15_secure_boot_full.png|810px|center|link=]] | ||
The figure above shows the steps implied in secure boot: | |||
#[[#Keys generation|Keys generation]] | |||
#[[#Keys registration|Keys registration]] | |||
#Image [[#Image signing|signing]] | |||
# | |||
[[#Image authentication |Image authentication]] | |||
===Keys generation=== | |||
The first step is to generate the necessary keys with [[KeyGen_tool|STM32 KeyGen tool]]. | |||
The [[ | '''Authentication keys'''<br> | ||
:*The [[KeyGen_tool|STM32 KeyGen tool]] generates one ECC pair of keys that is used to sign the images. <br> | |||
:*The [[KeyGen_tool|STM32 KeyGen tool]] tool also generates a third file containing the public key hash (PKH) that is used to authenticate the public key on the target.<br> | |||
=== | === Keys registration=== | ||
*PKH shall be stored in [[STM32MP15_OTP_mapping#PKH|OTP WORD 24 to 31]]. | |||
===Image signing=== | |||
[[File:STM32MP15_image_signing.png |right|300px]] | |||
*Only one signing key available. | |||
*The public key is stored in the [[STM32 header for binary files|header]]. | |||
*Two algorithms supported for ECDSA calculation. The algorithm is in the [[STM32 header for binary files|header]] | |||
**P-256 NIST | |||
**Brainpool 256 T1 | |||
<br clear="all"> | |||
< | ===Image authentication=== | ||
The EDCSA verification follows the process below:<br> | |||
< | [[File:STM32MP15_image_authentication.png |right|500px]] | ||
#The ROM code computes the SHA256 hash of the “Public key” available in the signed file. Then, it compares this hash with the one stored in STM32MP1 BSEC non-volatile memory in [[STM32MP15_OTP_mapping#PKH|OTP WORD 24 to 31]] , if different, the authentication process fails, otherwise it continues. | |||
#The ROM code computes the SHA256 of the FSBL payload plus the “Public key” and the file [[STM32 header for binary files|header]]. | |||
#It uses the “Public key” that has just been authenticated to verify that the signature stored in the [[STM32 header for binary files|header]] is a valid signature of this hash, if the verification fails, then the authentication process fails, otherwise the authentication is successful and the ROM code goes on with the boot process. | |||
#The ROM code checks that the FSBL version contained in the [[STM32 header for binary files|header]] is greater or equal to the "min FSBL version" stored in [[STM32MP15_OTP_mapping#version monotonic counter| OTP WORD 4]], if not the authentication process fails, otherwise the ROM code continues the boot process. | |||
<br clear="all"> | |||
==Operating guidances== | |||
{{Warning| Make sure that a device with Secure boot enabled is used. This is available on {{MicroprocessorDevice | device=13 | security=Advanced}}, {{MicroprocessorDevice | device=15 | security=Advanced}} and {{MicroprocessorDevice | device=25 | security=Advanced}}, otherwise the device becomes permanently unusable.}} | |||
The needed keys file is generated using [[KeyGen_tool|STM32 KeyGen tool]]. | |||
The files are signed with [[Signing_tool|STM32 Signing tool]]. | |||
The secure provisioning on the board of the needed keys in the associated OTPs are done directly by the end-user application or with [[Secure Secret Provisioning (SSP) overview|Secure Secret Provisioning (SSP)]]. | |||
[[ | When the device is '''secured locked''' as explained in [[Device_life_cycle|Life cycle]], the ROM accepts only authenticated images. It is locked by blowing the appropriate fuses as described in the [[Device_life_cycle#Encoding_life_cycle| life cycle table]]. | ||
See [[How to use U-Boot stm32key command]] for examples of secure boot activation without SSP. | |||
On secured locked device if the authentication fails, the ROM code enters into a serial boot loop indicated by the blinking Error LED (cf [[STM32 MPU ROM code overview#Common debug and error cases|ROM code common debug and error cases]]). | |||
<references/> | ==References== | ||
<references /> | |||
<noinclude> | <noinclude> | ||
[[Category:ROM code|02]] | [[Category:ROM code|02]] | ||
{{PublicationRequestId | 10394 | [[Category:Secure boot]] | ||
{{PublicationRequestId | 24126 |2022-07-27 | Previous TW review : 10394 2019-01-30 BrunoB }} | |||
</noinclude> | </noinclude> | ||
Latest revision as of 13:58, 11 March 2025
1. Purpose[edit | edit source]
Secure boot is a key feature to guarantee a secure platform.
STM32MPU boot sequence supports a trusted boot chain that ensures that the loaded images are authenticated and checked in integrity before being used.
When the chip is secured unlocked the secure boot is not enforced, this means that:
- authentication and integrity are not ensured
- authentication is not mandatory
- when required, the authentication may fail
- an image may be encrypted but not authenticated
The ROM code logs error and goes on processing until it jumps to FSBL. The goal is to help developers to debug the secure boot chain.
When the chip is secured locked, the secure boot is enforced, this means that:
- authenticity and integrity are ensured
- authentication is mandatory
- only authenticated images may be encrypted
For details about secure boot features on STM32MP13x lines ![]() and STM32MP2 series see Secure boot on STM32MP13 lines and STM32MP2 series
and STM32MP2 series see Secure boot on STM32MP13 lines and STM32MP2 series
For details about secure boot features on STM32MP15x lines ![]() see Secure boot on STM32MP15 lines
see Secure boot on STM32MP15 lines
For details about the closing and setup of the chip for enforced secure boot see Operating guidances
2. Secure boot on STM32MP13x lines  and STM32MP2 series[edit | edit source]
and STM32MP2 series[edit | edit source]
2.1. Overview[edit | edit source]
STM32 MPU provides authentication processing with ECDSA [1] verification algorithm, based on ECC [2]. ECDSA offers better result than RSA with a smaller key. STM32 MPU relies on a 256 bits ECDSA key.
The figure above shows the steps implied in secure boot:
- Keys generation
- Keys registration
- Image encryption and signing
- Image authentication with key revocation and version anti-rollback
- Image decryption
2.2. Keys generation[edit | edit source]
The first step is to generate the necessary keys with STM32 KeyGen tool.
Authentication keys
- The STM32 KeyGen tool generates eight ECC pair of keys that are used to sign the images.
- The STM32 KeyGen tool generates eight ECC pair of keys that are used to sign the images.
- The STM32 KeyGen tool also generates a file containing the hash of the table of eight (algo+public key) hashes (*PKHTH*) that are used to authenticate the public key on the target.
Encryption / Decryption key
- The STM32 KeyGen tool generates the encryption/decryption master key (EDMK) that is used to derive the decryption key used to encrypt and decrypt the image payload.
2.3. Keys registration[edit | edit source]
PKHTH and EDMK shall be stored in BSEC non volatile memory (OTP words).
Table below shows which OTP shall be used, depending on the serie.
2.4. Image signing[edit | edit source]
- Eight signing keys available.
- Public Keys are hashed and this table of hashes is stored in the header.
- Each key is identified by its index in the table.
- The index of the key used for signing, the activate key index, are stored in the header.
- Using a key revokes all the keys with lower index.
- All series support ECDSA algorithms :
- P-256 NIST
- Brainpool 256T1
- In addition STM32MP21x lines
 supports:
supports:
- P-384 NIST
- Brainpool 384T1
- (The ECDSA algorithm is stored in the header)
2.5. Image authentication[edit | edit source]
The EDCSA verification follows the process below:
- The ROM code computes the SHA256 hash of the Table of Public Hashes available in the header.
- Then, it compares this hash with the one stored in BSEC non-volatile memory in PKHTH. If it is different, the authentication process fails, otherwise it continues.
- The ROM code computes the SHA256 hash of the “Public key” available in the signed file[Note 1].
- Then, it checks this “Public key”:
- It checks that the active key index stored in the header is greater or equal to the "min active key index" stored in BSEC non-volatile memory. If this is not the case, the authentication process fails, otherwise it continues
- It compares the hash of of the “Public key” previously computed to the one corresponding to the active key index in the Table of Public Hashes. If it is different, the authentication process fails, otherwise it continues
- It checks that the active key index stored in the header is greater or equal to the "min active key index" stored in BSEC non-volatile memory. If this is not the case, the authentication process fails, otherwise it continues
- The ROM code computes the SHA256 of the FSBL payload plus the file header.
- It uses the “Public key” that has just been authenticated to verify that the signature stored in the header is a valid signature of this hash. If the verification fails, then the authentication process fails, otherwise the authentication is successful and the ROM code goes on with the boot process.
- The ROM code ends the authentication process by if needed, updating the "min active key index" and the "min FSBL version" in the BSEC non volatile memory.
- Key revocation
- The "min active key index" stored in OTP WORD 22 on STM32MP13x lines
 and OTP WORD 17 or OTP WORD 22 on STM32MP2 series is updated if the active key index that was used is greater that it.
and OTP WORD 17 or OTP WORD 22 on STM32MP2 series is updated if the active key index that was used is greater that it. - Anti rollback
- The ROM code checks that the FSBL version contained in the header is greater or equal to the "min FSBL version" stored in OTP WORD 4 on STM32MP13x lines
 or OTP WORD 12 or OTP WORD 19 on STM32MP2 series. If not the authentication process fails, otherwise the ROM code updates the "min FSBL version" and continues the boot process.
or OTP WORD 12 or OTP WORD 19 on STM32MP2 series. If not the authentication process fails, otherwise the ROM code updates the "min FSBL version" and continues the boot process.
- ↑ "Public key" hash is in fact the hash of (Algorithm id + Public key)
2.6. Image encryption[edit | edit source]
- The host calculates the SHA256 hash of FSBL binary, and stores the 128 most significant bits of it in the header.
- The host calculates the PRF CMAC derivation of the Encryption Decryption Master Key (EDMK) with a derivation constant to generate the encryption key, and stores the derivation constant in the header.
- The host uses the encryption key to encrypt the FBSL binary with AES algorithm. AES Initial Vector (IV) consists in the 128 most significant bits of the hash.
2.7. Image decryption[edit | edit source]
- The ROM code calculates the PRF CMAC derivation of the Encryption Decryption Master Key (EDMK) stored in BSEC non-volatile memory, with the derivation constant stored in the header, and obtains the decryption key.
- The ROM code uses the decryption key to decrypt the FBSL binary with AES algorithm. AES Initial Vector (IV) consists in the 128 most significant bits of plain image hash stored in the header.
- The ROM code calculates the SHA256 hash of the plain FSBL binary,
- The ROM code compares the 128 most significant bits of this hash with the ones stored in the header , if the verification fails, then the decryption process fails, otherwise the decryption is successful, and the ROM code goes on with the boot process.
Note that as shown in "Image encryption" figure above the decryption process is optional and when enabled always occurs on an authenticated image.
3. Secure boot on STM32MP15x lines  [edit | edit source]
[edit | edit source]
3.1. Overview[edit | edit source]
STM32 MPU provides authentication processing with ECDSA [3] verification algorithm, based on ECC [4]. ECDSA offers better result than RSA with a smaller key. STM32 MPU relies on a 256 bits ECDSA key.
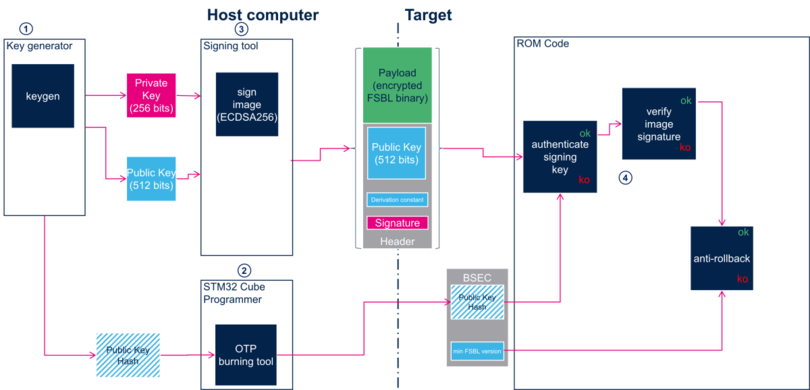
The figure above shows the steps implied in secure boot:
3.2. Keys generation[edit | edit source]
The first step is to generate the necessary keys with STM32 KeyGen tool.
Authentication keys
- The STM32 KeyGen tool generates one ECC pair of keys that is used to sign the images.
- The STM32 KeyGen tool generates one ECC pair of keys that is used to sign the images.
- The STM32 KeyGen tool tool also generates a third file containing the public key hash (PKH) that is used to authenticate the public key on the target.
- The STM32 KeyGen tool tool also generates a third file containing the public key hash (PKH) that is used to authenticate the public key on the target.
3.3. Keys registration[edit | edit source]
- PKH shall be stored in OTP WORD 24 to 31.
3.4. Image signing[edit | edit source]
- Only one signing key available.
- The public key is stored in the header.
- Two algorithms supported for ECDSA calculation. The algorithm is in the header
- P-256 NIST
- Brainpool 256 T1
3.5. Image authentication[edit | edit source]
The EDCSA verification follows the process below:
- The ROM code computes the SHA256 hash of the “Public key” available in the signed file. Then, it compares this hash with the one stored in STM32MP1 BSEC non-volatile memory in OTP WORD 24 to 31 , if different, the authentication process fails, otherwise it continues.
- The ROM code computes the SHA256 of the FSBL payload plus the “Public key” and the file header.
- It uses the “Public key” that has just been authenticated to verify that the signature stored in the header is a valid signature of this hash, if the verification fails, then the authentication process fails, otherwise the authentication is successful and the ROM code goes on with the boot process.
- The ROM code checks that the FSBL version contained in the header is greater or equal to the "min FSBL version" stored in OTP WORD 4, if not the authentication process fails, otherwise the ROM code continues the boot process.
4. Operating guidances[edit | edit source]
The needed keys file is generated using STM32 KeyGen tool.
The files are signed with STM32 Signing tool.
The secure provisioning on the board of the needed keys in the associated OTPs are done directly by the end-user application or with Secure Secret Provisioning (SSP).
When the device is secured locked as explained in Life cycle, the ROM accepts only authenticated images. It is locked by blowing the appropriate fuses as described in the life cycle table.
See How to use U-Boot stm32key command for examples of secure boot activation without SSP.
On secured locked device if the authentication fails, the ROM code enters into a serial boot loop indicated by the blinking Error LED (cf ROM code common debug and error cases).
5. References[edit | edit source]