| Coming soon |
Target description
The purpose of this article is to explain how to proceed step by step to generate a boot path using STM32CubeMx.
The example below will show how to configure and provision a boot path for an OEMiROT with a secure and non-secure user application initial code generation.
Read the Secure Boot STM32H5 How to Introduction article before starting the practical example described below.
More technical details you may need to understand this getting started are available in the following articles:
- Introduction article: Introduction to Secure boot and Secure firmware update.
- Specific STM32H5 bootpaths article: Secure Boot for STM32H5
- OEMiROT article OEMiROT for STM32H5
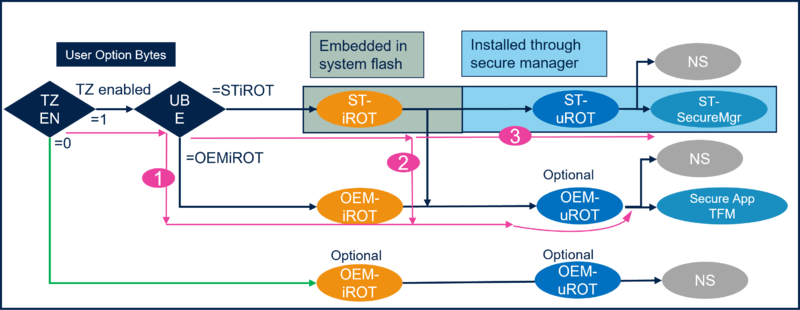
The How to start described in this article is using the Boot path number 1 of the figure below.
Prerequisites
To execute the example described below, you need:
- NUCLEO board: NUCLEO-H563ZI
- The following tools:
- STM32CubeMx_6.9.0 or later (for installation, see appendix)
- IAR Embedded Workbench rev 9.20.1 or later
Note:
- STM32 Trusted Package Creator (TPC) is automatically installed during the STM32CubeMX installation. There is a TPC version dedicated to STM32CubeMX and installed in the STM32CubeMX/utilities folder.
- The latest STM32Cube_FW revision is installed through STM32CubeMX (see appendix)
- If needed set the windows environment variable (see appendix). It is required in case the H5 doesn’t appear in the “Access to MCU Selector” of STM32CubeMx
1. Setting the STM32CubeMX project
Launch STM32CubeMX
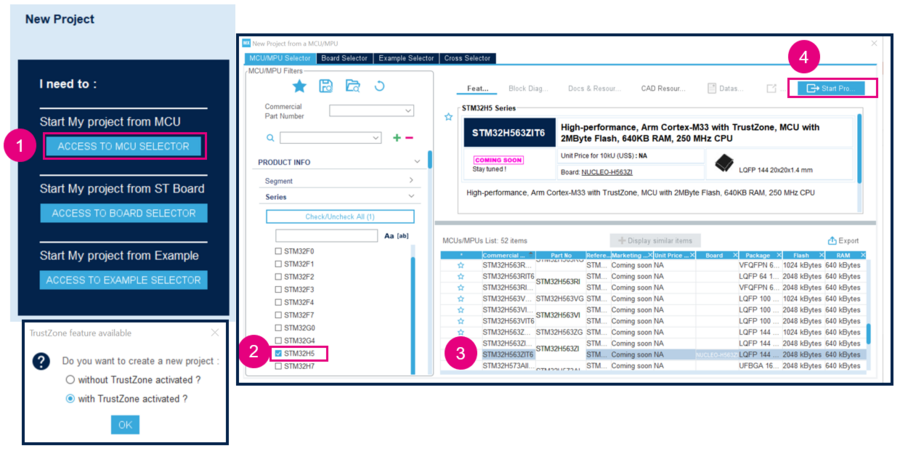
- 1) Click on Access to MCU selector (easier for this example to enable only the needed GPIOs, so it's advised to use the MCU selector instead of the board selector).
- 2) Select STM32H5 serie and select the device used in NUCLEO_H563
- 3) Click start project
- 4) Enable the TrustZone, as shown in the figure 1, for the OEMiROT bootpath the TZ needs to be enabled.
Set the STM32CubeMX project:
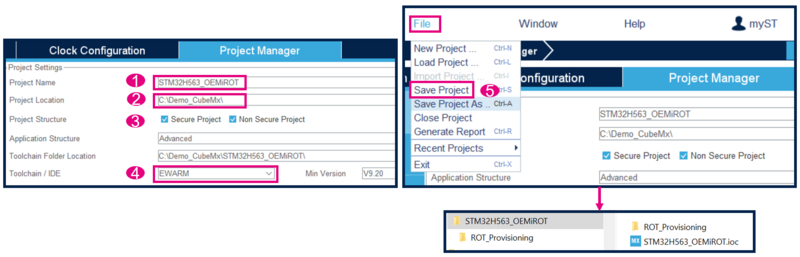
- 1) Type the name of the project (the related folder will be created)
- 2) Chose the folder for this project (avoid long path)
- 3) Tick both: Secure and non Secure projects
- 4) Select the Toolchain, for this example EWARN is used
- 5) File -> Save Project -> the project folder (if not already existing) and the STM32H563_OEMiROT.ioc file is created
2. GPIO configuration
For this proposed example three GPIO need to be configured for the discovery board:
- PF4 for the blue LED used in the secure user application code
- PC13 for the blue user button used in the secure user application code
- PB0 for the green LED used in the non-secure user application code
In the STM32CubeMX select the Pinout & Configuration window
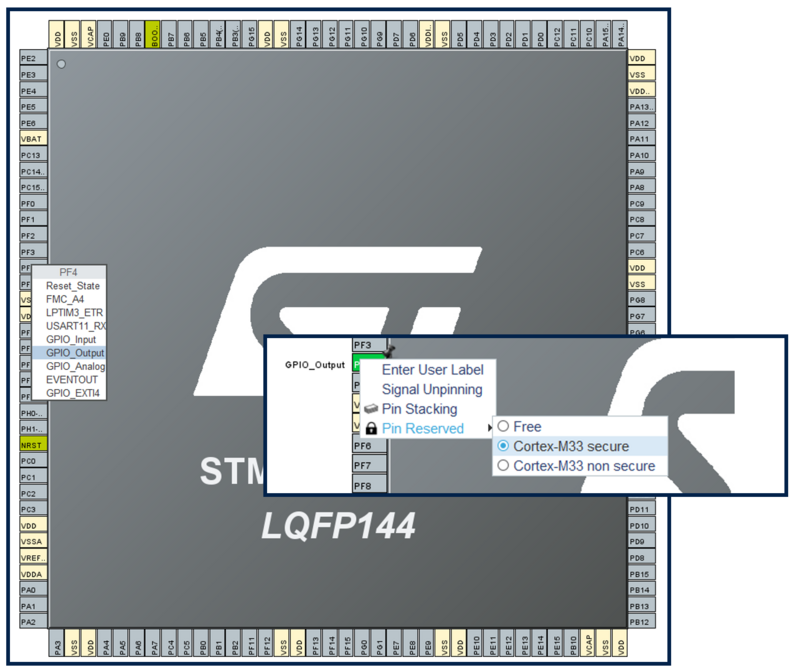
To configure the GPIO for the blue LED proceed as follow:
- Click left on PF4: select GPIO_Output -> a push pull output will be configured need to drive an LED
- Click right on PF4: and select Cortex-M33 secure. This GPIO is then assigned to the secure user application code
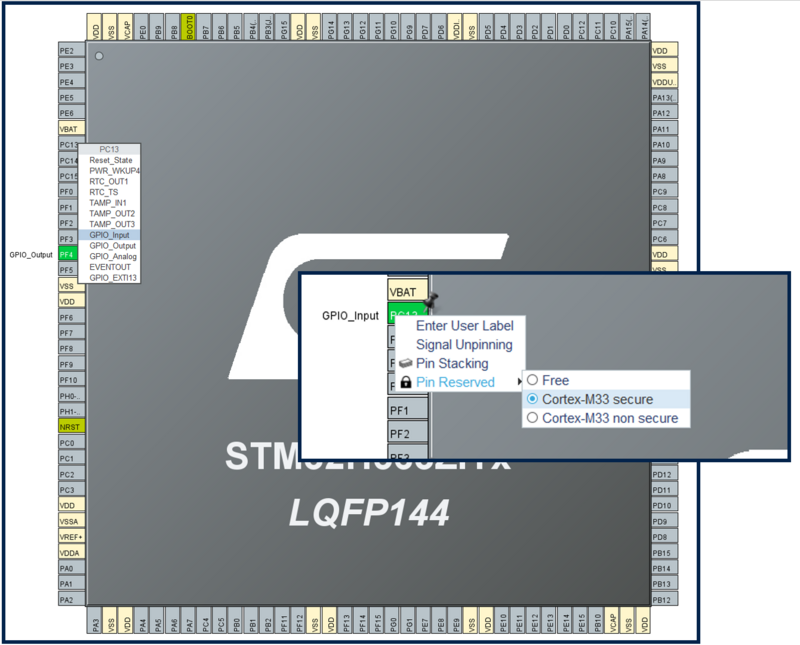
To configure the user bue button proceed as follow:
- Click left on PC13: select GPIO_Input
- Click right on PC13: and select Cortex-M33 secure. This GPIO is then assigned to the secure user application code
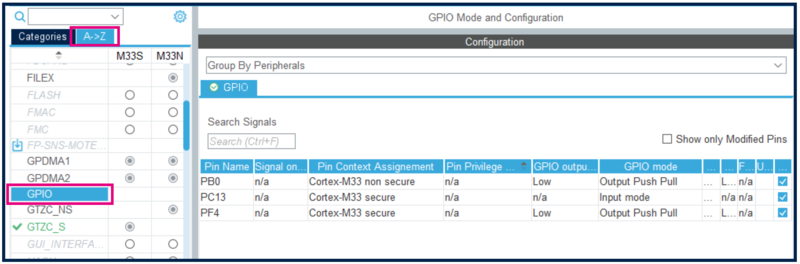
To configure the GPIO for the green LED proceed as follow:
- Click left on PB0: select GPIO_Output -> a push pull output will be configured need to drive an LED
- Click right on PB0: and select Cortex-M33 non-secure. This GPIO is then assigned to the non-secure user application code
- Select GPIO: the summary of the settings are displayed as shown in the figure below
3. Configure the OEMiROT bootpath
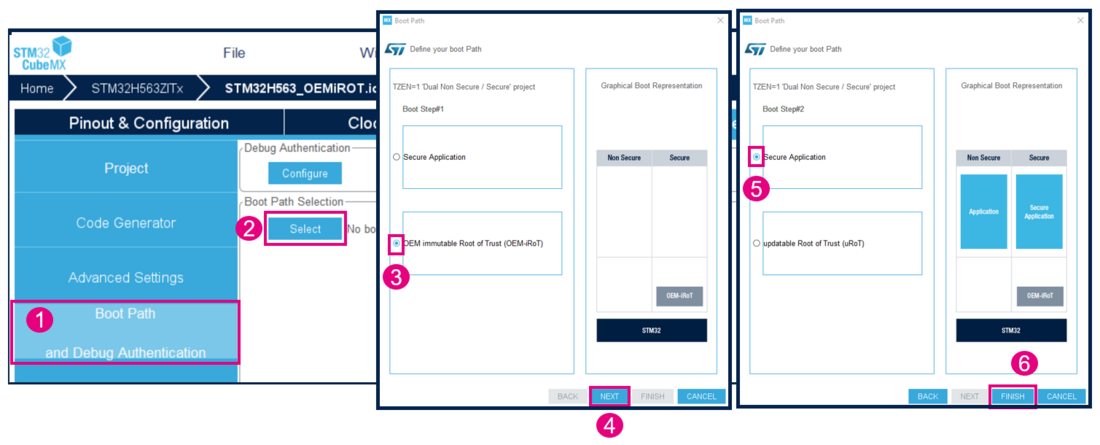
To configure the bootpath number 1 of the figure 1 proceed as follow:
- 1) Click on "Boot Path and Debug Authentication"
- 2) Click on "Select"
- 3) Select the OEM-iROT. The TZ activation has already been chosen, this selection is defining the UBE option byte (but you don't need to take care about the setting of this option byte).
- 4) Click on "Next"
- 5) Select Secure Application (since for this example there is no uROT, so no second boot stage)
- 6) Click Finish
OEMiROT_Boot firmware
OEMiROT_Boot is executed in HDPL1 in User Flash and perform authenticity and integrity checks of the User application and data images. It also configures the number of User application and images.
Please refer to OEMiROT STM32H5 How to Introduction for more informations.
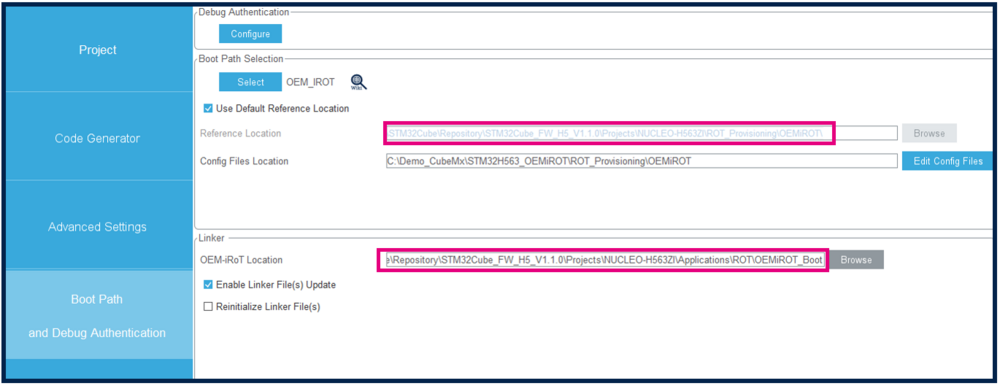
You can see the OEMiROT_Boot firmware path in Boot path and Linker tabs.
This firmware is located by default in STM32CubeH5 package installed through STM32CubeMX. It will be compiled during provisioning step.
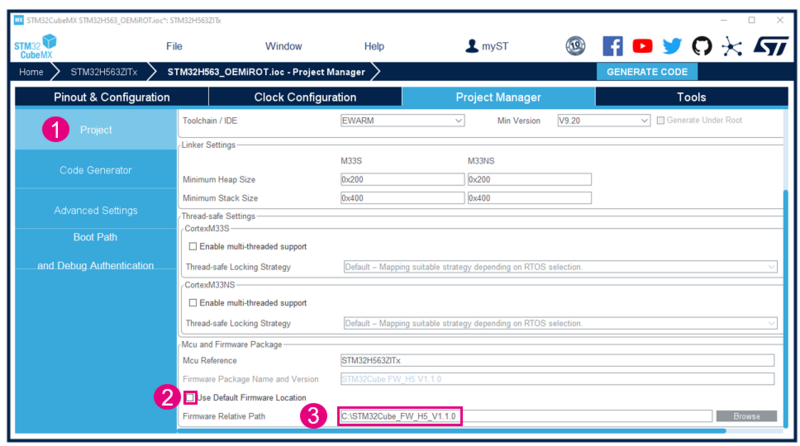
If you want to use an other repository for STM32CubeH5 package than the default CubeMX folder you can define it in
Project Manager--> Project Tab-->MCu and Firmware Package:
- Uncheck Use Default Firmware Location
- Define the path you want to use in Firmware Relative Path
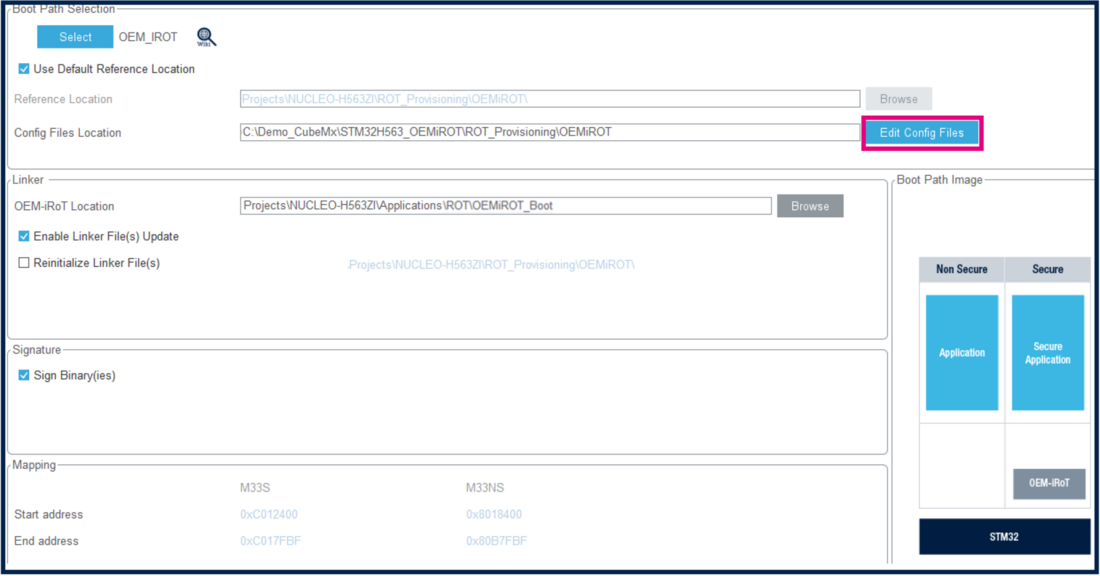
OEMiROT configuration
In the Project Manager window, select Edit Config, as shown in the figure below.
It will automatically open STM32Trusted Package Creator (TPC).
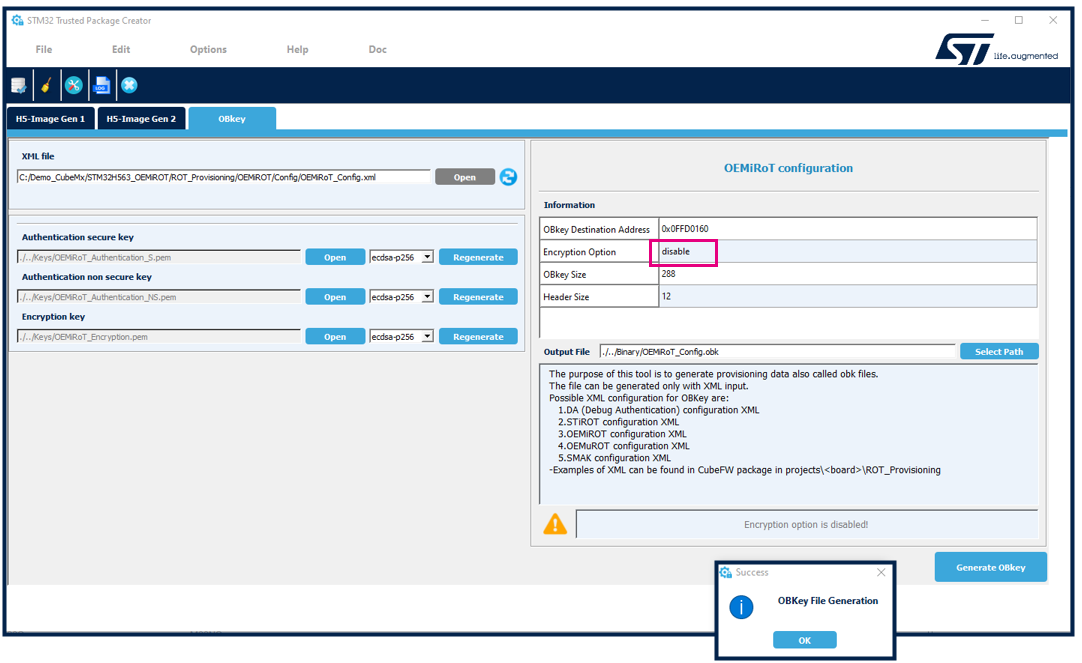
And the following window is displayed.
- Generate the OBKey file :
Notes:
- For STM32H563 devices Encryption option is disabled. This option is enabled only on STM32H573 crypto devices.
- The figure above, shows the path where the OEMiROT_Config.xml file is located. This file configures the keys used to encrypt/decrypt the data and sign/check the signature of the user application.
- The configuration of the OEM-iROT is made in the OEMiROT_Boot firmware. During the provisioning the download area is used to store the encrypted user application, that is decrypted by the OEMiROT and installed in the execution area (refer to the OEMiROT STM32H5 How to Introduction article).
- The firmware area size is the total size of the secure and non secure user application codes (the secure area size is indicated separately)
As mentioned above, for this example you don't need to make any other updates of the default configuration.
- Close STM32 Trusted Package Creator
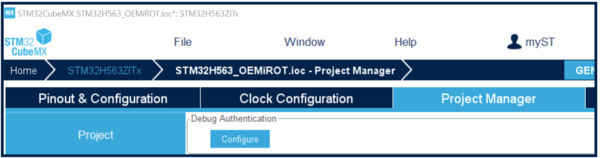
4. Debug Authentication configuration
Refer to the Debug_Authentication_for_STM32H5_MCUs article for more details.
A default configuration file (fully functional) and related OBKey file are provided through the STM32CubeFW.
To customize the Debug Authentication proceed as following:
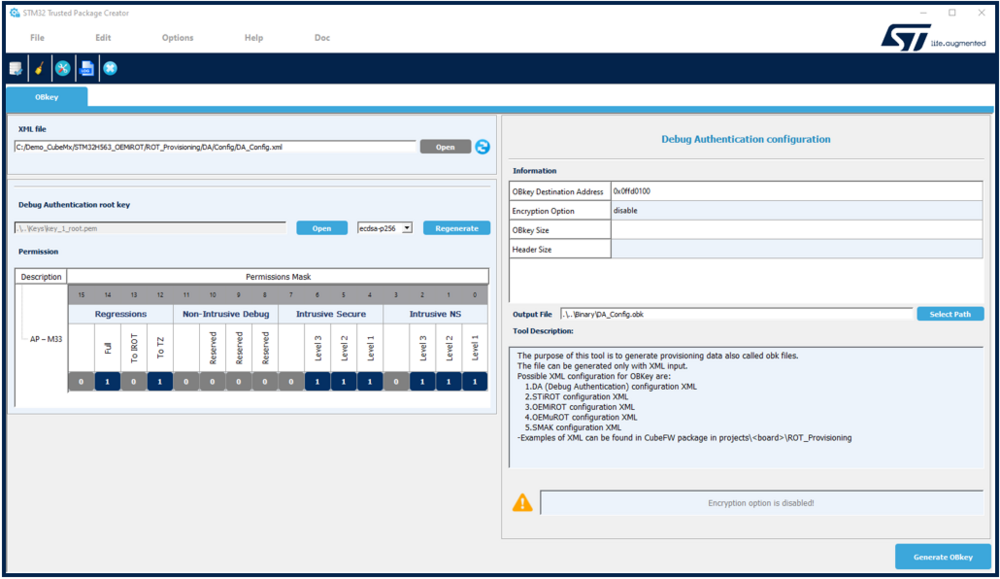
- In STM32CubeMx -> Project Manager -> Select: Debug Authentication Configure.
- The STM32Trusted Package Creator is launched (TPC installed together with STM32CubeProgrammer) and the DA_Config.xml file is automatically open.
- The "key_1_root" key is needed to reopen the device or to perform a regression. To protect you own developed application, this key needs to be regenerated. If regenerated, it's important to not lose this new key.
- Don't regenerate the key for this example
- The permission mask is set to allow all possible regressions and debug openings in the secure and non-secure user application. See Debug Authentication STM32H5 How to Introduction article for more details.
This permission mask, called the SOC mask is stored in the device during the provisioning process.
The owner of the root key has then the defined privileges to perform a regression or open the debugger according set permissions.
- Close STM32Trusted Package Creator
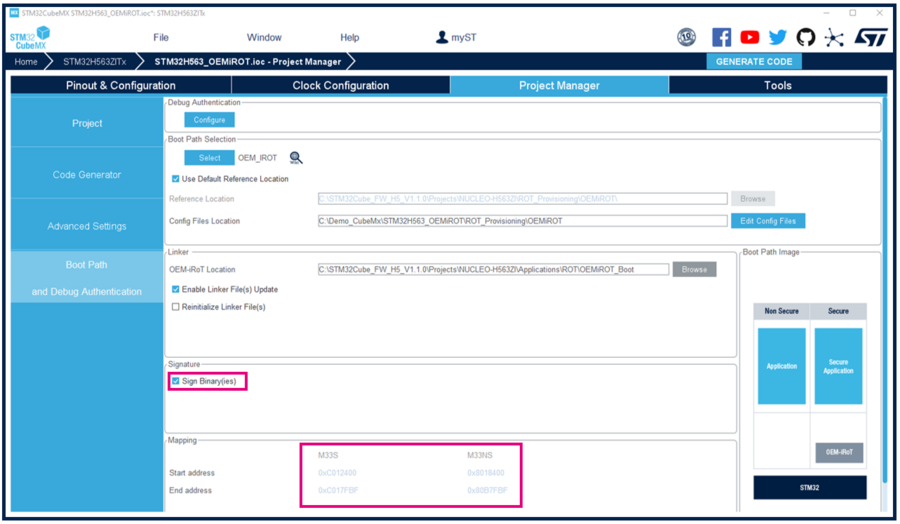
5. Initial Code Generation and modication
Select Project Manager in STM32CubeMX
- Ensure Sign Binaries is selected -> at each user application code compilation using the IDE an encrypted and signed binary is created containing both secure and non secure user application (compilation -> postbuild command)
- Note that start and end address are indicated for the secure and non-secure according to the OEMiROT configuration
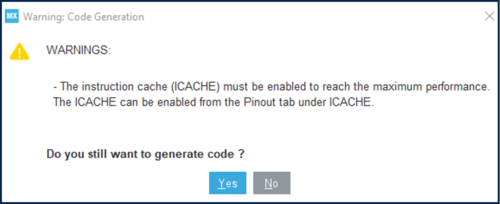
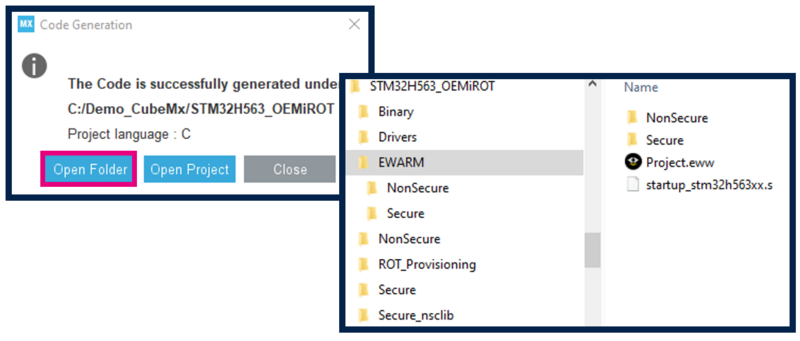
- Click Generate Code.
- You can have the following warning message. Click yes to generate the code.
- Or if you want to enable the Instruction Cache, select the Pinout Tab (see figure 9, select ICache located just below the GPIO configuration)
- Open generated user application.
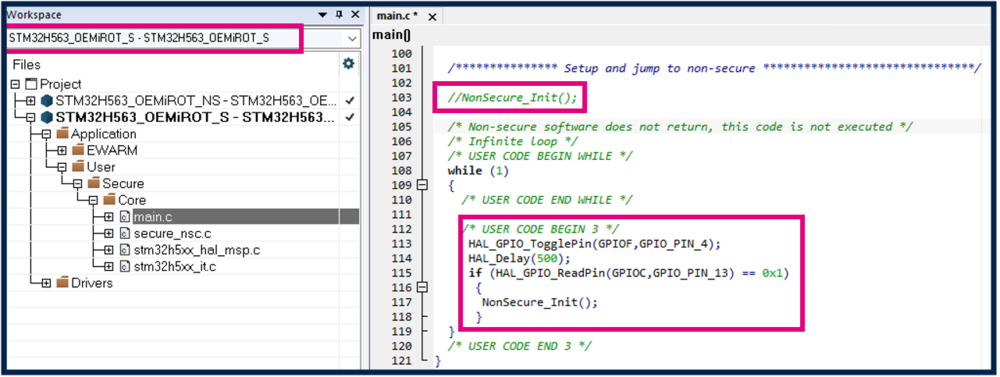
Open the secure user application code
- Comment out NonSecure_Init() for the jump into the non secure user application code (replaced with the code below).
- Insert the following code as shown in the figure below
HAL_GPIO_TogglePin(GPIOF,GPIO_PIN_4);
HAL_Delay(500);
if (HAL_GPIO_ReadPin(GPIOC,GPIO_PIN_13) == 0x1)
{
NonSecure_Init();
}
This code will make the blue LED blinking with the chosen Delay, showing that the secure user application is executed.
If the user blue button is pushed the jump in the non secure code is done through the Non-Secure_Init .
- Compile the code using the IDE (Project -> Rebuild all).
- Note: the secure code need to be compiled first (before the non-secure code)
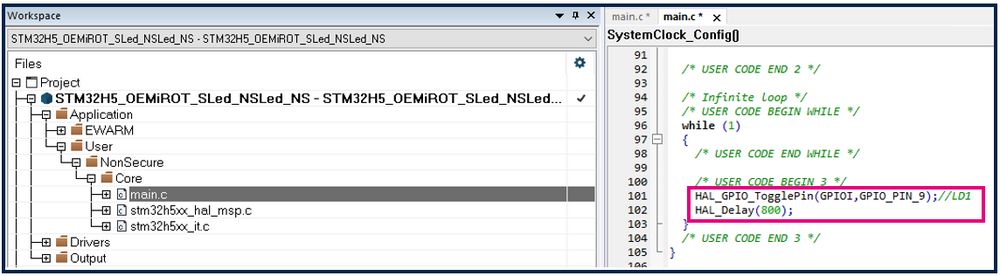
Open the non-secure user application
- Insert the following code as shown in the figure below
HAL_GPIO_TogglePin(GPIOI,GPIO_PIN_9);
HAL_Delay(800);
This code will make the geen LED blinking with the chosen Delay, showing that the non-secure user application is executed.
- Compile the code using the IDE (Project -> Rebuild all).
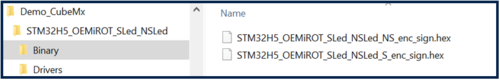
Two binaries are created as shown in the figure below.
- The assembled binary of the secure and non-secure user application
- The binary obtained after encryption and signature of the assembled binary. The signed and encrypted file is generated through the automatically called postbuild command (ticked "Sign Binary" in the window figure 16).
6. Appendix
6.1. STM32CubeFW installation
The STM32CubeFW needs to be installed through STM32CubeMX.
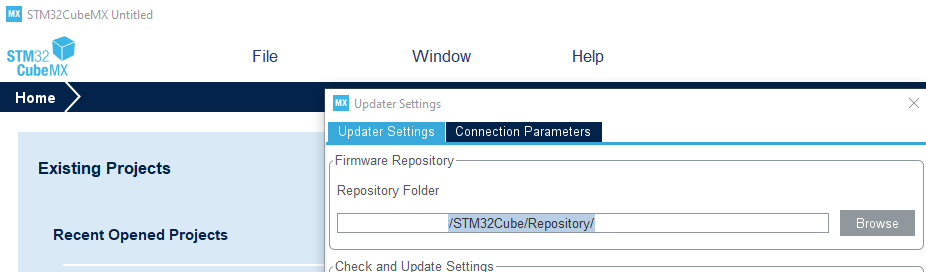
- Step 1: the repository folder has to be defined:
- In CubeMx: Help menu -> Updater Settings
- Browse the repository you have chosen for the STM32CubeFW
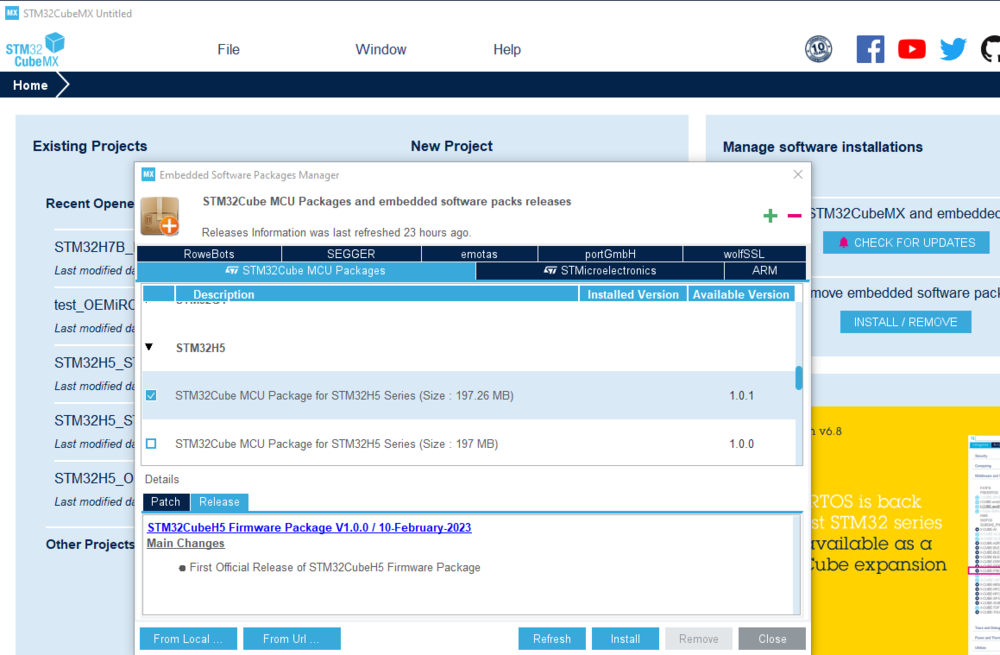
- Step 2: STM32CubeFW installation
- In STM32CubeMX: Select Install/Remove
- In the description frame: select STM32H5
- Select the CubeFW package to install
- In case you have locally the zip file of the STM32CubeFWH5: it can be installed by drag and drop this file in the description window
Note: only official STM32CubeFW release can be installed by STM32CubeMX.