1. Generic boot sequence[edit source]
1.1. Linux start-up[edit source]
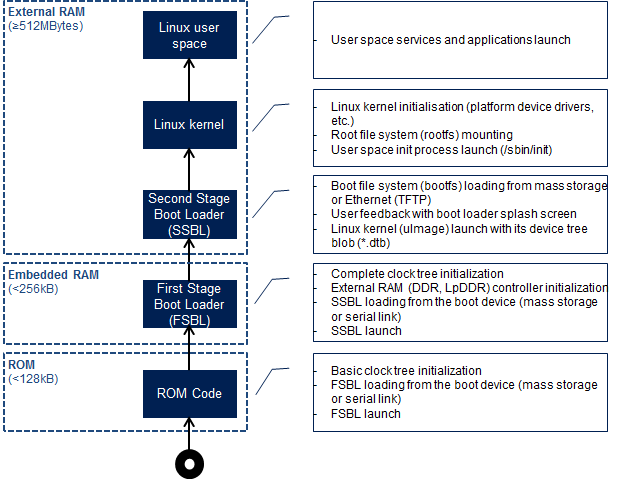
Starting Linux® on a processor is done in several steps that progressively initialize the platform peripherals and memories. These steps are explained in the following parapraphs and illustrated by the diagram on the right, which also gives typical memory sizes for each stage.
1.1.1. ROM code[edit source]
The ROM code is a piece of software that takes its name from the read only memory (ROM) where it is stored. It fits in a few tens of Kbytes and maps its data in embedded RAM. It is the first code executed by the processor, and it embeds all the logic needed to select the boot device (serial link or Flash) from which the first-stage boot loader (FSBL) is loaded to the embedded RAM.
1.1.2. First stage boot loader (FSBL)[edit source]
Among other things, the first stage boot loader (FSBL) initializes (part of) the clock tree and the external RAM controller. Finally, the FSBL loads the second-stage boot loader (SSBL) into the external RAM and jumps to it.
The Trusted Firmware-A (TF-A) and U-Boot secondary program loader (U-Boot SPL) are two possible FSBLs.
1.1.3. Second-stage boot loader (SSBL)[edit source]
The second-stage boot loader (SSBL) runs in a wide RAM so it can implement complex features (USB, Ethernet, display, and so on), that are very useful to make Linux kernel loading more flexible (from a Flash device, a network, and so on), and user-friendly (by showing a splash screen to the user). U-Boot is commonly used as a Linux bootloader in embedded systems.
1.1.4. Linux kernel space[edit source]
The Linux kernel is started in the external memory and it initializes all the peripheral drivers that are needed on the platform.
1.1.5. Linux user space[edit source]
Finally, the Linux kernel hands control to the user space starting the init process that runs all initialization actions described in the root file system (rootfs), including the application framework that exposes the user interface (UI) to the user.
1.2. Other services start-up[edit source]
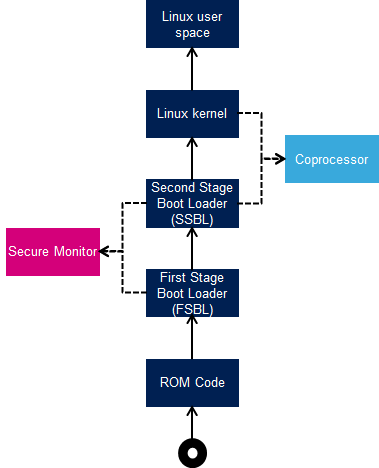
In addition to Linux startup, the boot chain can also handle the start-up of other services.
For instance, for the STM32MP15, the boot chain starts:
- the secure monitor , supported by the Arm® Cortex®-A secure context (TrustZone). Examples of use of a secure monitor are: user authentication, key storage, and tampering management.
- the coprocessor firmware, running on the Arm Cortex-M core. This can be used to offload real-time or low-power services.
The dotted lines in the diagram on the right mean that:
- the secure monitor can be started by the first stage boot loader (FSBL) or the second stage boot loader (SSBL)
- the coprocessor can be started by the second stage boot loader (SSBL), known as “early boot”, or Linux kernel
2. STM32MP boot sequence[edit source]
2.1. Diagram frames and legend[edit source]
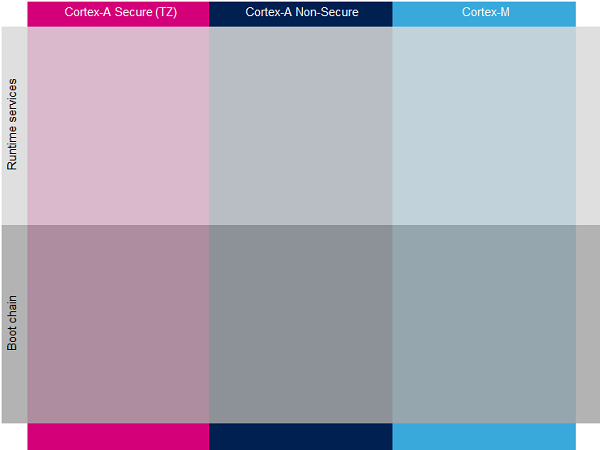
The hardware execution contexts are shown with vertical frames in the boot diagrams:
- the Arm Cortex-A secure context, in pink
- the Arm Cortex-A non-secure context, in dark blue
- the Arm Cortex-M context, in light blue
The horizontal frame in:
- the bottom part shows the boot chain
- the top part shows the runtime services, that are installed by the boot chain
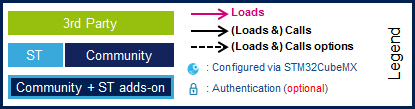
The legend on the right shows how information about the various components shown in the frames, and which are involved in the boot process, is highlighted:
- The box color shows the component source code origin
- The arrows show the loading and calling actions between the components
- The Cube logo is used on the top right corner of components that can be configured via STM32CubeMX
- The lock show the components that can be authenticated during the boot process
2.2. STM32MP boot chains[edit source]
2.2.1. Overview[edit source]
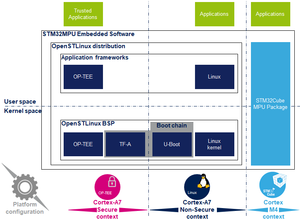
Two different boot chain flavors are supported on STM32MP processors with STM32MPU Embedded Software:
- The trusted boot chain uses Trusted Firmware-A (TF-A) as the FSBL, so it should fulfill all the requirements for security-sensitive customers, and it uses U-Boot as the SSBL. Note that the authentication is optional with this boot chain, so it can run on any STM32MP device. security variant (that is, with or without the Secure boot). The trusted boot chain is the default solution delivered by STMicroelectronics, with a complete feature set (for example, all Flash devices are supported).
- The basic boot chain is also available to generate both the FSBL (U-Boot SPL) and SSBL (U-Boot) from a unique piece of source code, U-Boot. It is only upstreamed with a limited number of features, and the U-Boot community is able to extend this.
2.2.2. STM32MP15 case[edit source]
2.2.2.1. Overview[edit source]
The diagrams below illustrate the two boot chain flavors availble on the STM32MP15: the trusted boot chain and the basic boot chain.
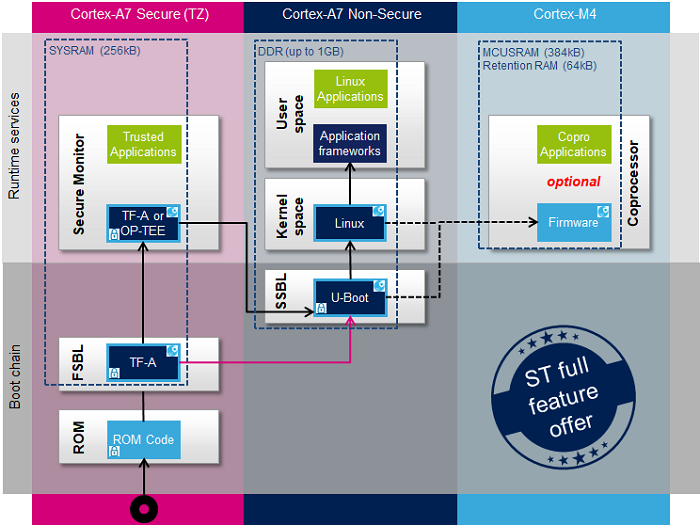
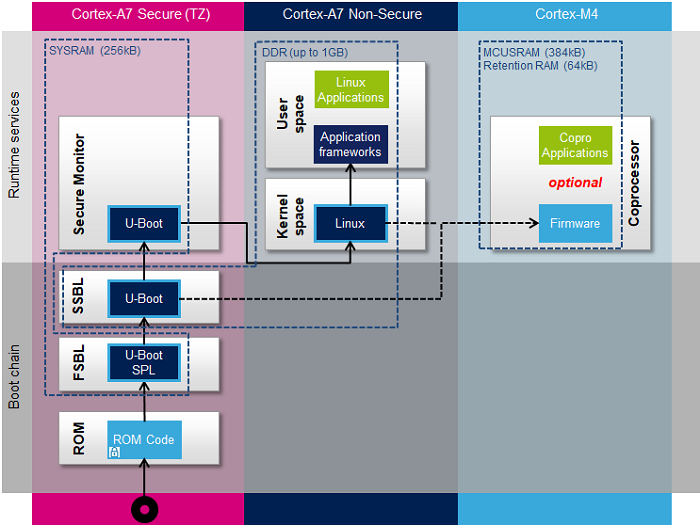
Notes:
- The second-stage boot loader (SSBL) can run in ARM Secure/Trustzone mode (basic boot chain) or Non-Secure mode (trusted boot chain).
- The STM32MP coprocessor can be started at the SSBL level by the U-Boot early boot feature or, later, by the Linux remoteproc framework, depending on the application startup time-targets.
2.2.2.2. ROM code[edit source]
The ROM code starts the processor in secure mode. It supports the FSBL authentication and offers authentication services to the FSBL.
2.2.2.3. First stage boot loader (FSBL)[edit source]
The FSBL is executed from the SYSRAM.
Among other things, this boot loader initializes (part of) the clock tree and the DDR controller. Finally, the FSBL loads the second-stage boot loader (SSBL) into the DDR external RAM and jumps to it.
The Trusted Firmware-A (TF-A) and U-Boot secondary program loader (U-Boot SPL) are the two possible FSBLs on the STM32MP15, for the trusted boot chain and the basic boot chain, respectively.
2.2.2.4. Second stage boot loader (SSBL)[edit source]
The second-stage boot loader (SSBL) runs in a wide RAM so it can implement complex features (USB, Ethernet, display, and so on), that are very useful to make Linux kernel loading (from a Flash device, a network, and so on) more flexible, and user-friendly (by showing a splash screen to the user).
U-Boot is commonly used as a bootloader in embedded software.
2.2.2.5. Linux[edit source]
Linux® is OS is loaded in DDR by U-Boot and executed in the non-secure context.
2.2.2.6. Secure OS / Secure Monitor[edit source]
The Cortex-A7 secure world can implement a minimal secure monitor (from TF-A or U-Boot) or a real secure OS, such as OP-TEE.
2.2.2.7. Coprocessor firmware[edit source]
The coprocessor STM32Cube firmware can be started at the SSBL level by U-Boot with the remoteproc feature (rproc command) or, later, by Linux remoteproc framework, depending on the application startup time-targets.
2.2.3. Boot chains features set[edit source]
As previously mentionned, the Basic boot chain has a limited features set versus the Trusted boot chain (which is the default solution delivered by STMicroelectronics). Here is the list of supported features for the Trusted and Basic boot chains:
| Features | Trusted boot chain | Basic boot chain |
|---|---|---|
| Boot device support | ||
| eMMC | Supported | Supported |
| SDCard | Supported | Supported |
| NOR | Supported | Supported |
| NAND | Supported | Not supported |
| Flash programming via UART | Supported | Not supported |
| Flash programming via USB | Supported | Not supported |
| Device control | ||
| DDR initialization | Supported | Supported |
| PMIC management | Supported | Supported |
| System shutdown | Supported | Not supported |
| SMP CPU boot and reset | Supported | supported |
| Low power management | Supported | Not supported |
| Security features | ||
| Authentication ECDSA Based | Supported | Not supported |
| Secure boot TZEN=1 - SMC Firewalling | Supported | Not supported |
| Cortex-M4 isolation control | Supported | Not supported |
| Non secure boot - Unlimited access to RCC and PWR | Supported | Supported |
| HSI/CSI Calibration | Supported | Not supported |
| Security Tamper | Supported | Not supported |
| Security OTP | Supported | Not supported |
| Security IWDG1 | Supported | Not supported |