STM32H5 was designed to radically improve STM32 security, taking into account experience with previous Cortex-M33 microcontrollers, customer feedback and requirements to achieve highest PSA certification levels. This article is intended for readers who already know previous STM32 MCU's and their security features and want to focus on the specific updates and changes introduced to STM32H5.
For general STM32 security see this article or AN5156.
For more details on each particular security topic, there is more documentation to study, the product reference manual, user manuals and application notes.
There are 3 distinct STM32H5 lines:
| STM32H5 MCU line | Security features |
|---|---|
| STM32H503 | Product state management with provisioning, temporal isolation, boot lock, write protection |
| STM32H563 | STM32H503 + TrustZone |
| STM32H573 | STM32H563 + Cryptography, SAES and secure (key) storage |
This article focuses on the most featured sales type, but important differences in the former two will be highlighted.
1. Secure hardware architecture (SBS)
In contrast to STM32L5 and STM32U5 the security configuration is now concentrated around protected registers in the SBS (system configuration, boot and security) block. Concentrating the security related configuration to a single place reduces the attack surface and makes the protection more efficient.
This block takes care of:
- system configuration - including register access control
- boot control - interpreting settings from option bytes an managing the temporal isolation
- debug control - making sure only legitimate debug access is allowed
- hardware storage control - managing the secure storage components (EPOCH, SAES, OBK, HUK)
2. Product state
Product state is a system that replaces the old RDP (read protection) mechanism of life cycle management. The STM32L5 introduced the RDP0.5 and the STM32U5 also the much needed rollback mechanism for debug authentication, but more radical change was necessary.
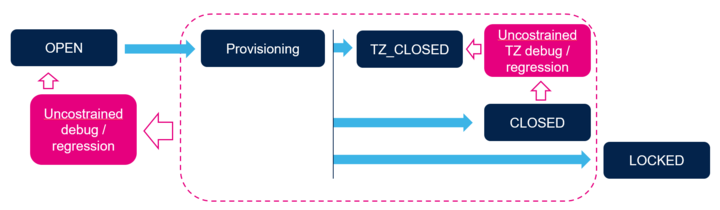
The new basic progression now looks like this:
| Product state | Description | Transitions possible |
|---|---|---|
| Open | State intended for unrestricted development. HUK is hidden, user is free to experiment | Provisioning, Provisioned |
| Provisioning (and Provisioned) | States in which no development is possible, used just to establish security | Closed, Locked, TZ-Closed, Regression |
| TZ-Closed | State in which secure environment is fixed in place and developers work only with the non-secure domain | Regression, Closed, Locked |
| Closed | Final product delivery state - no debug access is possible | Regression |
| Locked | As closed, but with no chance for regression (as old RDP2) | none |
| Regression (or NS-Regression) | Process of reopening for debug | Open or TZ-Closed, depending on regression type |
One thing to note is that there is no direct equivalent to the RDP1 in the new scheme. RDP1 was not suitable for development, nor good enough for serious protection.
ST delivers the microcontroller in the Open state. It's possible to freely manipulate option bytes, including the TrustZone enable, to facilitate for easy development and testing, down to HDP level 1. The limitation is that secure boot and services, the iRoT ( immutable root of trust ) are not fully usable without real HUK and the Secure Manager cannot be installed before provisioning.
The provisioning is used to secure the product and manage the control over the security. This means that the product can be set for example to:
- Regress up to the Open if correct credential is provided
- Regress only to TZ-Closed on different credential
- Temporarily allow full debug with right credentials
- Temporarily allow debug on non-secure part with different credentials
- Create credentials that allow delegating the access to other users
The product itself would only have the root certificate with the max allowed opening installed. All else is configured in the development environment.
3. Temporal isolation (HDP)
Temporal isolation feature has evolved in the STM32H5 significantly. It's still called HDP, but the usability is extended. There are 2 most significant changes:
- The HDP now has 4 level of which 3 are available to the user
- The HDP protected area now can be defined (almost) anywhere in the memory, independent of the secure watermark area
Another novelty is that the HDP is now linked to the Secure Storage ( also referred to as Option Byte Keys, described later).
The HDP levels are:
- Level 0 - only defined in the system flash, never accessible to user, linked to regression control
- Level 1 - Level used by the secure boot, for example iRoT, if ST-iRoT is used, this level is also not user accessible.
- Level 2 - Level used by the later stages of the secure boot, for example uRoT (updatable root of trust)
- Level 3 - Final level in which the product will end up once the secure boot phase is concluded
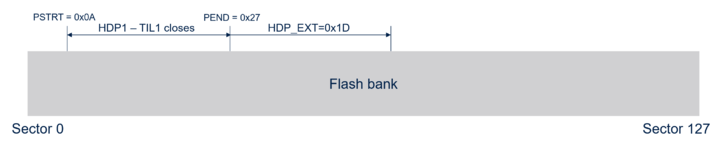
Locking out the lower levels is under the control of the SBS. The option bytes define the start and the end of the HDPL1 reserved area in each flash bank, with sector granularity. Open part of the system flash contains callable function that facilitates the transition. The system service to increase the level will increase the monotonic level counter and jump to the desired address in the Level 2 area.
The threshold between HDPL2 and final HDPL3 is a register value. This is the number of sectors past the end of the HDPL1 lockout area that will also be rendered inaccessible until next reboot. It's volatile and needs to be set every time the transition is needed. The value has dual protection - once set, it cannot ever be decremented and cannot be modified at all once the transition to HDPL3 is done.
4. Secure storage (OBK)
Secure storage is, simply put, a sector of non-volatile memory with special access rules, intended primarily as key storage, though really any data can be stored there. Part of it is reserved for system security management, and part is open to user. Access to the Secure storage is under control of the SBS, linked to the temporal isolation levels. The OBK is not available at all on the STM32H503 and it's limited in protection of the STM32H56x, following description is only accurate in case of the STM32H57x crypto parts. The STM32H57x features SAES, secure AES cryptography IP, which uses HUK (hardware unique key) to encrypt the OBK contents. As the HUK is never disclosed, and never used before provisioning, the storage of the OBK is very safe. To prevent replay attacks, the SAES is also "salting" the HUK with EPOCH counter. EPOCH counters are monotonic, non-volatile counters, incremented on each regression.
5. The secure boot ecosystem
5.1. Selection of boot address
This section is only fully applicable on the crypto parts - the STM32H57x line. The boot lock and the HDP are available on all the STM32H5 series, allowing developers to develop a secure boot system, but without the SAES the security level will be limited. The native ST-iRoT and the subsequent option of the Secure Manager is only an option where full cryptography support exists - in the STM32H57x top line.
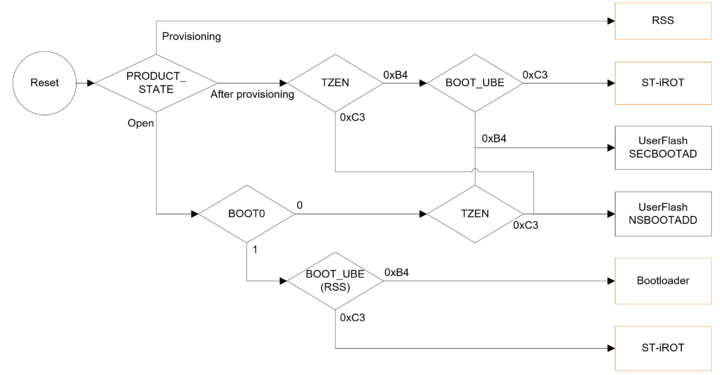
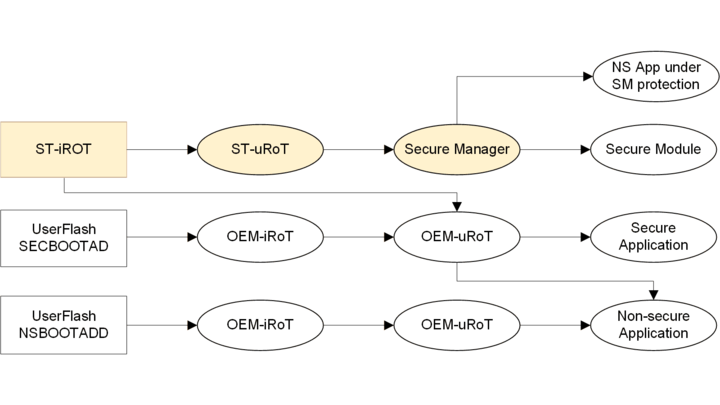
In either case the secure boot is a sequence, starting from a fixed starting point, configured and locked using option bytes. As the secure boot progresses, the basic and immutable firmware ( iRoT - immutable root of trust) will update or validate updatable part of the secure boot progression, called uRoT, updatable root of trust, increasing the HDP temporal isolation to level 2 when giving control to the next chain link. Finally the uRoT will update or execute an application or an operating system, either secure or non-secure, in HDP level 3.
The option bytes determine from which which memory will the device boot. You can see that with default state ( product state Open, TZ disabled, unique boot entry disabled ) the device will use user flash memory in non-secure address range, the 0x0800 0000 starting point common with other STM32 MCUs. It's also possible to use the old-fashioned bootloader. This is also the only option for the STM32H503 devices.
With TrustZone enabled the device starts secure boot procedure. In case of the STM32H57x it evaluates the UBE option byte setting to determine if ST-iRoT is the selected boot option. If not, or on the STM32H56x, the boot continues in user flash memory on secure address range starting 0x0C00 0000, where presumably there's an OEM-iRoT or other secure software of choice. More details are available in Introduction to OEM-iROT on STM32H5 series
From the ST-iRoT the secure boot will also continue to user flash, either using ST installable services (up to the Secure Manager), or to a customized code, from secure boot chain point of view it's a OEM-uRoT.
There are actually two other boot entry point, hidden. One is the Debug authentication, when debugger is connected during reset using dedicated set of debug interface registers it can attempt to reopen the device by initiating the regression.
Lastly, if the device is reset in Provisioning product state, the RSS (root secure services) part of system flash is given control. The sole purpose of it is to finish the provisioning and change to state to the next in the lifecycle. No user code can be executed on the STM32H5 in Provisioning state.
5.2. Secure boot progression in software
Depending on the selected boot address, there are different options for secure boot progression. The upper path leading to the Secure Manager is "golden". It's the path of certified PSA level 3 security, available on STM32H57x crypto line only. More details can be found in the introduction to ST-iROT onSTM32H573. The dashed arrows represent optional divergence, which is available should the product be configured as such. It's always possible to choose customized secure environment. But of course the STM32H56x do not have the option to load Secure Manager and the STM32H503, with TrustZone forced to disabled, only the lowest path is possible.
6. What's missing on the STM32H5
The STM32H5 is the peak in STM32 general purpose microcontroller family security. However coming from other STM32 users can find some security features missing. That's the case of old approach to security being replaced with new and better methods.
- The replacement of RDP (read-out protection) by the PRODUCT_STATE scheme was already covered. There is no direct replacement for RDP1, which allowed to set read protection on the non-volatile memory only with possibility of removal with condition of mass erase. With PRODUCT_STATE, there is no possibility of mass erase of closed product without successful debug authentication.
- PCROP was removed. This extension to RDP stopped even the code running on the device from reading certain areas of internal flash memory. Obviously this feature is redundant with TrustZone and HDP available.
- Firewall was removed. This feature was introduced on the STM32L4 and used extensively in SBSFU. Also replaced by the TrustZone.
7. Changes in the existing security functions
Summary of familiar security features common to STM32 family, and how they appear in the STM32H5.
7.1. MPU
Up to eight MPU regions can be defined with TrustZone deactivated, twelve with TrustZone enabled.
7.2. WRP
Flash write protection is configured in a bitmap fashion, with granularity of 4 sectors (32kB per one bit of configuration). The configuration is entered using OB.
Also the SRAM2 features write protection, bits of write protection configuration each represent 1kB of the total 64kB (or 16kB in case of STM32H503) of the SRAM2 memory.
7.3. OTP
One-time programmable flash memory area is 2kB, programmable by 16bit word at the time. It has a locking mechanism, a separate write protection. Each bit of the locking OB word locks block of 32 OB words from modification.
On the STM32H503 block of the OTP is used to perform the provisioning, storing a HASH of the password needed for regression.
7.4. OTFDEC
The underlying communication interface is now called XSPI, to prevent confusion when more SPI lines are added. This would be universal title for OCTOSPI, QUADSPI, and any other number of lines.
The IP is practically identical to the one used in STM32U5, but the Secure Storage (OBK) expands application possibilities of the external memory. It's possible to use the OBK to store OTFDEC keys and only reveal them in safe condition, improving the overall security.
7.5. AES/SAES
Taking the STM32U5 series as baseline for the comparison, nothing is drastically changed in the AES, only some speed increase. But the SEAS now supports more operation modes and again, the ability to work in close cooperation with the Secure Storage (OBK) is a big improvement for the overall application security.
7.6. PKA
Public key cryptography has more capability compared to the STM32L4Px and STM32L4Qx, providing more functions, with larger keys and with greater resistance to SCA. But the level of capability remains the same as STM32U5, apart of speed increase due to higher clock.
7.7. Tamper
Apart of 8 usual external tamper sources, the STM32H5 allows monitoring up to 15 internal test points with tamper detection, newest addition being the HSE presence guard, enhancing the security already provided by the CSS. There are 32 tamper protected registers of 32 bits. It's the most advanced anti tamper built to STM32 to date.