This page reports measured performances when using the Cryptographic Library pure software algorithms with a STM32L5 MCU. In addition to performances, required code footprint and memory are also given.
1. Measurement configuration
1.1. Hardware configuration
| STM32 MCU | STM32L552ZET6Q |
| Device ID | 0x472 |
| Revision ID | 0x2000 |
| Board | NUCLEO-L552ZE-Q |
1.2. Firmware Configuration
| Cryptographic Library version | 040000B1[ver. 1] |
- ↑ This value corresponds to the information returned by a call to cmox_getInfos
1.3. System Configuration
| System Core Clock Frequency | 110 MHz |
| Flash latency | 5 wait states |
| Voltage scaling | Range 0 |
| Dual bank | 0 (0: Single / 1: Dual) |
| ICACHE peripheral | 1 (0: disabled / 1: enabled) |
1.4. Development Toolchains and Compilers
| IAR Embedded Workbench | IAR ANSI C/C++ Compiler V8.50.4.261/W32 for ARM |
2. Performances Values
2.1. AES Symmetric key encryption & decryption
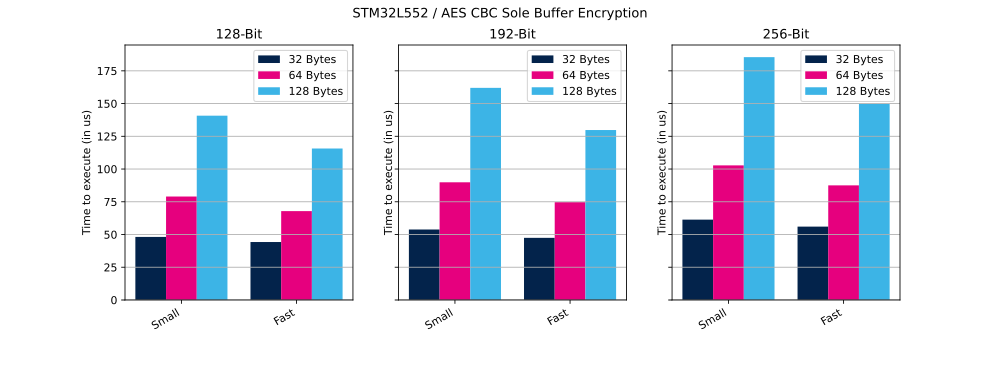
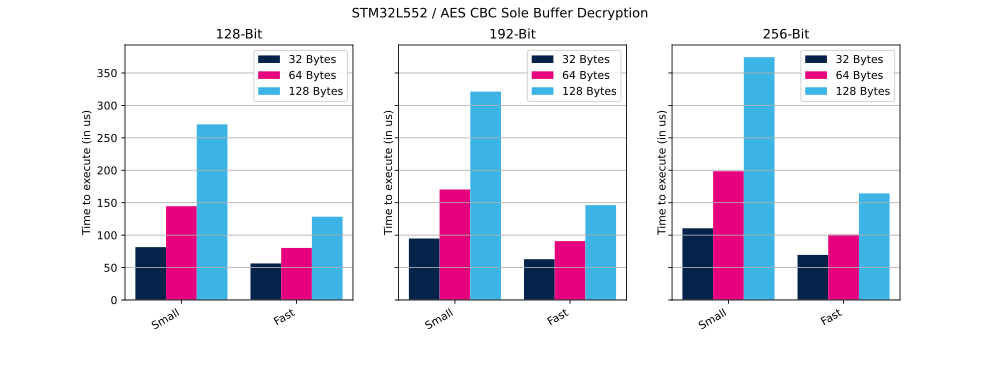
In this section we provide the performance results for AES-CBC using different modes of operation:
- Sole buffer: one sole buffer is encrypted or decrypted. Time to perform is given in µs.
- Data flow: a big message is encrypted or decrypted by chunk. Bit rate is given in Kbytes per s.
2.1.1. Sole buffer mode
In this mode, the entire encryption or decryption process, for the whole message size, is managed through a single API call provided by the CMOX library.
Table below shows the clock cycles and time (in us) needed to perform the described operation in small and in fast configuration.
| AES Mode | Key size | Buffer Size | Cipher Operation | Configuration | Cycles | Time |
|---|---|---|---|---|---|---|
| AES CBC | 128Bits | 32 bytes | Encryption | Small | 5,299 | 48 µs |
| AES CBC | 128Bits | 32 bytes | Encryption | Fast | 4,870 | 44 µs |
| AES CBC | 128Bits | 64 bytes | Encryption | Small | 8,692 | 79 µs |
| AES CBC | 128Bits | 64 bytes | Encryption | Fast | 7,466 | 67 µs |
| AES CBC | 128Bits | 128 bytes | Encryption | Small | 15,483 | 140 µs |
| AES CBC | 128Bits | 128 bytes | Encryption | Fast | 12,725 | 115 µs |
| AES CBC | 192Bits | 32 bytes | Encryption | Small | 5,922 | 53 µs |
| AES CBC | 192Bits | 32 bytes | Encryption | Fast | 5,221 | 47 µs |
| AES CBC | 192Bits | 64 bytes | Encryption | Small | 9,887 | 89 µs |
| AES CBC | 192Bits | 64 bytes | Encryption | Fast | 8,218 | 74 µs |
| AES CBC | 192Bits | 128 bytes | Encryption | Small | 17,820 | 162 µs |
| AES CBC | 192Bits | 128 bytes | Encryption | Fast | 14,277 | 129 µs |
| AES CBC | 256Bits | 32 bytes | Encryption | Small | 6,751 | 61 µs |
| AES CBC | 256Bits | 32 bytes | Encryption | Fast | 6,164 | 56 µs |
| AES CBC | 256Bits | 64 bytes | Encryption | Small | 11,308 | 102 µs |
| AES CBC | 256Bits | 64 bytes | Encryption | Fast | 9,629 | 87 µs |
| AES CBC | 256Bits | 128 bytes | Encryption | Small | 20,400 | 185 µs |
| AES CBC | 256Bits | 128 bytes | Encryption | Fast | 16,467 | 149 µs |
| AES CBC | 128Bits | 32 bytes | Decryption | Small | 8,968 | 81 µs |
| AES CBC | 128Bits | 32 bytes | Decryption | Fast | 6,198 | 56 µs |
| AES CBC | 128Bits | 64 bytes | Decryption | Small | 15,907 | 144 µs |
| AES CBC | 128Bits | 64 bytes | Decryption | Fast | 8,827 | 80 µs |
| AES CBC | 128Bits | 128 bytes | Decryption | Small | 29,785 | 270 µs |
| AES CBC | 128Bits | 128 bytes | Decryption | Fast | 14,122 | 128 µs |
| AES CBC | 192Bits | 32 bytes | Decryption | Small | 10,428 | 94 µs |
| AES CBC | 192Bits | 32 bytes | Decryption | Fast | 6,919 | 62 µs |
| AES CBC | 192Bits | 64 bytes | Decryption | Small | 18,739 | 170 µs |
| AES CBC | 192Bits | 64 bytes | Decryption | Fast | 9,986 | 90 µs |
| AES CBC | 192Bits | 128 bytes | Decryption | Small | 35,345 | 321 µs |
| AES CBC | 192Bits | 128 bytes | Decryption | Fast | 16,093 | 146 µs |
| AES CBC | 256Bits | 32 bytes | Decryption | Small | 12,165 | 110 µs |
| AES CBC | 256Bits | 32 bytes | Decryption | Fast | 7,648 | 69 µs |
| AES CBC | 256Bits | 64 bytes | Decryption | Small | 21,838 | 198 µs |
| AES CBC | 256Bits | 64 bytes | Decryption | Fast | 11,082 | 100 µs |
| AES CBC | 256Bits | 128 bytes | Decryption | Small | 41,185 | 374 µs |
| AES CBC | 256Bits | 128 bytes | Decryption | Fast | 18,073 | 164 µs |
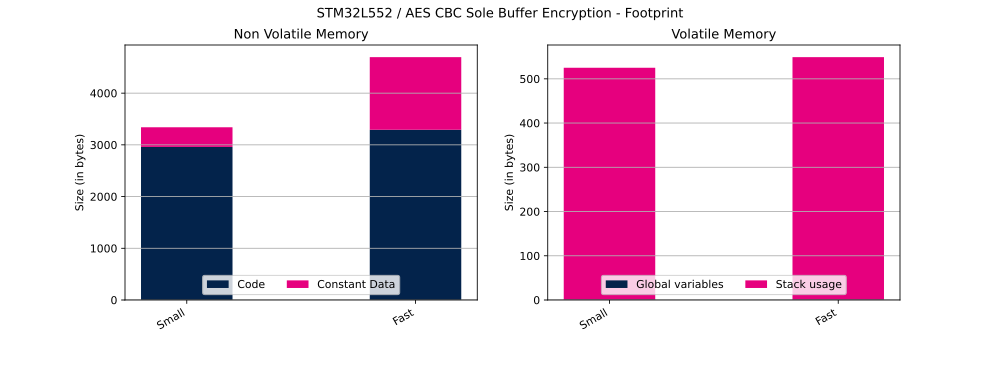
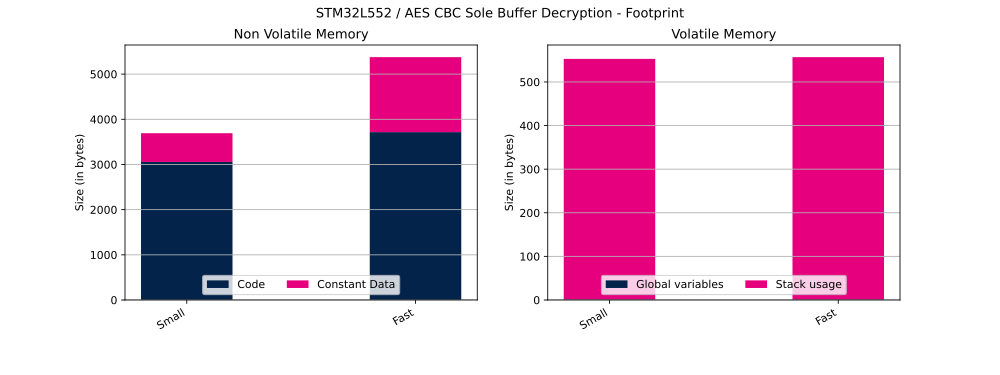
Table below shows flash and RAM usage (in bytes).
| Cipher Operation | Configuration | Code | Constant data | Global Data | Stack usage |
|---|---|---|---|---|---|
| Encryption | Small | 2,960 bytes | 380 bytes | 1 bytes | 524 bytes |
| Encryption | Fast | 3,292 bytes | 1,404 bytes | 1 bytes | 548 bytes |
| Decryption | Small | 3,056 bytes | 636 bytes | 1 bytes | 552 bytes |
| Decryption | Fast | 3,716 bytes | 1,660 bytes | 1 bytes | 556 bytes |
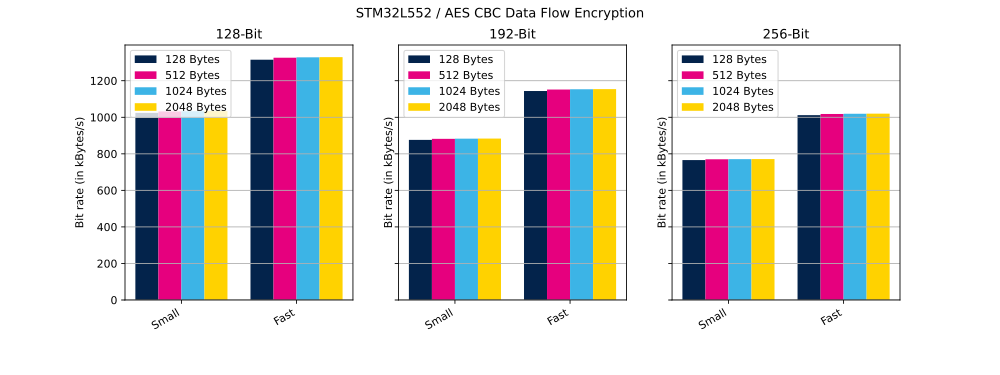
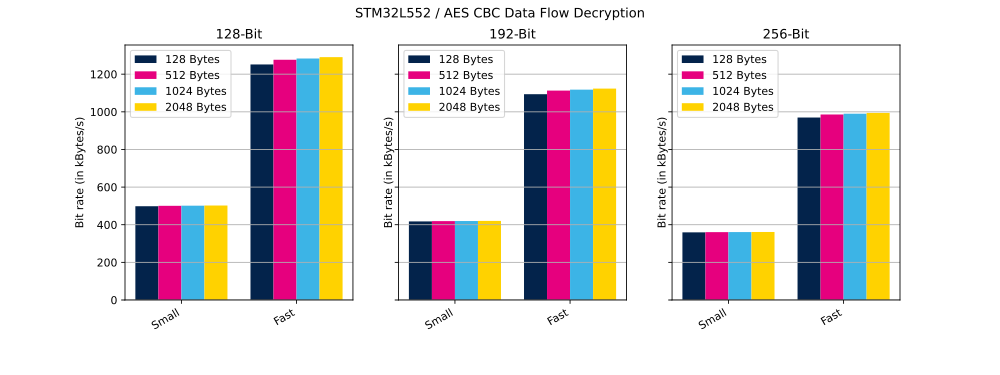
2.1.2. Data flow mode
In this mode, operation is performed in several calls to the CMOX library APIs, as below:
- cmox_cipher_init
- cmox_cipher_setKey
- cmox_cipher_setIV
- cmox_cipher_append: called several times to encrypt or decrypt the whole message by chunk of fixed size
Table below shows the clock cycles and bit rate (in KBytes per second) needed to perform described operation in small and in fast configuration.
| AES Mode | Key size | Message size | Chunk Size | Cipher Operation | Configuration | Cycles | Bit Rate |
|---|---|---|---|---|---|---|---|
| AES CBC | 128Bits | 8,000 bytes | 128 bytes | Encryption | Small | 859,280 | 1,024 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 128 bytes | Encryption | Fast | 669,184 | 1,315 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 512 bytes | Encryption | Small | 852,768 | 1,031 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 512 bytes | Encryption | Fast | 663,696 | 1,325 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 1024 bytes | Encryption | Small | 851,624 | 1,033 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 1024 bytes | Encryption | Fast | 662,616 | 1,328 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 2048 bytes | Encryption | Small | 851,056 | 1,034 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 2048 bytes | Encryption | Fast | 662,112 | 1,329 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 128 bytes | Encryption | Small | 1,004,288 | 876 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 128 bytes | Encryption | Fast | 769,432 | 1,143 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 512 bytes | Encryption | Small | 997,784 | 881 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 512 bytes | Encryption | Fast | 764,032 | 1,151 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 1024 bytes | Encryption | Small | 996,632 | 882 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 1024 bytes | Encryption | Fast | 763,008 | 1,153 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 2048 bytes | Encryption | Small | 996,064 | 883 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 2048 bytes | Encryption | Fast | 762,504 | 1,154 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 128 bytes | Encryption | Small | 1,149,240 | 765 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 128 bytes | Encryption | Fast | 869,920 | 1,011 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 512 bytes | Encryption | Small | 1,142,736 | 770 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 512 bytes | Encryption | Fast | 864,416 | 1,018 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 1024 bytes | Encryption | Small | 1,141,592 | 770 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 1024 bytes | Encryption | Fast | 863,400 | 1,019 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 2048 bytes | Encryption | Small | 1,141,008 | 771 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 2048 bytes | Encryption | Fast | 862,904 | 1,019 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 128 bytes | Decryption | Small | 1,765,960 | 498 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 128 bytes | Decryption | Fast | 703,032 | 1,251 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 512 bytes | Decryption | Small | 1,758,240 | 500 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 512 bytes | Decryption | Fast | 689,304 | 1,276 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 1024 bytes | Decryption | Small | 1,755,760 | 501 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 1024 bytes | Decryption | Fast | 685,704 | 1,283 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 2048 bytes | Decryption | Small | 1,752,592 | 502 kB/s |
| AES CBC | 128Bits | 8,000 bytes | 2048 bytes | Decryption | Fast | 681,856 | 1,290 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 128 bytes | Decryption | Small | 2,107,136 | 417 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 128 bytes | Decryption | Fast | 804,624 | 1,093 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 512 bytes | Decryption | Small | 2,099,456 | 419 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 512 bytes | Decryption | Fast | 790,792 | 1,112 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 1024 bytes | Decryption | Small | 2,096,880 | 419 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 1024 bytes | Decryption | Fast | 787,216 | 1,117 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 2048 bytes | Decryption | Small | 2,093,720 | 420 kB/s |
| AES CBC | 192Bits | 8,000 bytes | 2048 bytes | Decryption | Fast | 783,304 | 1,123 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 128 bytes | Decryption | Small | 2,447,976 | 359 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 128 bytes | Decryption | Fast | 907,496 | 969 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 512 bytes | Decryption | Small | 2,440,272 | 360 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 512 bytes | Decryption | Fast | 892,664 | 985 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 1024 bytes | Decryption | Small | 2,437,816 | 360 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 1024 bytes | Decryption | Fast | 888,864 | 990 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 2048 bytes | Decryption | Small | 2,434,672 | 361 kB/s |
| AES CBC | 256Bits | 8,000 bytes | 2048 bytes | Decryption | Fast | 884,960 | 994 kB/s |
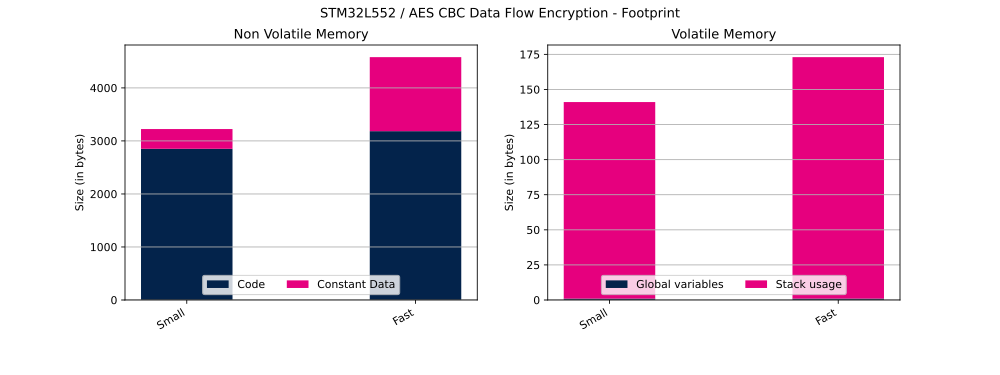
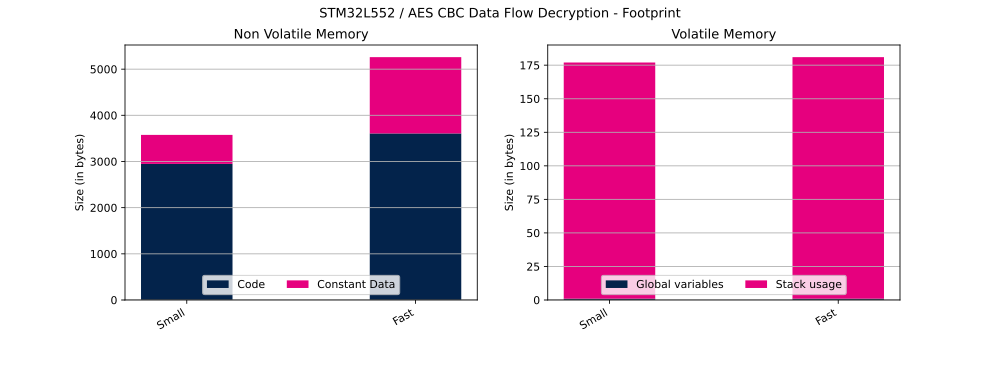
Table below shows flash and RAM usage (in bytes).
| Cipher Operation | Configuration | Code | Constant data | Global Data | Stack usage |
|---|---|---|---|---|---|
| Encryption | Small | 2,852 bytes | 372 bytes | 1 bytes | 140 bytes |
| Encryption | Fast | 3,184 bytes | 1,396 bytes | 1 bytes | 172 bytes |
| Decryption | Small | 2,948 bytes | 628 bytes | 1 bytes | 176 bytes |
| Decryption | Fast | 3,608 bytes | 1,652 bytes | 1 bytes | 180 bytes |
2.2. HASH Digest
In this section we provide the performance results for HASH using different modes of operation:
- Sole buffer: one sole buffer is hashed. Time to perform is given in us.
- Data flow: a big message is hashed by chunk. Bit rate is given in bytes per s.
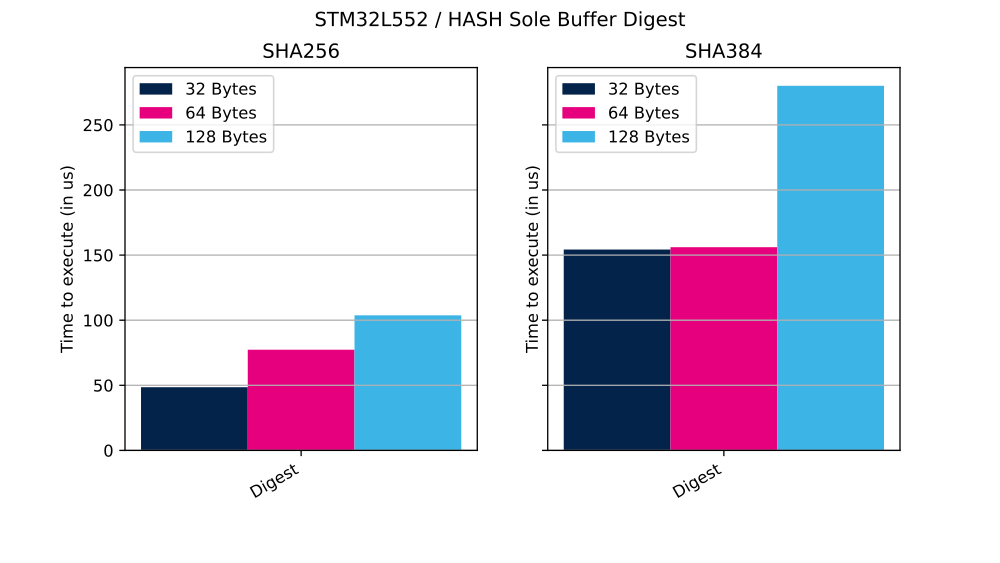
2.2.1. Sole buffer mode
In this mode, the entire message hashing process is managed through a single API call provided by the CMOX library.
Table below shows the clock cycles and time (in µs) needed to perform described operation.
| HASH Mode | Buffer Size | Cycles | Time |
|---|---|---|---|
| SHA256 | 32 bytes | 5,337 | 48 µs |
| SHA256 | 64 bytes | 8,507 | 77 µs |
| SHA256 | 128 bytes | 11,413 | 103 µs |
| SHA384 | 32 bytes | 16,969 | 154 µs |
| SHA384 | 64 bytes | 17,165 | 156 µs |
| SHA384 | 128 bytes | 30,803 | 280 µs |
Table below shows flash and RAM usage (in bytes).
| HASH Mode | Code | Constant data | Global Data | Stack usage |
|---|---|---|---|---|
| SHA256 | 1,780 | 296 bytes | 1 bytes | 564 bytes |
| SHA384 | 3,012 | 744 bytes | 1 bytes | 1,124 bytes |
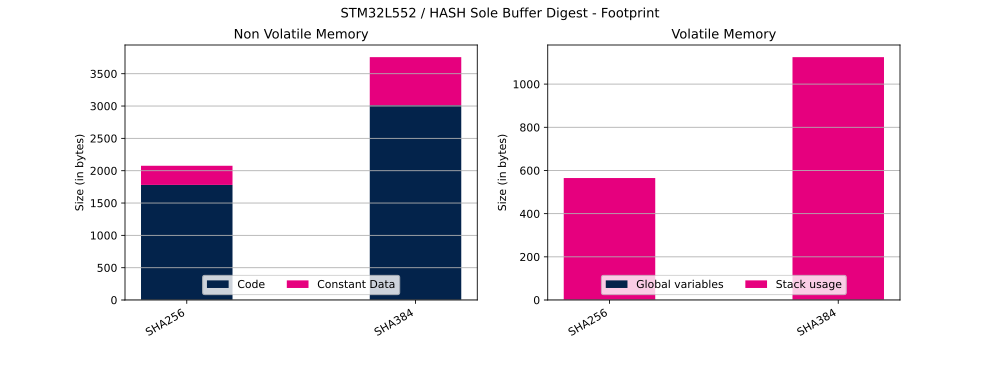
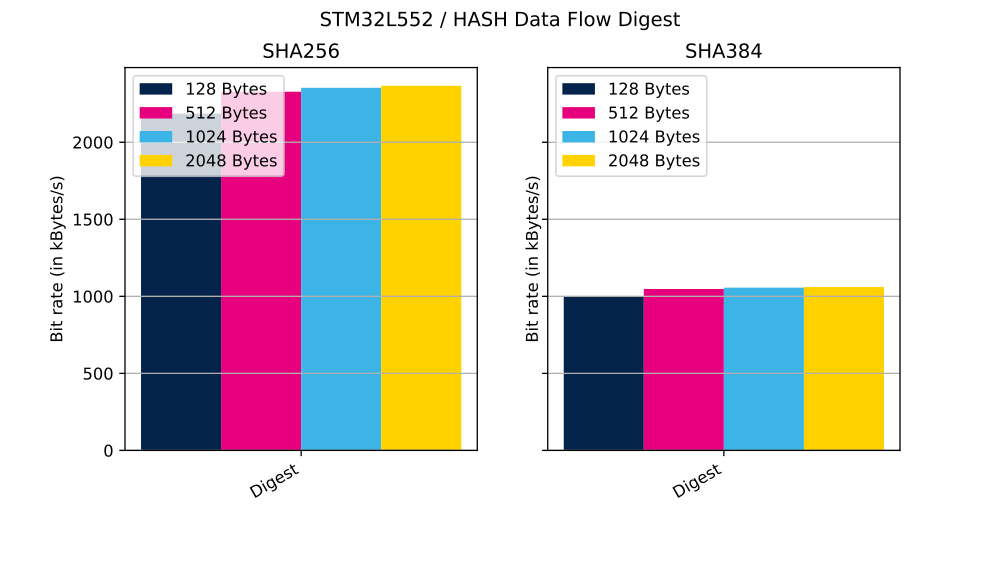
2.2.2. Data flow mode
In this mode, operation is performed in several calls to the CMOX library APIs, as below:
- cmox_hash_init
- cmox_hash_append: called several times to hash the whole message by chunk of fixed size
- cmox_hash_generateTag
Table below shows the clock cycles and bit rate (in KBytes per second) needed to perform described operation.
| HASH Mode | Message size | Chunk Size | Cycles | Bit Rate |
|---|---|---|---|---|
| SHA256 | 8,000 bytes | 128 bytes | 402,655 | 2,185 kB/s |
| SHA256 | 8,000 bytes | 512 bytes | 378,001 | 2,328 kB/s |
| SHA256 | 8,000 bytes | 1024 bytes | 373,926 | 2,353 kB/s |
| SHA256 | 8,000 bytes | 2048 bytes | 371,867 | 2,366 kB/s |
| SHA384 | 8,000 bytes | 128 bytes | 881,240 | 998 kB/s |
| SHA384 | 8,000 bytes | 512 bytes | 840,224 | 1,047 kB/s |
| SHA384 | 8,000 bytes | 1024 bytes | 833,191 | 1,056 kB/s |
| SHA384 | 8,000 bytes | 2048 bytes | 829,645 | 1,060 kB/s |
Table below shows final tag generation done through the call to cmox_hash_generateTag.
| HASH Mode | Cycles | Time |
|---|---|---|
| SHA256 | 4,370 | 39 µs |
| SHA384 | 15,552 | 141 µs |
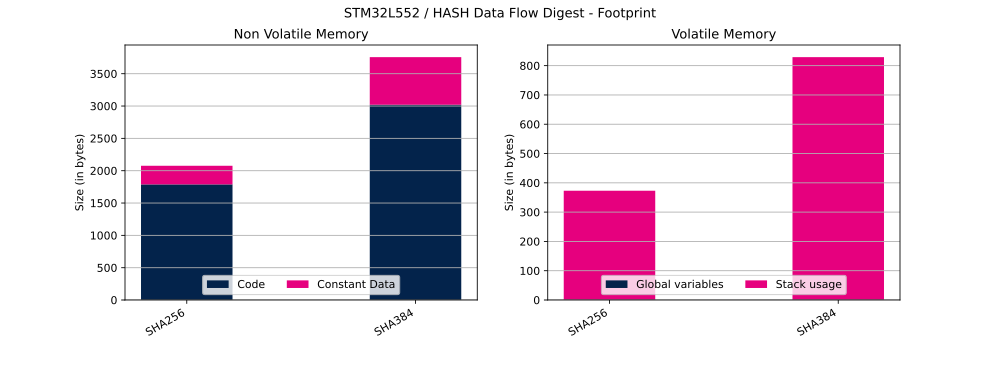
Table below shows flash and RAM usage (in bytes).
| HASH Mode | Code | Constant data | Global Data | Stack usage |
|---|---|---|---|---|
| SHA256 | 1,788 bytes | 288 bytes | 1 bytes | 372 bytes |
| SHA384 | 3,020 bytes | 736 bytes | 1 bytes | 828 bytes |
2.3. ECDSA Signature & Verification
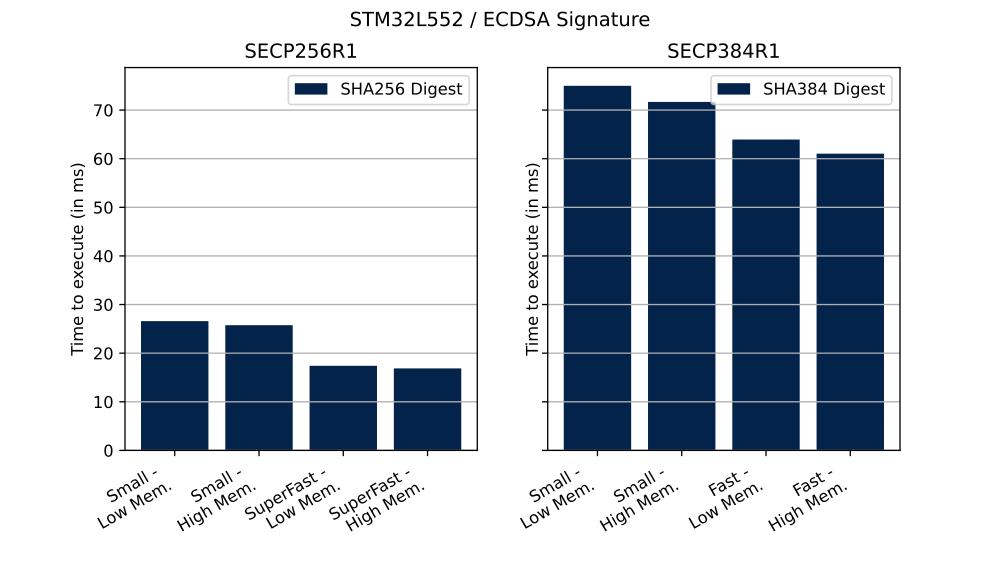
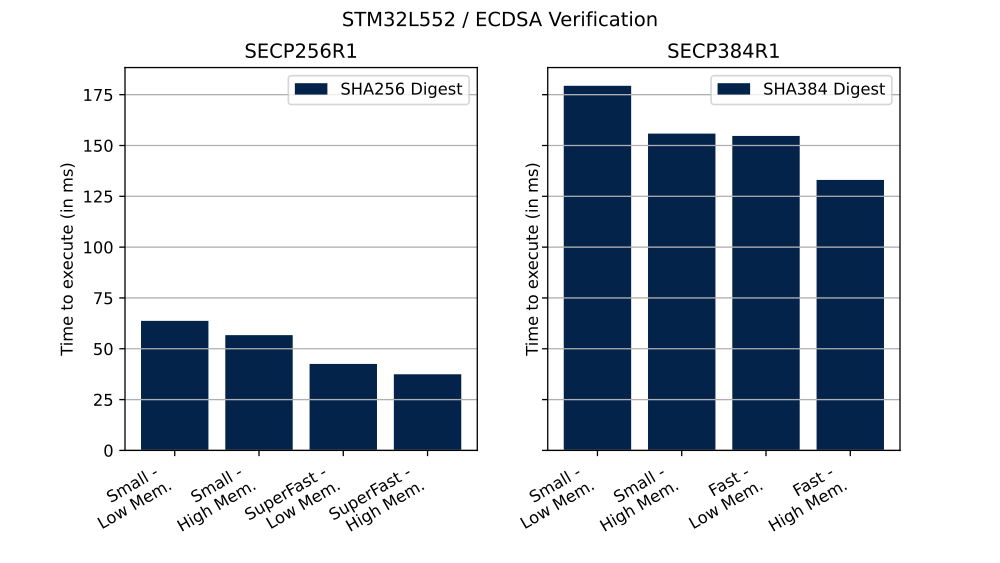
In this section we provide the performance results for ECDSA Signature & Verification.
Table below shows the clock cycles and time (in ms) needed to perform described operation in different configurations.
| Curve | Operation | ECC Mathematics configuration | Curve definition | Cycles | Time |
|---|---|---|---|---|---|
| SECP256R1 | Signature | Small | Low | 2,924,624 | 26 ms |
| SECP256R1 | Signature | Small | High | 2,833,152 | 25 ms |
| SECP256R1 | Signature | SuperFast | Low | 1,914,056 | 17 ms |
| SECP256R1 | Signature | SuperFast | High | 1,856,016 | 16 ms |
| SECP256R1 | Verification | Small | Low | 7,008,992 | 63 ms |
| SECP256R1 | Verification | Small | High | 6,237,136 | 56 ms |
| SECP256R1 | Verification | SuperFast | Low | 4,680,328 | 42 ms |
| SECP256R1 | Verification | SuperFast | High | 4,119,384 | 37 ms |
| SECP384R1 | Signature | Small | Low | 8,249,576 | 74 ms |
| SECP384R1 | Signature | Small | High | 7,884,680 | 71 ms |
| SECP384R1 | Signature | Fast | Low | 7,034,360 | 63 ms |
| SECP384R1 | Signature | Fast | High | 6,713,312 | 61 ms |
| SECP384R1 | Verification | Small | Low | 19,730,496 | 179 ms |
| SECP384R1 | Verification | Small | High | 17,141,648 | 155 ms |
| SECP384R1 | Verification | Fast | Low | 17,015,888 | 154 ms |
| SECP384R1 | Verification | Fast | High | 14,637,488 | 133 ms |
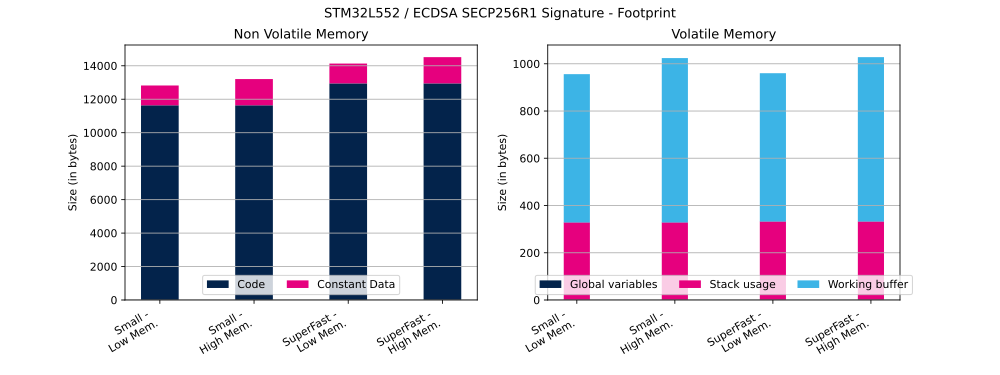
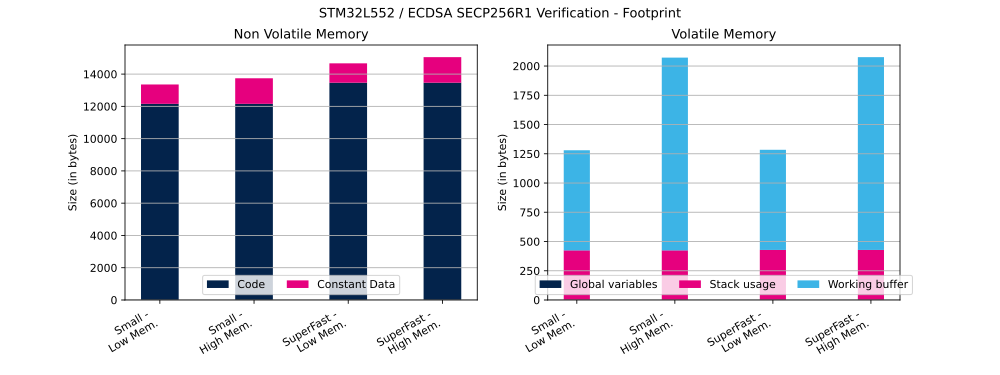
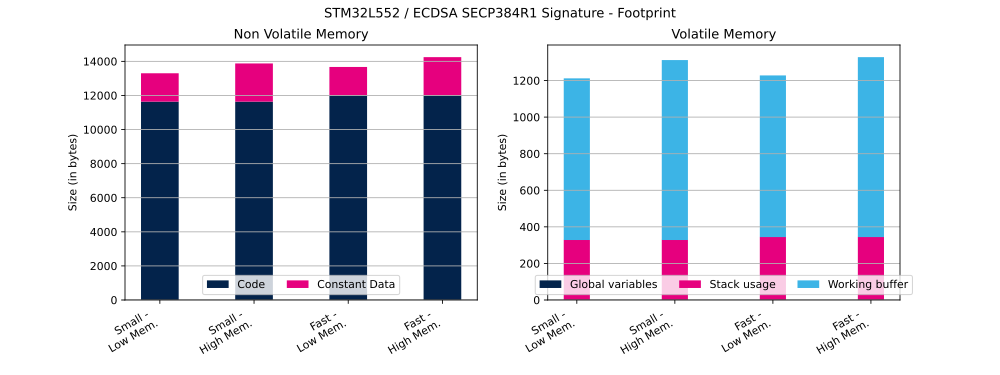
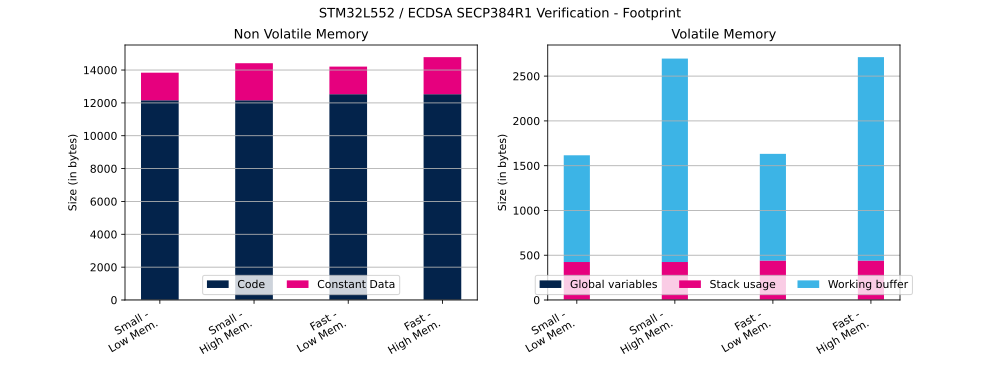
Table below shows ECDSA flash and RAM usage (in bytes).
| Curve | Operation | ECC Mathematics configuration | Curve definition | Code | Constant data | Global Data | Stack usage | Working buffer |
|---|---|---|---|---|---|---|---|---|
| SECP256R1 | Signature | Small | Low | 11,636 bytes | 1,184 bytes | 1 bytes | 328 bytes | 628 bytes |
| SECP256R1 | Signature | Small | High | 11,636 bytes | 1,568 bytes | 1 bytes | 328 bytes | 696 bytes |
| SECP256R1 | Signature | SuperFast | Low | 12,946 bytes | 1,184 bytes | 1 bytes | 332 bytes | 628 bytes |
| SECP256R1 | Signature | SuperFast | High | 12,946 bytes | 1,568 bytes | 1 bytes | 332 bytes | 696 bytes |
| SECP256R1 | Verification | Small | Low | 12,158 bytes | 1,200 bytes | 1 bytes | 424 bytes | 856 bytes |
| SECP256R1 | Verification | Small | High | 12,158 bytes | 1,584 bytes | 1 bytes | 424 bytes | 1,648 bytes |
| SECP256R1 | Verification | SuperFast | Low | 13,468 bytes | 1,200 bytes | 1 bytes | 428 bytes | 856 bytes |
| SECP256R1 | Verification | SuperFast | High | 13,468 bytes | 1,584 bytes | 1 bytes | 428 bytes | 1,648 bytes |
| SECP384R1 | Signature | Small | Low | 11,636 bytes | 1,664 bytes | 1 bytes | 328 bytes | 884 bytes |
| SECP384R1 | Signature | Small | High | 11,636 bytes | 2,240 bytes | 1 bytes | 328 bytes | 984 bytes |
| SECP384R1 | Signature | Fast | Low | 12,006 bytes | 1,664 bytes | 1 bytes | 344 bytes | 884 bytes |
| SECP384R1 | Signature | Fast | High | 12,006 bytes | 2,240 bytes | 1 bytes | 344 bytes | 984 bytes |
| SECP384R1 | Verification | Small | Low | 12,158 bytes | 1,680 bytes | 1 bytes | 424 bytes | 1,192 bytes |
| SECP384R1 | Verification | Small | High | 12,158 bytes | 2,256 bytes | 1 bytes | 424 bytes | 2,272 bytes |
| SECP384R1 | Verification | Fast | Low | 12,528 bytes | 1,680 bytes | 1 bytes | 440 bytes | 1,192 bytes |
| SECP384R1 | Verification | Fast | High | 12,528 bytes | 2,256 bytes | 1 bytes | 440 bytes | 2,272 bytes |
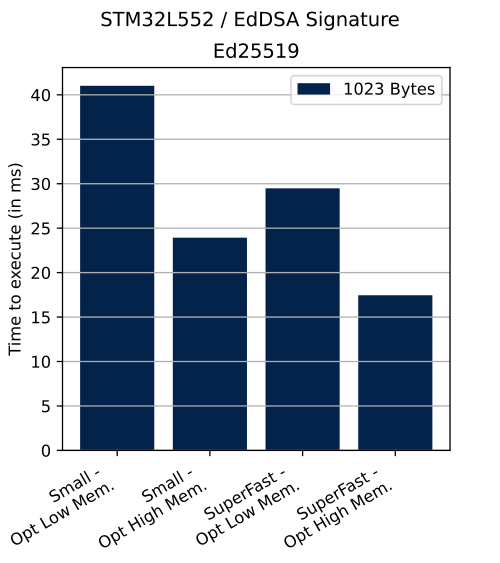
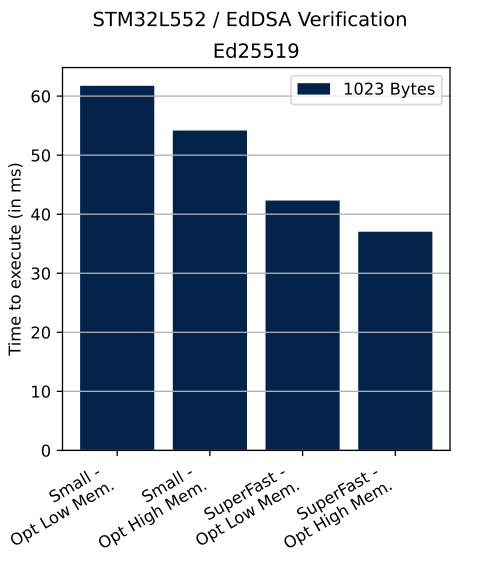
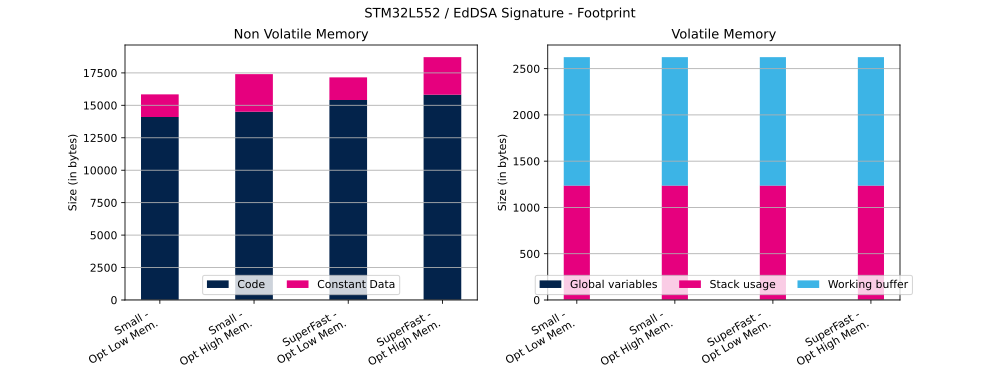
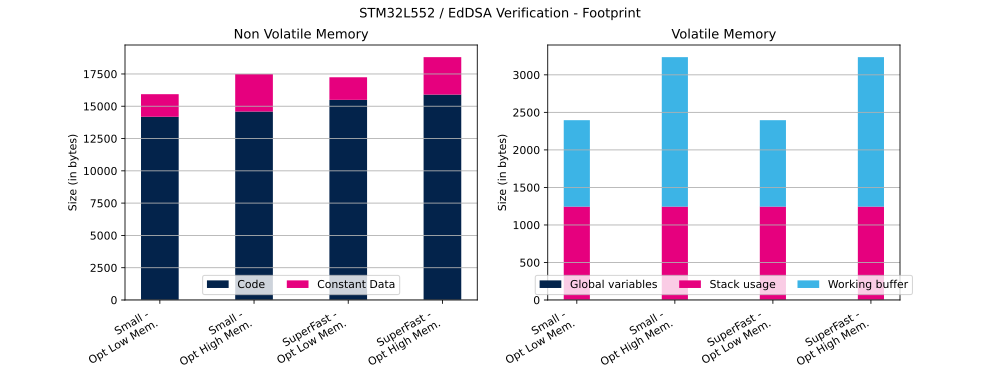
2.4. EdDSA Signature & Verification
In this section we provide the performance results for EdDSA Signature & Verification.
Table below shows the clock cycles and time (in ms) needed to perform described operation in different configurations.
| Curve | Message size | Operation | ECC Mathematics configuration | Curve definition | Cycles | Time |
|---|---|---|---|---|---|---|
| Ed25519 | 1,023 bytes | Signature | Small | OptLow | 4,511,896 | 41 ms |
| Ed25519 | 1,023 bytes | Signature | Small | OptHigh | 2,632,648 | 23 ms |
| Ed25519 | 1,023 bytes | Signature | SuperFast | OptLow | 3,242,920 | 29 ms |
| Ed25519 | 1,023 bytes | Signature | SuperFast | OptHigh | 1,919,992 | 17 ms |
| Ed25519 | 1,023 bytes | Verification | Small | OptLow | 6,792,304 | 61 ms |
| Ed25519 | 1,023 bytes | Verification | Small | OptHigh | 5,958,792 | 54 ms |
| Ed25519 | 1,023 bytes | Verification | SuperFast | OptLow | 4,654,664 | 42 ms |
| Ed25519 | 1,023 bytes | Verification | SuperFast | OptHigh | 4,072,960 | 37 ms |
Table below shows EdDSA flash and RAM usage (in bytes).
| Curve | Message size | Operation | ECC Mathematics configuration | Curve definition | Code | Constant data | Global Data | Stack usage | Working buffer |
|---|---|---|---|---|---|---|---|---|---|
| Ed25519 | 1,023 bytes | Signature | Small | OptLow | 14,100 bytes | 1,744 bytes | 1 bytes | 1,236 bytes | 1,388 bytes |
| Ed25519 | 1,023 bytes | Signature | Small | OptHigh | 14,506 bytes | 2,896 bytes | 1 bytes | 1,236 bytes | 1,388 bytes |
| Ed25519 | 1,023 bytes | Signature | SuperFast | OptLow | 15,410 bytes | 1,744 bytes | 1 bytes | 1,236 bytes | 1,388 bytes |
| Ed25519 | 1,023 bytes | Signature | SuperFast | OptHigh | 15,816 bytes | 2,896 bytes | 1 bytes | 1,236 bytes | 1,388 bytes |
| Ed25519 | 1,023 bytes | Verification | Small | OptLow | 14,186 bytes | 1,748 bytes | 1 bytes | 1,244 bytes | 1,152 bytes |
| Ed25519 | 1,023 bytes | Verification | Small | OptHigh | 14,592 bytes | 2,900 bytes | 1 bytes | 1,244 bytes | 1,992 bytes |
| Ed25519 | 1,023 bytes | Verification | SuperFast | OptLow | 15,496 bytes | 1,748 bytes | 1 bytes | 1,244 bytes | 1,152 bytes |
| Ed25519 | 1,023 bytes | Verification | SuperFast | OptHigh | 15,902 bytes | 2,900 bytes | 1 bytes | 1,244 bytes | 1,992 bytes |
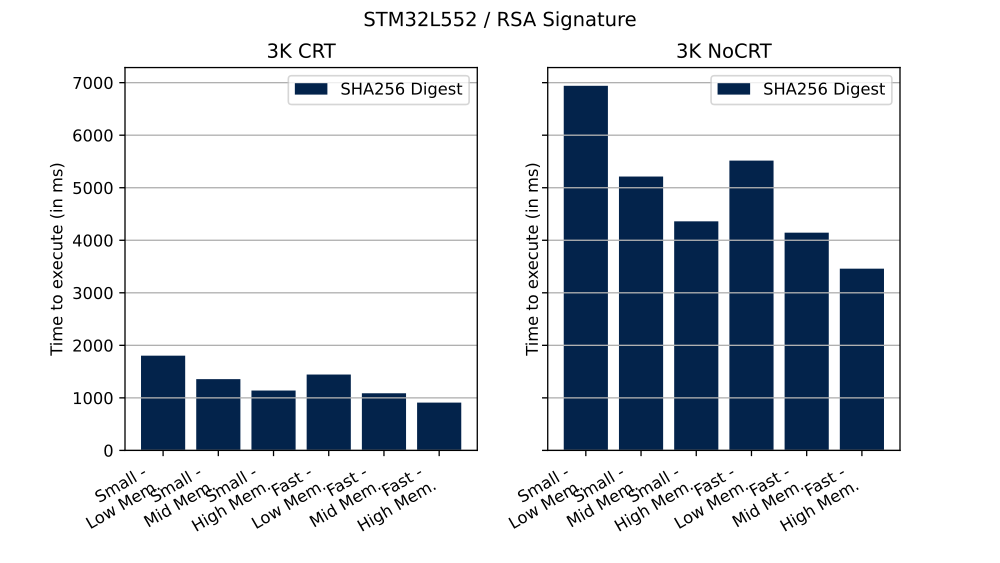
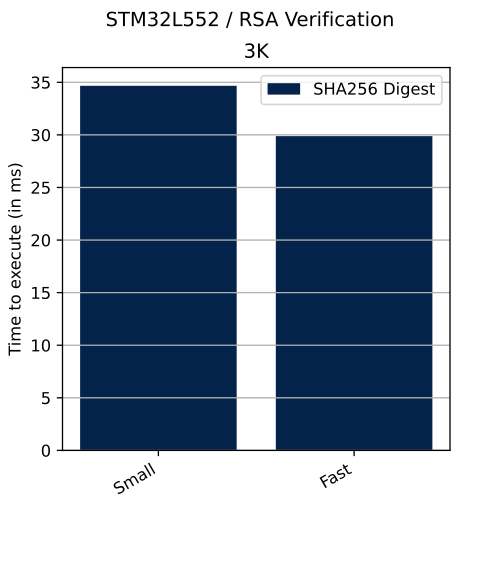
2.5. RSA Signature & Verification
In this section we provide the performance results for RSA Signature & Verification.
Table below shows the clock cycles and time (in ms) needed to perform described operation in different configurations.
| PKCS#1 | Priv. key mod. exp. method | Hash method | Modulus size | Operation | RSA Mathematics configuration | Priv. key mod. exp.implementation | Cycles | Time |
|---|---|---|---|---|---|---|---|---|
| v2.2 | CRT | SHA-256 | 3K | Signature | Small | Low | 198,353,328 | 1,803 ms |
| v2.2 | CRT | SHA-256 | 3K | Signature | Small | Mid | 149,293,056 | 1,357 ms |
| v2.2 | CRT | SHA-256 | 3K | Signature | Small | High | 125,370,232 | 1,139 ms |
| v2.2 | CRT | SHA-256 | 3K | Signature | Fast | Low | 158,894,368 | 1,444 ms |
| v2.2 | CRT | SHA-256 | 3K | Signature | Fast | Mid | 119,683,376 | 1,088 ms |
| v2.2 | CRT | SHA-256 | 3K | Signature | Fast | High | 100,074,160 | 909 ms |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Small | Low | 763,443,336 | 6,940 ms |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Small | Mid | 573,386,688 | 5,212 ms |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Small | High | 479,617,744 | 4,360 ms |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Fast | Low | 606,866,800 | 5,516 ms |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Fast | Mid | 455,903,856 | 4,144 ms |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Fast | High | 380,471,192 | 3,458 ms |
| v2.2 | n/a | SHA-256 | 3K | Verification | Small | n/a | 3,813,464 | 34 ms |
| v2.2 | n/a | SHA-256 | 3K | Verification | Fast | n/a | 3,286,840 | 29 ms |
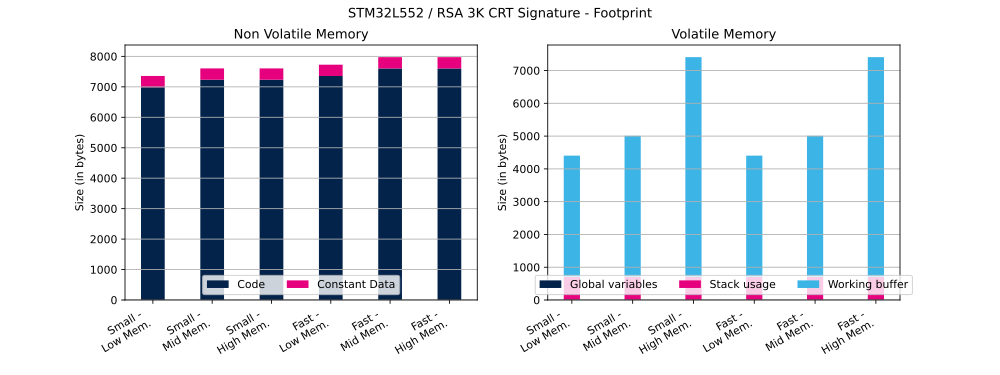
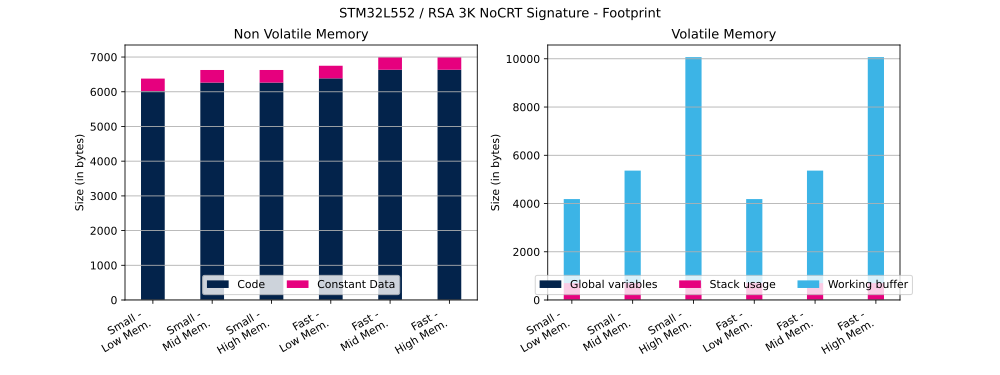
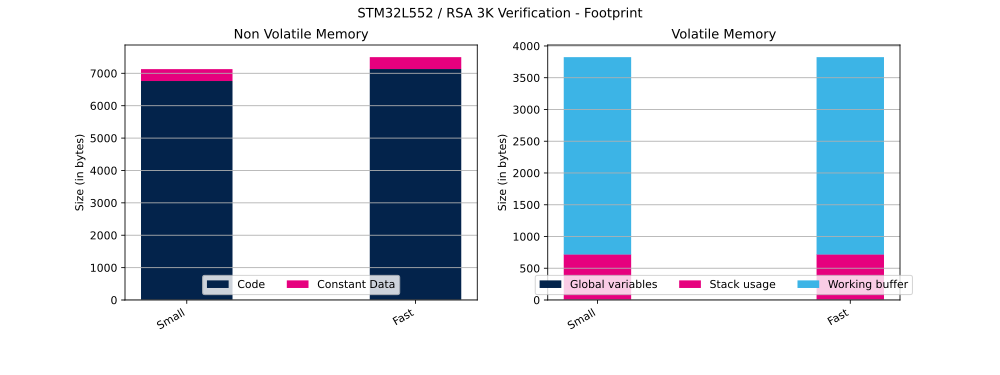
Table below shows RSA flash and RAM usage (in bytes).
| PKCS#1 | Priv. key mod. exp. method | Hash method | Modulus size | Operation | RSA Mathematics configuration | Priv. key mod. exp.implementation | Code | Constant data | Global Data | Stack usage | Working buffer |
|---|---|---|---|---|---|---|---|---|---|---|---|
| v2.2 | CRT | SHA-256 | 3K | Signature | Small | Low | 6,986 bytes | 371 bytes | 5 bytes | 700 bytes | 3,704 bytes |
| v2.2 | CRT | SHA-256 | 3K | Signature | Small | Mid | 7,234 bytes | 371 bytes | 5 bytes | 700 bytes | 4,308 bytes |
| v2.2 | CRT | SHA-256 | 3K | Signature | Small | High | 7,234 bytes | 371 bytes | 5 bytes | 700 bytes | 6,708 bytes |
| v2.2 | CRT | SHA-256 | 3K | Signature | Fast | Low | 7,356 bytes | 371 bytes | 5 bytes | 700 bytes | 3,704 bytes |
| v2.2 | CRT | SHA-256 | 3K | Signature | Fast | Mid | 7,604 bytes | 371 bytes | 5 bytes | 700 bytes | 4,308 bytes |
| v2.2 | CRT | SHA-256 | 3K | Signature | Fast | High | 7,604 bytes | 371 bytes | 5 bytes | 700 bytes | 6,708 bytes |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Small | Low | 6,016 bytes | 363 bytes | 5 bytes | 700 bytes | 3,484 bytes |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Small | Mid | 6,264 bytes | 363 bytes | 5 bytes | 700 bytes | 4,664 bytes |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Small | High | 6,264 bytes | 363 bytes | 5 bytes | 700 bytes | 9,368 bytes |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Fast | Low | 6,386 bytes | 363 bytes | 5 bytes | 700 bytes | 3,484 bytes |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Fast | Mid | 6,634 bytes | 363 bytes | 5 bytes | 700 bytes | 4,664 bytes |
| v2.2 | No CRT | SHA-256 | 3K | Signature | Fast | High | 6,634 bytes | 363 bytes | 5 bytes | 700 bytes | 9,368 bytes |
| v2.2 | n/a | SHA-256 | 3K | Verification | Small | n/a | 6,762 bytes | 367 bytes | 5 bytes | 716 bytes | 3,108 bytes |
| v2.2 | n/a | SHA-256 | 3K | Verification | Fast | n/a | 7,132 bytes | 367 bytes | 5 bytes | 716 bytes | 3,108 bytes |