How to start with OEM-iROT access on STM32H503![]() 45min
45min
Target description
This tutorial shows how to make a provisioning and then a full regression on a STM32H503 device. Provisioning process goes through 3 steps :
- Initial Option Bytes programming
- Code image generation and flashing
- Password provisioning
The last step shows a full regression.
Prerequisites
- knowledge of STM32CubeProgrammer
- knowledge of JTAG / SWD interface
Hardware
- Nucleo MB1814 with STM32H503
Required tools
- STM32CubeProgrammer[1] Software programming tool for STM32 (v2.13.0 min)
- Including STM32TrustedPackageCreator
- STM32Cube_FW_H5_V1.0.0 or later
- IAR Embedded Workbench v9.20.1
- Tera Term or equivalent terminal emulator
Literature
- UM2237 STM32CubeProgrammer software description
- UM2238 STM32 Trusted Package Creator tool software description
- AN5054 Secure programming using STM32CubeProgrammer
- AN2606 STM32 microcontroller system memory boot mode
Environment setup
Before starting, the first step is to prepare the environment to be able to go through the DA process.
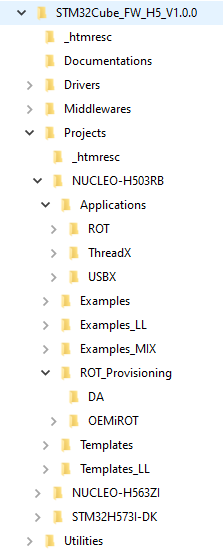
- Download the STM32CubeFW_H5 Cube firmware
A directory NUCLEO-H503RB is included in the Projects directory
- STM32CubeProgrammer default folder is : C:\Program Files\STMicroelectronics\STM32Cube\STM32CubeProgrammer
In case the STM32CubeProgrammer has not been installed in the default folder, the customized installation paths need to be updated in the following script :NUCLEO-H503RB\ROT_Provisioning\env.bat
:: ==============================================================================
:: General
:: ==============================================================================
:: Configure tools installation path
set stm32programmercli="C:\Program Files\STMicroelectronics\STM32Cube\STM32CubeProgrammer\bin\STM32_Programmer_CLI.exe"
set stm32tpccli="C:\Program Files\STMicroelectronics\STM32Cube\STM32CubeProgrammer\bin\STM32TrustedPackageCreator_CLI.exe"
1. Step 1 : Configuration management - OEMiROT Keys generation
At this step the following keys will be generated:
- ECDSA-256 encryption private key
- ECDSA-256 encryption public key
- ECDSA-256 authentication key
These keys will be used to encrypt and authenticate the user application.
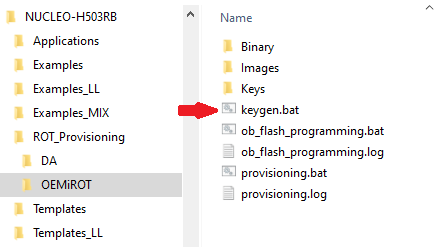
Run the provided script Keygen.bat :
Once you get the success message,
![]() keys are well generated in folder Projects\NUCLEO-H503RB\ROT_Provisioning\OEMiROT\Keys.
keys are well generated in folder Projects\NUCLEO-H503RB\ROT_Provisioning\OEMiROT\Keys.
2. Step 2 : Code and data image generation
Check that the STM32H5 IAR provided patch is correctly installed and check that your IAR Embedded Workbench version is recent enough.
Two code examples for IAR Embedded Workbench are provided
- OEMiROT_Boot corresponds to the Secure Boot.
It performs authenticity and integrity checks of the project firmware and data images.
- OEMiROT_Appli is an example of application managed by OEMiROT
OEMiROT_Boot project compilation
- Open the Project.eww located in the EWARM directory : ..\Projects\NUCLEO-H503RB\Applications\ROT\OEMiROT_Boot\EWARM
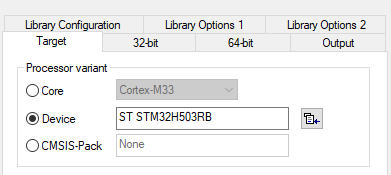
- Open Project -> Option -> General Options : The device and CPU core should be automatically recognized and you should see the following windows
If the device is not recognized, check that the STM32H5 IAR provided patch is correctly installed check that your IAR Embedded Workbench version is recent enough
- Perform: Project -> Rebuild all (don’t upload the code, only perform a compilation)
The following binary is created:…..\Projects\NUCLEO-H503RB\Applications\ROT\OEMiROT_Boot\Binary\OEMiROT_Boot.bin
OEMiROT_Appli project compilation
- Open the Project.eww located in the EWARM directory :
..\Projects\NUCLEO-H503RB\Applications\ROT\OEMiROT_Appli\EWARM
- Open Project -> Option -> General Options
The device and CPU core should be automatically recognized.
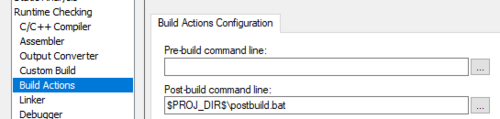
- Open Project -> Option -> Build Actions
Here is the command line which will create an image of the code with STM32Cube Package Creator:
- Perform: Project -> Rebuild all (don’t upload the code, only perform a compilation)
The following image is created: …..\ Projects\NUCLEO-H503RB\Applications\ROT\OEMiROT_Appli\Binary\rot_app_enc_sign.hex
Data generation (if Data image is enabled)