1. Article purpose[edit source]
To meet the new market security requests and protect customers against any leakage of their IPs, STMicroelectronics introduces a security feature, the secure secret provisioning (SSP), allowing the OEM secrets programming into STM32 MPU one time programming (OTP) area in a secure way (with confidentiality, authentication and integrity checks).The STM32MP1 series supports protection mechanisms that allows the protection of critical operations (such as cryptography algorithms) and critical data (such as secret keys) against unexpected access.
This wiki gives an overview of the STM32MP1 series SSP solution with its associated tools ecosystem.
2. SSP overview[edit source]
The SSP is a secure system mechanism implemented in STM32 microprocessors that allows secured and counted
installation of OEM secrets in untrusted production environment (such the OEM contract manufacturer).
The SSP process prevents the OEM secrets from:
- being accessed by the contract manufacturer.
- being extracted or disclosed.
- being over produced.
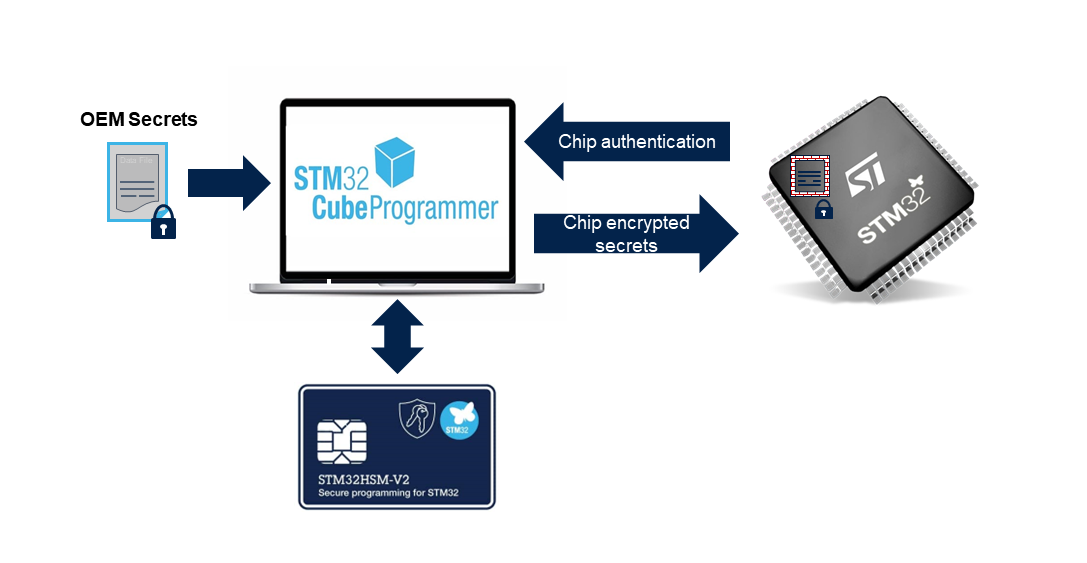
Following the STM32 MCU SFI strategy, the SSP processing relies on an STM32 Hardware Security Module[1] (HSM) to manage chip authentication and and to unwarily encrypt exchange data with STM32 chip. The chip authentication allows to count the number of provisioned devices. The STM32 HSM is connected to the programing tool (STM32CubeProgrammer presented as an example) that uploads the encrypted data to the chip.
3. SSP embedded software implementation[edit source]
The SSP chip implementation relies on two embedded software parts:
- The ROM code SSP.
- A TF-A BL2 based SSP dedicated firmware.
3.1. ROM Code SSP implementation[edit source]
The ROM code has a complete access to chip data. During the SSP process, it is in charge of:
- Generating the chip certificate.
- Connecting to programming tool via serial interface binary loading.
- Downloading the TF-A SSP Firmware in SYSRAM from serial interface.
- Decrypting the secret data.
- Authenticating the TF-A SSP Firmware.
- Executing TF-A SSP
3.2. TF-A SSP firmware[edit source]
The TF-A BL2 SSP Firmware is a specific code that extends the communication with the programming tool and is in charge of specific SSP commands, it:
- Initializes the SSP process by changing the chip life cycle state.
- Sends the ROM code prepared chip certificate to the programming tool to allow chip authentication.
- Receives the secret data binary from the programming tool and store it in a dedicated secure memory region for the ROM code.
- Writes all the decrypted secrets in the chip OTP and sets the chip to CLOSE SECURE state.
This part of code is using part of TF-A BL2 generic code but is only restricted to serial connection mode and OTP access. The TF-A SSP size is limited to the minimum but required a dedicated board configuration (over device tree).
4. SSP STM32 tools[edit source]
Trusted Package Creator offers a way to:
- Generate OEM keys.
- Provision the ST HSMv2 card
- Generate secret file (coming soon)
This is an essential tool for the OEM to manage a complete encrypted secret package and customize the HSMv2 to the untrusted manufacturer.
5. Running the SSP process[edit source]
The SSP required different stages:
- At OEM level:
- Generate OEM keys
- HSM provisioning
- Generate secret files
- Customize TF-A BL2 SSP firmware
- Sign the TF-A BL2 SSP firmware.
- At untrusted manufacturer level
- Set the chip in SSP provisioning state.
- Send the encrypted data to the chip.
A dedicated page how to deploy SSP: a step-by-step approach explains how to configure and run a complete SSP process.
6. References[edit source]