This message will disappear after all relevant tasks have been resolved.
Semantic MediaWiki
There are 1 incomplete or pending task to finish installation of Semantic MediaWiki. An administrator or user with sufficient rights can complete it. This should be done before adding new data to avoid inconsistencies.1. SFI
1.1. Features
The secure firmware install (SFI) solution provides security when programming devices in a non-trusted facility owned by a Contract Manufacturer (CM).
SFI addresses the two main issues at a non-trusted facility:
- OEM application confidentiality against CM during STM32 programming.
- Avoid CM overproduction of OEM devices.
1.2. Principles
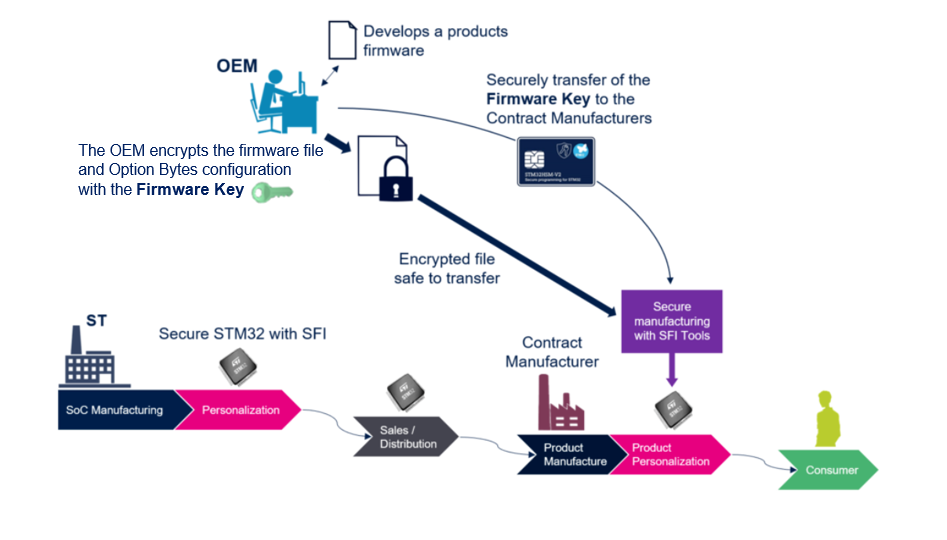
Below is the description of the SFI manufacturing scheme:
- The OEM creates and manages his secret encryption key (the firmware key as indicated in the figure below).
- The OEM encrypts its application and Option bytes configuration with the firmware key. It is the SFI OEM application image (the Encrypted file in the figure below).
- The OEM programs the firmware key within an HSM before locking it. Before that step, the firmware key cannot be read or extracted clearly from the HSM. Only STM32 can handle the firmware key from the HSM.
- The OEM sends the HSM and the SFI OEM application image to the CM facility.
- The CM securely installs the OEM application using SFI tools (including HSM):
- STM32 securely extracts the firmware key from the HSM. HSM verifies the firmware key extraction request number.
- STM32 securely decrypts and programs the OEM application within the internal flash.
- OEM application is never disclosed outside STM32. The SFI process guarantees the OEM application confidentiality against CM.
OEM uses the STM32 Trusted Package Creator software to:
- Encrypt the OEM application (meaning binary files)
- Store its credentials (firmware key and part counter) into STM32-HSM [1].
CM uses the STM32CubeProgrammer (or any other SFI-recommended partner programming tools) to securely program STM32 MCUs in untrusted environments.
2. SFI for STM32H5 with Secure Manager
3. SFI for STM32H5 without Secure Manager
- ↑ Cite error: Invalid
<ref>tag; no text was provided for refs namedHSM