This page reports measured performance when using the pure software cryptographic library algorithms with an STM32H5 MCU. In addition to performance figures, the required code footprint and memory are also given.
1. Measurement configuration
1.1. Hardware configuration
| STM32 MCU | STM32H563ZI |
| Device ID | 0x484 |
| Revision ID | 0x1000 |
| Board | NUCLEO-H563ZI |
1.2. Firmware configuration
| Cryptographic Library version | 040000B1[ver. 1] |
- ↑ This value corresponds to the information returned by a call to cmox_getInfos
1.3. System configuration
| System Core Clock Frequency | 240 MHz |
| Flash latency | 5 wait states |
| Voltage scaling | Range 3 |
| ICACHE peripheral | 1 (0: disabled / 1: enabled) |
| Prefetch Cache (ART) | 1 (0: disabled / 1: enabled) |
1.4. Development toolchains and compilers
| IAR Embedded Workbench | IAR ANSI C/C++ Compiler V9.20.4.327/W64 for ARM |
2. Performance values
2.1. AES symmetric key encryption and decryption
This section provides the performance results for AES-CBC using different modes of operation:
- Sole buffer: one sole buffer is encrypted or decrypted. Time to perform is given in µs.
- Data flow: a big message is encrypted or decrypted by chunk. Bit rate is given in kilobytes per second.
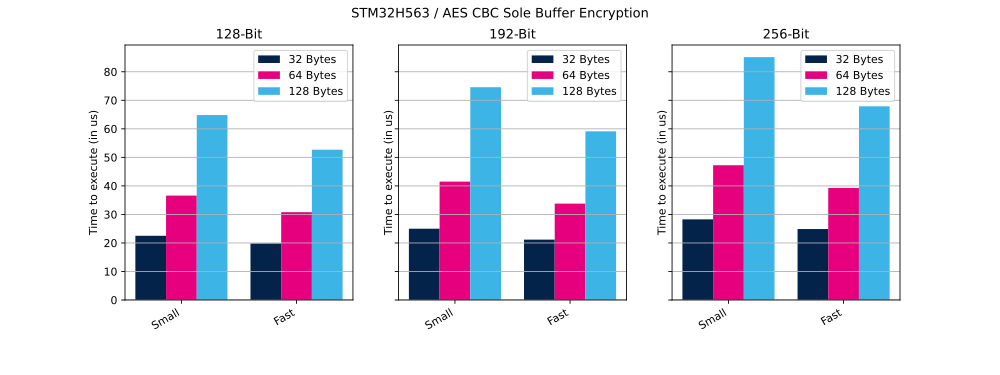
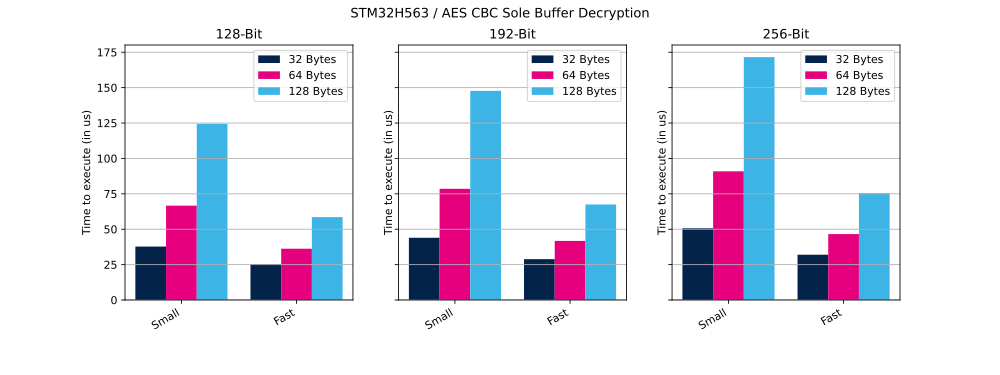
2.1.1. Sole buffer mode
In this mode the entire encryption or decryption process, for the whole message size, is managed through a single API call provided by the CMOX library.
The table below shows the number of clock cycles and time (in µs) needed to perform the described operation in small and fast configurations.
| AES mode | Key size | Buffer size | Cipher operation | Configuration | Cycles | Time |
|---|---|---|---|---|---|---|
| AES CBC | 128 bits | 32 bytes | Encryption | Small | 5311 | 22 µs |
| AES CBC | 128 bits | 32 bytes | Encryption | Fast | 4796 | 19 µs |
| AES CBC | 128 bits | 64 bytes | Encryption | Small | 8698 | 36 µs |
| AES CBC | 128 bits | 64 bytes | Encryption | Fast | 7409 | 30 µs |
| AES CBC | 128 bits | 128 bytes | Encryption | Small | 15 499 | 64 µs |
| AES CBC | 128 bits | 128 bytes | Encryption | Fast | 12 667 | 52 µs |
| AES CBC | 192 bits | 32 bytes | Encryption | Small | 5884 | 24 µs |
| AES CBC | 192 bits | 32 bytes | Encryption | Fast | 5165 | 21 µs |
| AES CBC | 192 bits | 64 bytes | Encryption | Small | 9852 | 41 µs |
| AES CBC | 192 bits | 64 bytes | Encryption | Fast | 8196 | 34 µs |
| AES CBC | 192 bits | 128 bytes | Encryption | Small | 17 792 | 74 µs |
| AES CBC | 192 bits | 128 bytes | Encryption | Fast | 14 259 | 59 µs |
| AES CBC | 256 bits | 32 bytes | Encryption | Small | 6709 | 27 µs |
| AES CBC | 256 bits | 32 bytes | Encryption | Fast | 5976 | 24 µs |
| AES CBC | 256 bits | 64 bytes | Encryption | Small | 11 259 | 46 µs |
| AES CBC | 256 bits | 64 bytes | Encryption | Fast | 9423 | 39 µs |
| AES CBC | 256 bits | 128 bytes | Encryption | Small | 20 359 | 84 µs |
| AES CBC | 256 bits | 128 bytes | Encryption | Fast | 16 300 | 67 µs |
| AES CBC | 128 bits | 32 bytes | Decryption | Small | 8892 | 37 µs |
| AES CBC | 128 bits | 32 bytes | Decryption | Fast | 6095 | 25 µs |
| AES CBC | 128 bits | 64 bytes | Decryption | Small | 15 826 | 65 µs |
| AES CBC | 128 bits | 64 bytes | Decryption | Fast | 8761 | 36 µs |
| AES CBC | 128 bits | 128 bytes | Decryption | Small | 29 694 | 123 µs |
| AES CBC | 128 bits | 128 bytes | Decryption | Fast | 14 132 | 58 µs |
| AES CBC | 192 bits | 32 bytes | Decryption | Small | 10 444 | 43 µs |
| AES CBC | 192 bits | 32 bytes | Decryption | Fast | 6914 | 28 µs |
| AES CBC | 192 bits | 64 bytes | Decryption | Small | 18 736 | 78 µs |
| AES CBC | 192 bits | 64 bytes | Decryption | Fast | 9974 | 41 µs |
| AES CBC | 192 bits | 128 bytes | Decryption | Small | 35 337 | 147 µs |
| AES CBC | 192 bits | 128 bytes | Decryption | Fast | 16 183 | 67 µs |
| AES CBC | 256 bits | 32 bytes | Decryption | Small | 11 959 | 49 µs |
| AES CBC | 256 bits | 32 bytes | Decryption | Fast | 7728 | 32 µs |
| AES CBC | 256 bits | 64 bytes | Decryption | Small | 21 616 | 90 µs |
| AES CBC | 256 bits | 64 bytes | Decryption | Fast | 11 191 | 46 µs |
| AES CBC | 256 bits | 128 bytes | Decryption | Small | 40 963 | 170 µs |
| AES CBC | 256 bits | 128 bytes | Decryption | Fast | 18 133 | 75 µs |
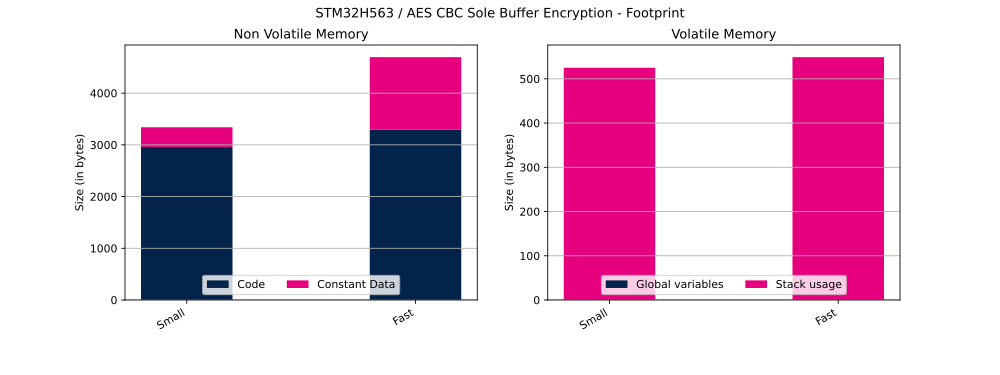
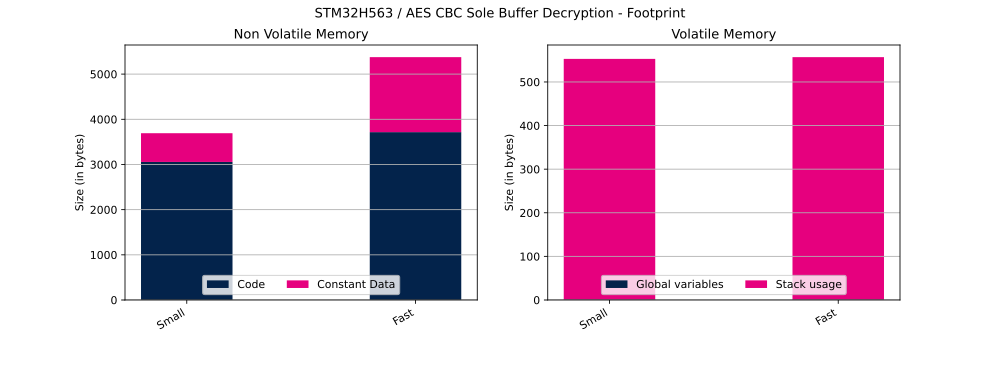
The table below shows Flash and RAM usage (in bytes).
| Cipher operation | Configuration | Code | Constant data | Global data | Stack usage |
|---|---|---|---|---|---|
| Encryption | Small | 2960 bytes | 380 bytes | 1 bytes | 524 bytes |
| Encryption | Fast | 3292 bytes | 1404 bytes | 1 bytes | 548 bytes |
| Decryption | Small | 3056 bytes | 636 bytes | 1 bytes | 552 bytes |
| Decryption | Fast | 3716 bytes | 1660 bytes | 1 bytes | 556 bytes |
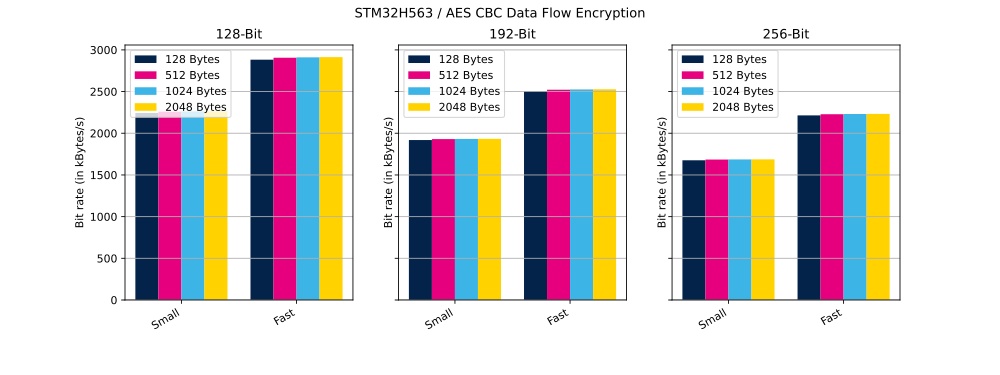
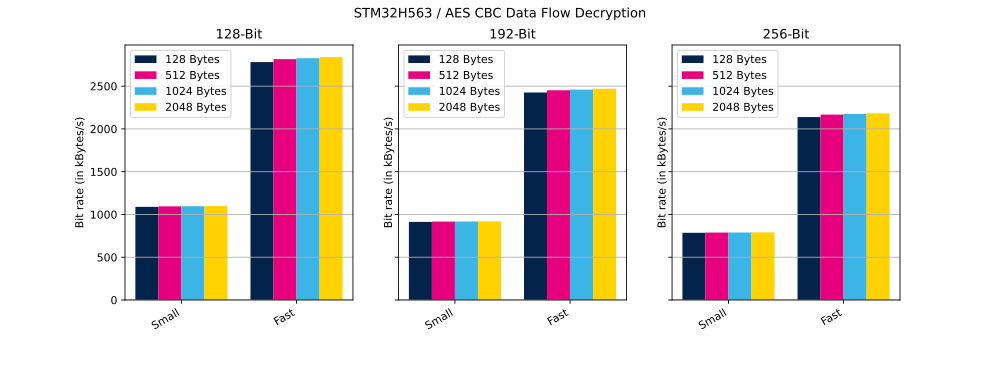
2.1.2. Data flow mode
In this mode, operation is performed in several calls to the CMOX library APIs, as below:
- cmox_cipher_init
- cmox_cipher_setKey
- cmox_cipher_setIV
- cmox_cipher_append: called several times to encrypt or decrypt the whole message by chunk of fixed size
The table below shows the number of clock cycles and bit rate (in kilobytes per second) needed to perform the described operation in small and in fast configuration.
| AES mode | Key size | Message size | Chunk size | Cipher operation | Configuration | Cycles | Bit rate |
|---|---|---|---|---|---|---|---|
| AES CBC | 128 bits | 8000 bytes | 128 bytes | Encryption | Small | 855 728 | 2243 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 128 bytes | Encryption | Fast | 666 656 | 2880 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 512 bytes | Encryption | Small | 849 800 | 2259 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 512 bytes | Encryption | Fast | 661 256 | 2903 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 1024 bytes | Encryption | Small | 848 776 | 2262 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 1024 bytes | Encryption | Fast | 660 216 | 2908 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 2048 bytes | Encryption | Small | 848 256 | 2263 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 2048 bytes | Encryption | Fast | 659 640 | 2910 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 128 bytes | Encryption | Small | 1 000 728 | 1918 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 128 bytes | Encryption | Fast | 767 040 | 2503 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 512 bytes | Encryption | Small | 994 840 | 1929 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 512 bytes | Encryption | Fast | 761 608 | 2520 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 1024 bytes | Encryption | Small | 993 808 | 1931 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 1024 bytes | Encryption | Fast | 760 560 | 2524 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 2048 bytes | Encryption | Small | 993 280 | 1932 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 2048 bytes | Encryption | Fast | 760 016 | 2526 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 128 bytes | Encryption | Small | 1 145 736 | 1675 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 128 bytes | Encryption | Fast | 868 936 | 2209 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 512 bytes | Encryption | Small | 1 139 856 | 1684 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 512 bytes | Encryption | Fast | 862 376 | 2226 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 1024 bytes | Encryption | Small | 1 138 832 | 1685 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 1024 bytes | Encryption | Fast | 861 184 | 2229 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 2048 bytes | Encryption | Small | 1 138 264 | 1686 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 2048 bytes | Encryption | Fast | 860 576 | 2231 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 128 bytes | Decryption | Small | 1 762 040 | 1089 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 128 bytes | Decryption | Fast | 691 936 | 2774 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 512 bytes | Decryption | Small | 1 753 592 | 1094 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 512 bytes | Decryption | Fast | 682 624 | 2812 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 1024 bytes | Decryption | Small | 1 751 152 | 1096 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 1024 bytes | Decryption | Fast | 679 776 | 2824 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 2048 bytes | Decryption | Small | 1 748 304 | 1098 kbyte/s |
| AES CBC | 128 bits | 8000 bytes | 2048 bytes | Decryption | Fast | 676 808 | 2836 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 128 bytes | Decryption | Small | 2 103 056 | 912 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 128 bytes | Decryption | Fast | 791 904 | 2424 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 512 bytes | Decryption | Small | 2 094 600 | 916 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 512 bytes | Decryption | Fast | 783 384 | 2450 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 1024 bytes | Decryption | Small | 2 092 088 | 917 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 1024 bytes | Decryption | Fast | 780 832 | 2458 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 2048 bytes | Decryption | Small | 2 089 184 | 919 kbyte/s |
| AES CBC | 192 bits | 8000 bytes | 2048 bytes | Decryption | Fast | 777 976 | 2467 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 128 bytes | Decryption | Small | 2 443 944 | 785 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 128 bytes | Decryption | Fast | 896 776 | 2141 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 512 bytes | Decryption | Small | 2 435 432 | 788 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 512 bytes | Decryption | Fast | 885 992 | 2167 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 1024 bytes | Decryption | Small | 2 433 008 | 789 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 1024 bytes | Decryption | Fast | 883 168 | 2173 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 2048 bytes | Decryption | Small | 2 430 112 | 790 kbyte/s |
| AES CBC | 256 bits | 8000 bytes | 2048 bytes | Decryption | Fast | 880 128 | 2181 kbyte/s |
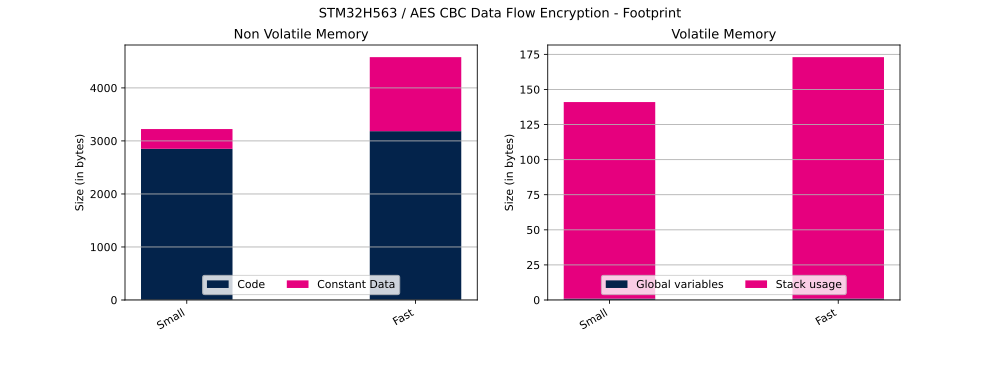
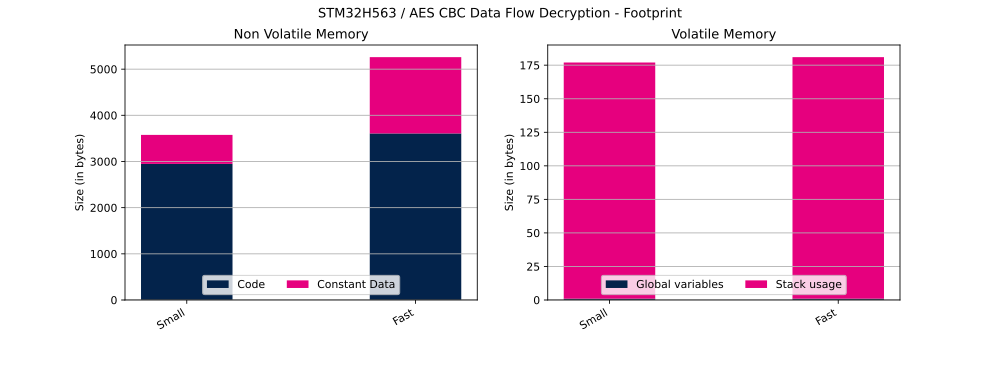
The table below shows Flash and RAM usage (in bytes).
| Cipher operation | Configuration | Code | Constant data | Global data | Stack usage |
|---|---|---|---|---|---|
| Encryption | Small | 2852 bytes | 372 bytes | 1 bytes | 140 bytes |
| Encryption | Fast | 3184 bytes | 1396 bytes | 1 bytes | 172 bytes |
| Decryption | Small | 2948 bytes | 628 bytes | 1 bytes | 176 bytes |
| Decryption | Fast | 3608 bytes | 1652 bytes | 1 bytes | 180 bytes |
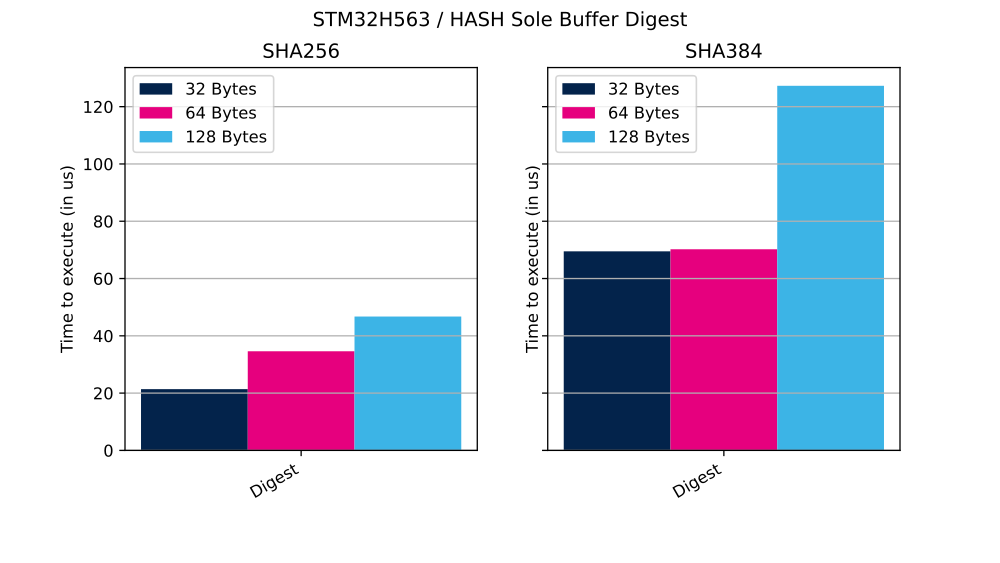
2.2. HASH digest
In this section we provide the performance results for HASH using different modes of operation:
- Sole buffer: one sole buffer is hashed. Time to perform is given in us.
- Data flow: a big message is hashed by chunk. Bit rate is given in bytes per s.
2.2.1. Sole buffer mode
In this mode, the entire message hashing process is managed through a single API call provided by the CMOX library.
The table below shows the number of clock cycles and time (in µs) needed to perform described operation.
| HASH mode | Buffer size | Cycles | Time |
|---|---|---|---|
| SHA256 | 32 bytes | 5137 | 21 µs |
| SHA256 | 64 bytes | 8297 | 34 µs |
| SHA256 | 128 bytes | 11 245 | 46 µs |
| SHA384 | 32 bytes | 16 693 | 69 µs |
| SHA384 | 64 bytes | 16 873 | 70 µs |
| SHA384 | 128 bytes | 30 570 | 127 µs |
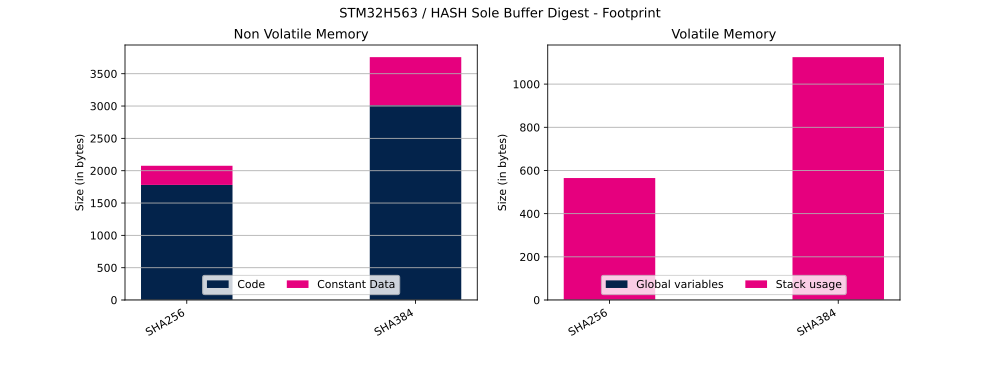
The table below shows Flash and RAM usage (in bytes).
| HASH mode | Code | Constant data | Global data | Stack usage |
|---|---|---|---|---|
| SHA256 | 1780 | 296 bytes | 1 bytes | 564 bytes |
| SHA384 | 3012 | 744 bytes | 1 bytes | 1124 bytes |
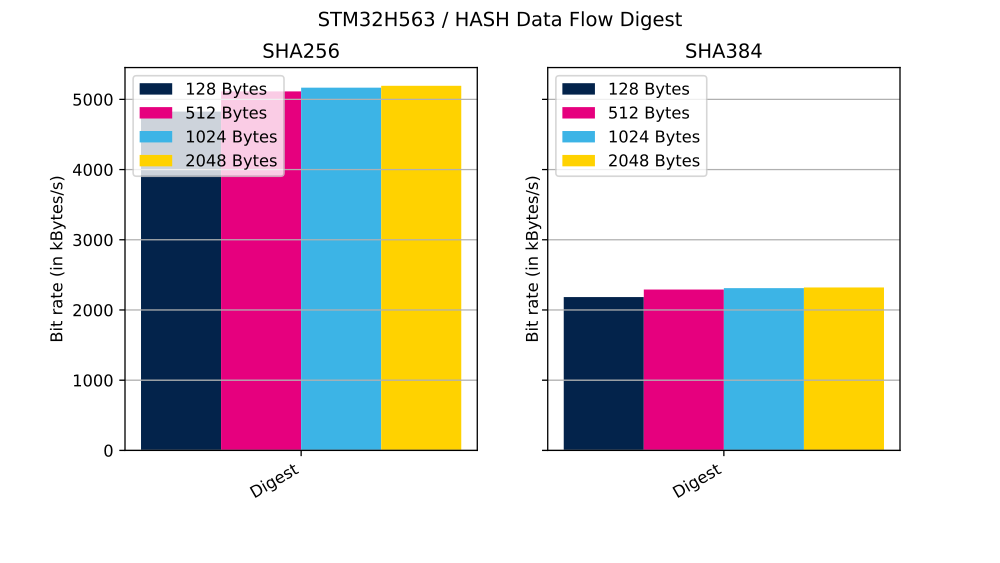
2.2.2. Data flow mode
In this mode, operation is performed in several calls to the CMOX library APIs, as below:
- cmox_hash_init
- cmox_hash_append: called several times to hash the whole message by chunk of fixed size
- cmox_hash_generateTag
The table below shows the number of clock cycles and bit rate (in kilobytes per second) needed to perform described operation.
| HASH mode | Message size | Chunk size | Cycles | Bit rate |
|---|---|---|---|---|
| SHA256 | 8000 bytes | 128 bytes | 397 937 | 4824 kbyte/s |
| SHA256 | 8000 bytes | 512 bytes | 375 440 | 5113 kbyte/s |
| SHA256 | 8000 bytes | 1024 bytes | 371 643 | 5166 kbyte/s |
| SHA256 | 8000 bytes | 2048 bytes | 369 746 | 5192 kbyte/s |
| SHA384 | 8000 bytes | 128 bytes | 879 286 | 2183 kbyte/s |
| SHA384 | 8000 bytes | 512 bytes | 838 119 | 2290 kbyte/s |
| SHA384 | 8000 bytes | 1024 bytes | 830 950 | 2310 kbyte/s |
| SHA384 | 8000 bytes | 2048 bytes | 827 378 | 2320 kbyte/s |
The table below shows final tag generation done through the call to cmox_hash_generateTag.
| HASH mode | Cycles | Time |
|---|---|---|
| SHA256 | 4308 | 17 µs |
| SHA384 | 15 506 | 64 µs |
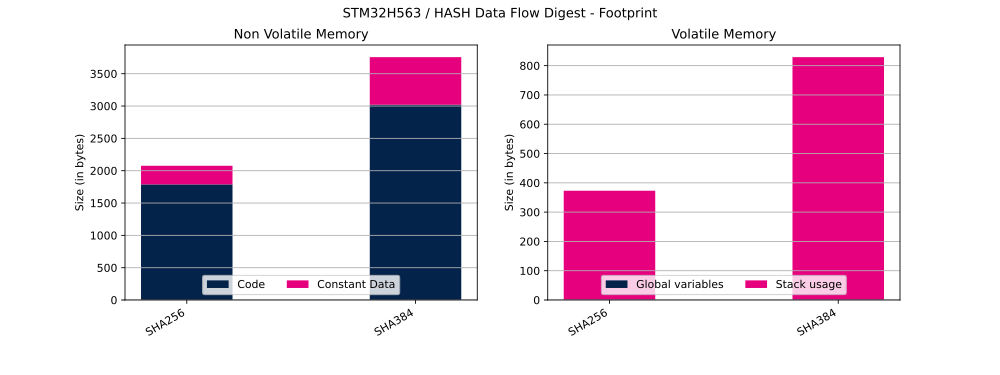
The table below shows Flash and RAM usage (in bytes).
| HASH mode | Code | Constant data | Global data | Stack usage |
|---|---|---|---|---|
| SHA256 | 1788 bytes | 288 bytes | 1 bytes | 372 bytes |
| SHA384 | 3020 bytes | 736 bytes | 1 bytes | 828 bytes |
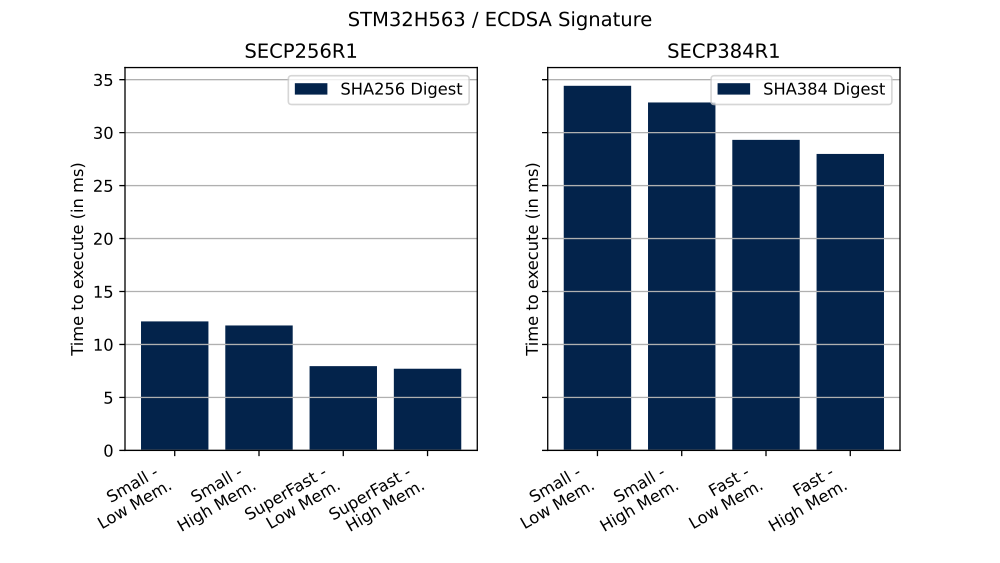
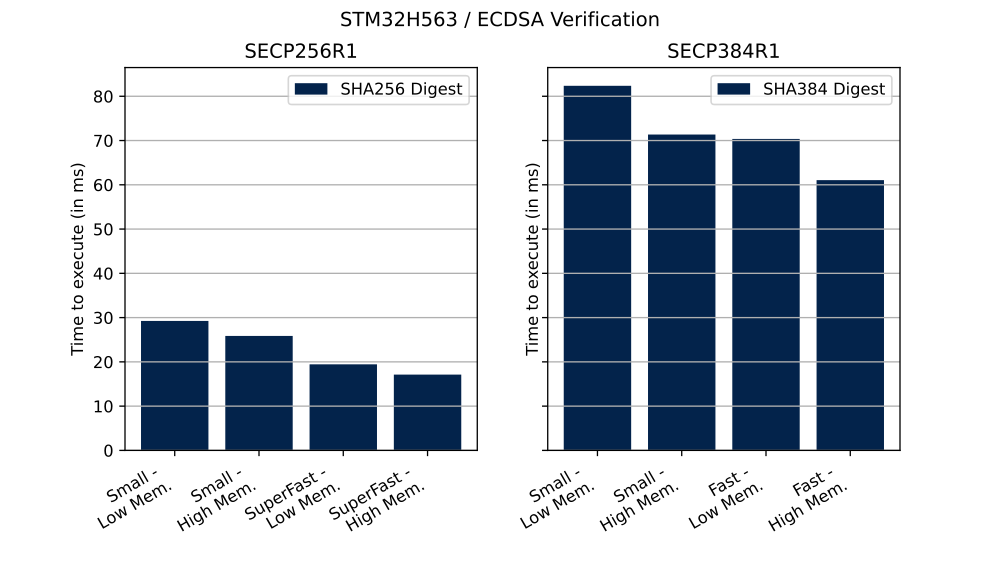
2.3. ECDSA signature and verification
In this section we provide the performance results for ECDSA signature and verification.
The table below shows the number of clock cycles and time (in ms) needed to perform described operation in different configurations.
| Curve | Operation | ECC mathematics configuration | Curve definition | Cycles | Time |
|---|---|---|---|---|---|
| SECP256R1 | Signature | Small | Low | 2 926 584 | 12 ms |
| SECP256R1 | Signature | Small | High | 2 832 432 | 11 ms |
| SECP256R1 | Signature | SuperFast | Low | 1 917 360 | 7 ms |
| SECP256R1 | Signature | SuperFast | High | 1 849 928 | 7 ms |
| SECP256R1 | Verification | Small | Low | 7 043 608 | 29 ms |
| SECP256R1 | Verification | Small | High | 6 207 528 | 25 ms |
| SECP256R1 | Verification | SuperFast | Low | 4 689 544 | 19 ms |
| SECP256R1 | Verification | SuperFast | High | 4 119 096 | 17 ms |
| SECP384R1 | Signature | Small | Low | 8 268 880 | 34 ms |
| SECP384R1 | Signature | Small | High | 7 887 296 | 32 ms |
| SECP384R1 | Signature | Fast | Low | 7 029 152 | 29 ms |
| SECP384R1 | Signature | Fast | High | 6 716 760 | 27 ms |
| SECP384R1 | Verification | Small | Low | 19 803 368 | 82 ms |
| SECP384R1 | Verification | Small | High | 17 131 040 | 71 ms |
| SECP384R1 | Verification | Fast | Low | 16 883 128 | 70 ms |
| SECP384R1 | Verification | Fast | High | 14 665 344 | 61 ms |
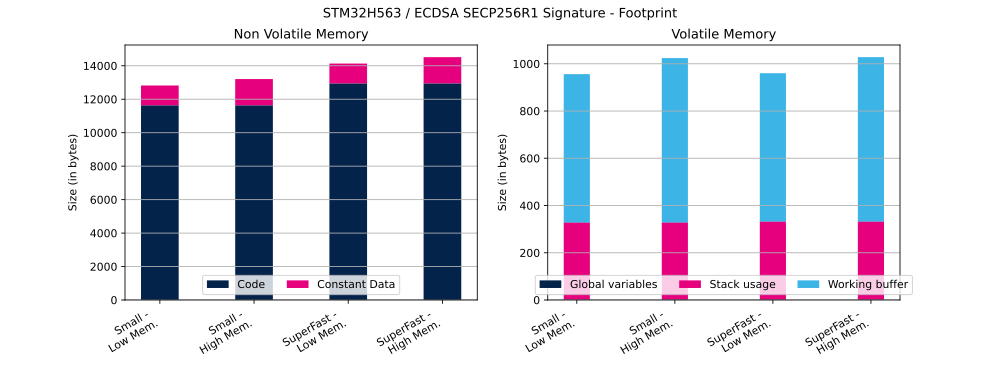
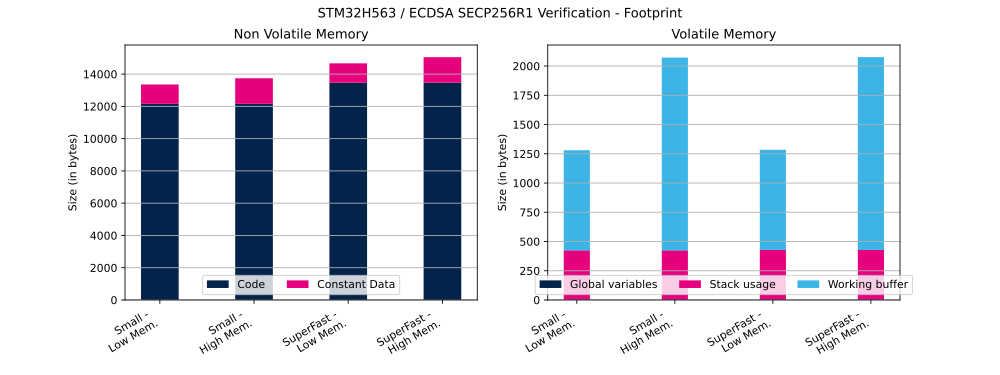
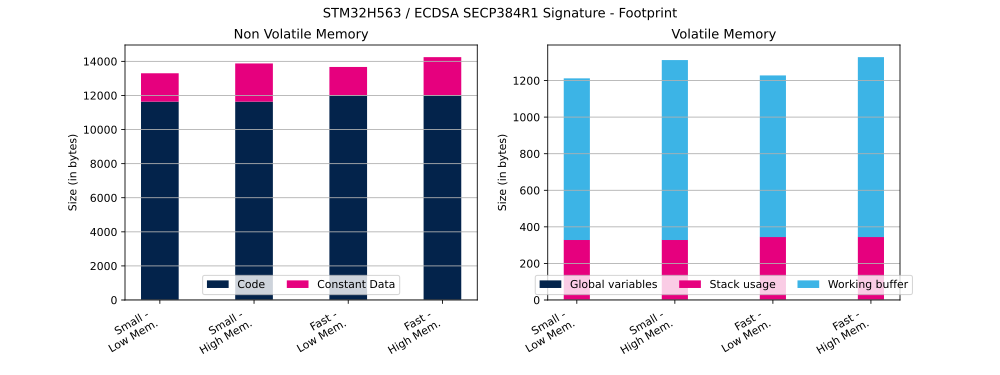
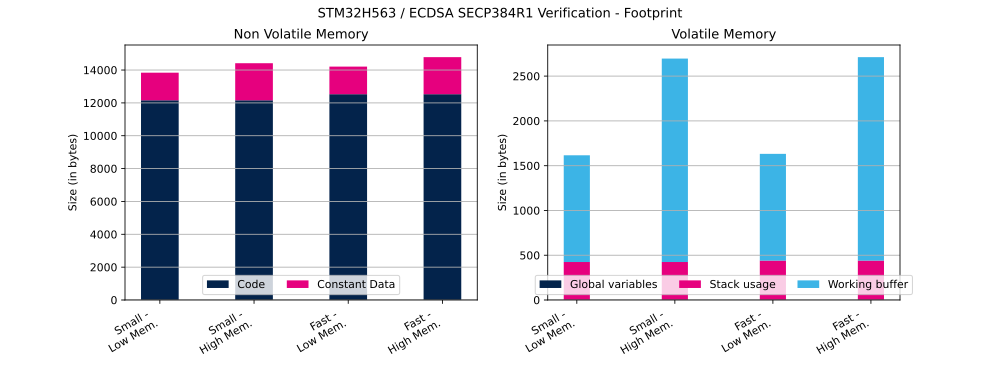
The table below shows ECDSA Flash and RAM usage (in bytes).
| Curve | Operation | ECC mathematics configuration | Curve definition | Code | Constant data | Global data | Stack usage | Working buffer |
|---|---|---|---|---|---|---|---|---|
| SECP256R1 | Signature | Small | Low | 11 636 bytes | 1184 bytes | 1 bytes | 328 bytes | 628 bytes |
| SECP256R1 | Signature | Small | High | 11 636 bytes | 1568 bytes | 1 bytes | 328 bytes | 696 bytes |
| SECP256R1 | Signature | SuperFast | Low | 12 946 bytes | 1184 bytes | 1 bytes | 332 bytes | 628 bytes |
| SECP256R1 | Signature | SuperFast | High | 12 946 bytes | 1568 bytes | 1 bytes | 332 bytes | 696 bytes |
| SECP256R1 | Verification | Small | Low | 12 158 bytes | 1200 bytes | 1 bytes | 424 bytes | 856 bytes |
| SECP256R1 | Verification | Small | High | 12 158 bytes | 1584 bytes | 1 bytes | 424 bytes | 1648 bytes |
| SECP256R1 | Verification | SuperFast | Low | 13 468 bytes | 1200 bytes | 1 bytes | 428 bytes | 856 bytes |
| SECP256R1 | Verification | SuperFast | High | 13 468 bytes | 1584 bytes | 1 bytes | 428 bytes | 1648 bytes |
| SECP384R1 | Signature | Small | Low | 11 636 bytes | 1664 bytes | 1 bytes | 328 bytes | 884 bytes |
| SECP384R1 | Signature | Small | High | 11 636 bytes | 2240 bytes | 1 bytes | 328 bytes | 984 bytes |
| SECP384R1 | Signature | Fast | Low | 12 006 bytes | 1664 bytes | 1 bytes | 344 bytes | 884 bytes |
| SECP384R1 | Signature | Fast | High | 12 006 bytes | 2240 bytes | 1 bytes | 344 bytes | 984 bytes |
| SECP384R1 | Verification | Small | Low | 12 158 bytes | 1680 bytes | 1 bytes | 424 bytes | 1192 bytes |
| SECP384R1 | Verification | Small | High | 12 158 bytes | 2256 bytes | 1 bytes | 424 bytes | 2272 bytes |
| SECP384R1 | Verification | Fast | Low | 12 528 bytes | 1680 bytes | 1 bytes | 440 bytes | 1192 bytes |
| SECP384R1 | Verification | Fast | High | 12 528 bytes | 2256 bytes | 1 bytes | 440 bytes | 2272 bytes |
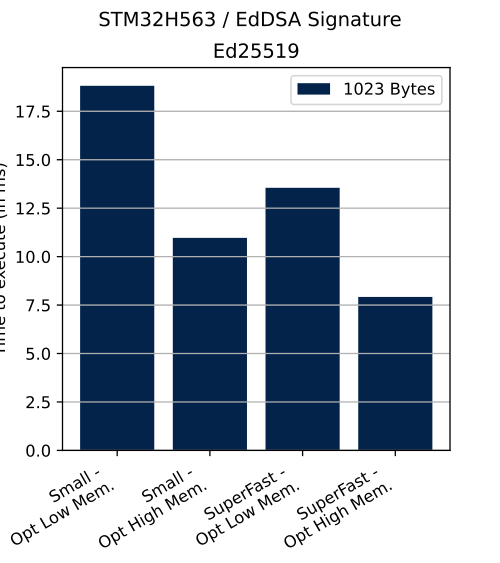
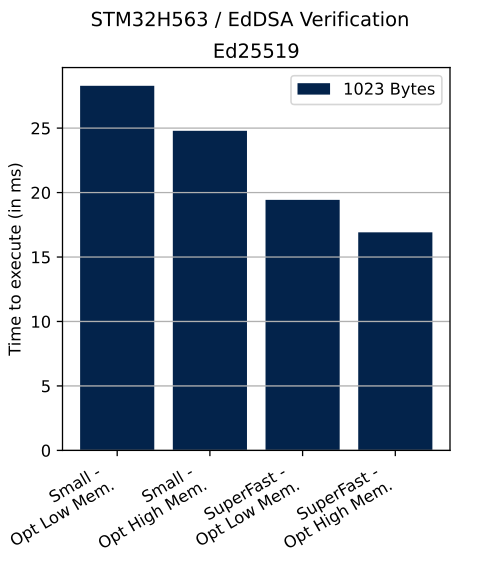
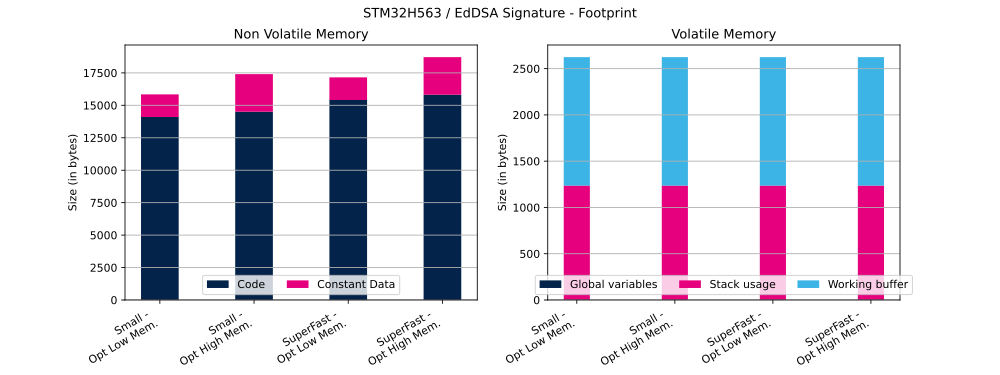
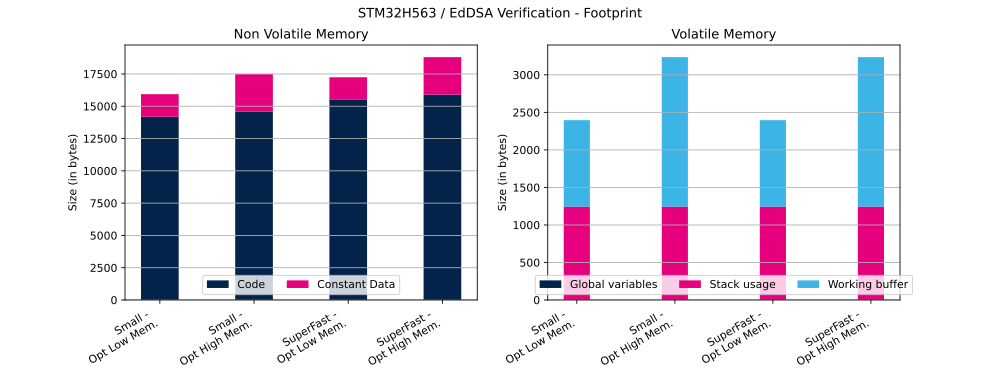
2.4. EdDSA signature and verification
In this section we provide the performance results for EdDSA signature and verification.
The table below shows the number of clock cycles and time (in ms) needed to perform described operation in different configurations.
| Curve | Message size | Operation | ECC mathematics configuration | Curve definition | Cycles | Time |
|---|---|---|---|---|---|---|
| Ed25519 | 1023 bytes | Signature | Small | OptLow | 4 518 104 | 18 ms |
| Ed25519 | 1023 bytes | Signature | Small | OptHigh | 2 633 240 | 10 ms |
| Ed25519 | 1023 bytes | Signature | SuperFast | OptLow | 3 236 048 | 13 ms |
| Ed25519 | 1023 bytes | Signature | SuperFast | OptHigh | 1 903 456 | 7 ms |
| Ed25519 | 1023 bytes | Verification | Small | OptLow | 6 796 704 | 28 ms |
| Ed25519 | 1023 bytes | Verification | Small | OptHigh | 5 949 248 | 24 ms |
| Ed25519 | 1023 bytes | Verification | SuperFast | OptLow | 4 653 904 | 19 ms |
| Ed25519 | 1023 bytes | Verification | SuperFast | OptHigh | 4 066 224 | 16 ms |
The table below shows EdDSA Flash and RAM usage (in bytes).
| Curve | Message size | Operation | ECC mathematics configuration | Curve definition | Code | Constant data | Global data | Stack usage | Working buffer |
|---|---|---|---|---|---|---|---|---|---|
| Ed25519 | 1023 bytes | Signature | Small | OptLow | 14 100 bytes | 1744 bytes | 1 bytes | 1236 bytes | 1388 bytes |
| Ed25519 | 1023 bytes | Signature | Small | OptHigh | 14 506 bytes | 2896 bytes | 1 bytes | 1236 bytes | 1388 bytes |
| Ed25519 | 1023 bytes | Signature | SuperFast | OptLow | 15 410 bytes | 1744 bytes | 1 bytes | 1236 bytes | 1388 bytes |
| Ed25519 | 1023 bytes | Signature | SuperFast | OptHigh | 15 816 bytes | 2896 bytes | 1 bytes | 1236 bytes | 1388 bytes |
| Ed25519 | 1023 bytes | Verification | Small | OptLow | 14 186 bytes | 1748 bytes | 1 bytes | 1244 bytes | 1152 bytes |
| Ed25519 | 1023 bytes | Verification | Small | OptHigh | 14 592 bytes | 2900 bytes | 1 bytes | 1244 bytes | 1992 bytes |
| Ed25519 | 1023 bytes | Verification | SuperFast | OptLow | 15 496 bytes | 1748 bytes | 1 bytes | 1244 bytes | 1152 bytes |
| Ed25519 | 1023 bytes | Verification | SuperFast | OptHigh | 15 902 bytes | 2900 bytes | 1 bytes | 1244 bytes | 1992 bytes |
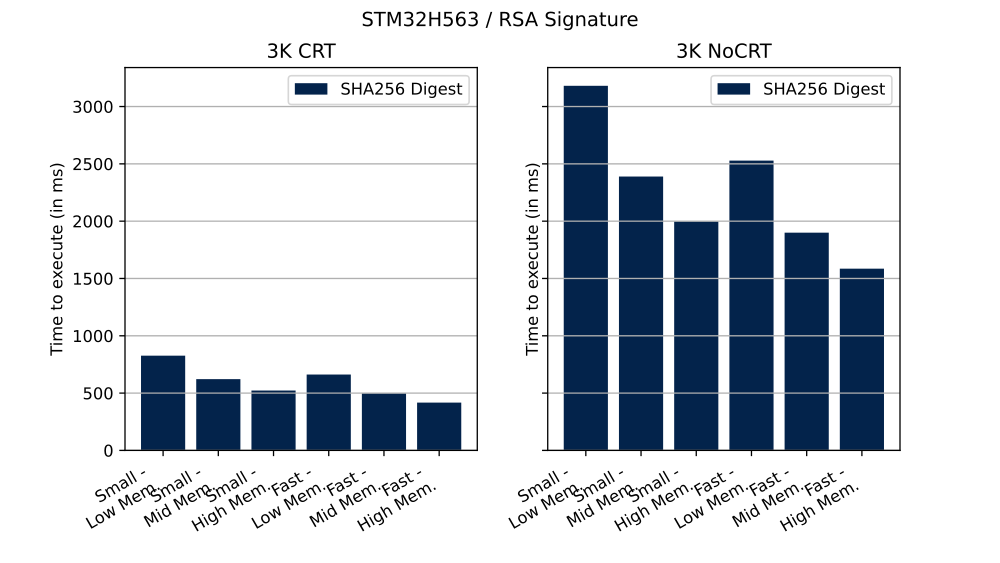
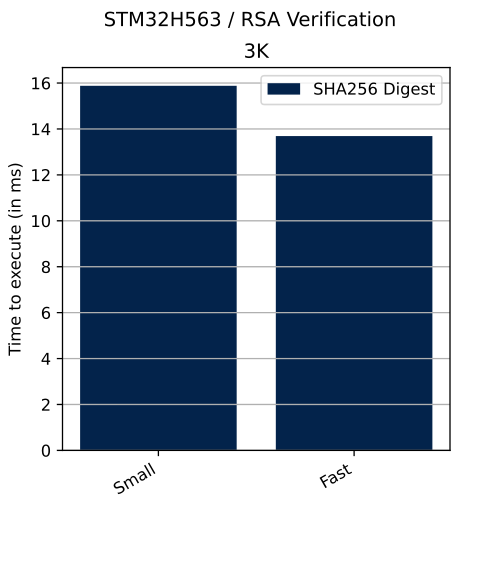
2.5. RSA signature and verification
In this section we provide the performance results for RSA signature and verification.
The table below shows the number of clock cycles and time (in ms) needed to perform described operation in different configurations.
| PKCS#1 | Priv. key mod. exp. method | Hash method | Modulus size | Operation | RSA mathematics configuration | Priv. key mod. exp. implementation | Cycles | Time |
|---|---|---|---|---|---|---|---|---|
| v2.2 | CRT | SHA-256 | 3K | Signature | Small | Low | 198 355 144 | 826 ms |
| v2.2 | CRT | SHA-256 | 3K | Signature | Small | Mid | 149 292 536 | 622 ms |
| v2.2 | CRT | SHA-256 | 3K | Signature | Small | High | 125 368 856 | 522 ms |
| v2.2 | CRT | SHA-256 | 3K | Signature | Fast | Low | 158 895 816 | 662 ms |
| v2.2 | CRT | SHA-256 | 3K | Signature | Fast | Mid | 119 656 056 | 498 ms |
| v2.2 | CRT | SHA-256 | 3K | Signature | Fast | High | 100 072 688 | 416 ms |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Small | Low | 763 445 784 | 3181 ms |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Small | Mid | 573 386 672 | 2389 ms |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Small | High | 479 616 768 | 1998 ms |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Fast | Low | 606 868 632 | 2528 ms |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Fast | Mid | 455 877 288 | 1899 ms |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Fast | High | 380 470 200 | 1585 ms |
| v2.2 | n/a | SHA-256 | 3K | Verification | Small | n/a | 3 811 416 | 15 ms |
| v2.2 | n/a | SHA-256 | 3K | Verification | Fast | n/a | 3 285 424 | 13 ms |
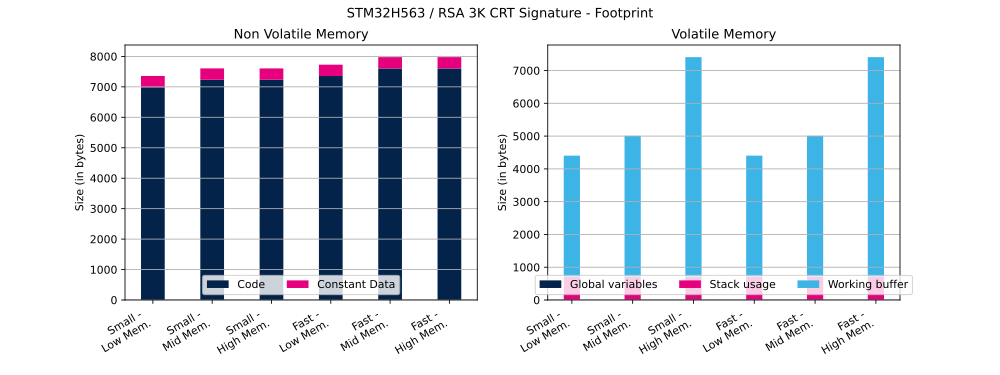
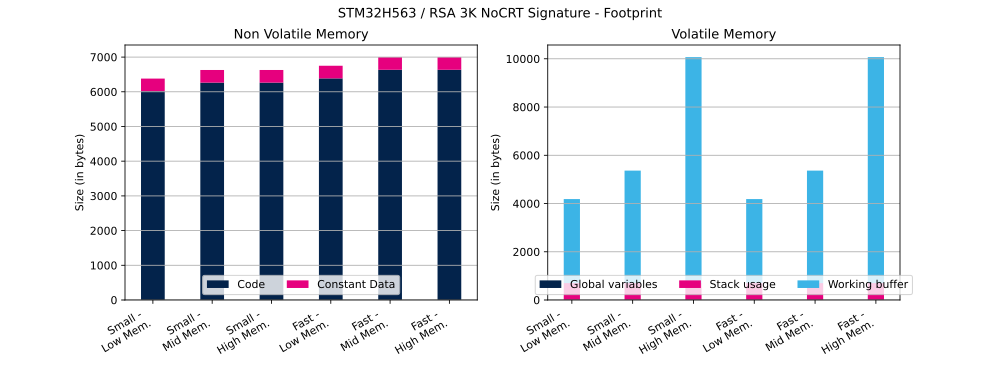
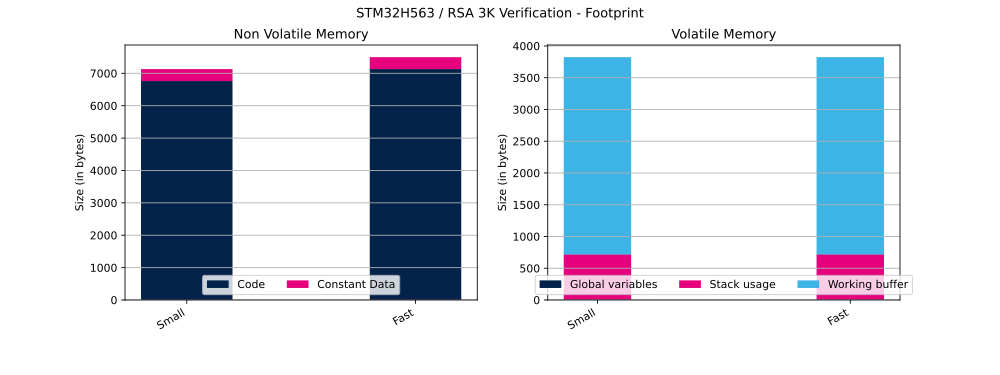
The table below shows RSA Flash and RAM usage (in bytes).
| PKCS#1 | Priv. key mod. exp. method | Hash method | Modulus size | Operation | RSA mathematics configuration | Priv. key mod. exp. implementation | Code | Constant data | Global data | Stack usage | Working buffer |
|---|---|---|---|---|---|---|---|---|---|---|---|
| v2.2 | CRT | SHA-256 | 3K | Signature | Small | Low | 6986 bytes | 372 bytes | 5 bytes | 700 bytes | 3704 bytes |
| v2.2 | CRT | SHA-256 | 3K | Signature | Small | Mid | 7234 bytes | 372 bytes | 5 bytes | 700 bytes | 4308 bytes |
| v2.2 | CRT | SHA-256 | 3K | Signature | Small | High | 7234 bytes | 372 bytes | 5 bytes | 700 bytes | 6708 bytes |
| v2.2 | CRT | SHA-256 | 3K | Signature | Fast | Low | 7356 bytes | 372 bytes | 5 bytes | 700 bytes | 3704 bytes |
| v2.2 | CRT | SHA-256 | 3K | Signature | Fast | Mid | 7604 bytes | 372 bytes | 5 bytes | 700 bytes | 4308 bytes |
| v2.2 | CRT | SHA-256 | 3K | Signature | Fast | High | 7604 bytes | 372 bytes | 5 bytes | 700 bytes | 6708 bytes |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Small | Low | 6016 bytes | 364 bytes | 5 bytes | 700 bytes | 3484 bytes |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Small | Mid | 6264 bytes | 364 bytes | 5 bytes | 700 bytes | 4664 bytes |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Small | High | 6264 bytes | 364 bytes | 5 bytes | 700 bytes | 9368 bytes |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Fast | Low | 6386 bytes | 364 bytes | 5 bytes | 700 bytes | 3484 bytes |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Fast | Mid | 6634 bytes | 364 bytes | 5 bytes | 700 bytes | 4664 bytes |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Fast | High | 6634 bytes | 364 bytes | 5 bytes | 700 bytes | 9368 bytes |
| v2.2 | n/a | SHA-256 | 3K | Verification | Small | n/a | 6762 bytes | 368 bytes | 5 bytes | 716 bytes | 3108 bytes |
| v2.2 | n/a | SHA-256 | 3K | Verification | Fast | n/a | 7132 bytes | 368 bytes | 5 bytes | 716 bytes | 3108 bytes |