1. Environment setup
As explained in SFI Image generation, the SFI image generation and the SFI image test rely on the SMAK.
So, please follow SMAK prerequisites and SMAK package contents for the SFI environment setup.
2. Development @ OEM: Firmware creation
The purpose of this SFI service is to securely install the OEM Firmware developed with Secure Manager.
So, in order to use this SFI service, the OEM must develop its nonsecure application with the SMAK development phase.
The OEM Firmware file is .hex extension.
ST provides an application example in \STM32Cube_H5_V1.1.0\Firmware\Projects\STM32H573I-DK\Applications\ROT\SMAK_Appli\Binary\appli_enc_sign.hex.
3. Secure Room @ OEM: SFI image generation and HSM provisioning
3.1. SFI image generation
Once the OEM completes its nonsecure application development, the OEM must prepare and test the final encrypted image (SFI image) used for OEM secure manufacturing with the SMAK production preparation phase.
3.1.1. step by step procedure
3.1.1.1. Step 0
- Replace the default applications with OEM application (let's call it oem_app.hex)
cp oem_app.hex \STM32Cube_H5_V1.1.0\Firmware\Projects\STM32H573I-DK\ROT_Provisioning\SM\Binary\appli_0.hex
cp oem_app.hex \STM32Cube_H5_V1.1.0\Firmware\Projects\STM32H573I-DK\ROT_Provisioning\SM\Binary\appli_1.hex
- with unlicensed module:
- copy module in \STM32Cube_H5_V1.1.0\Firmware\Projects\STM32H573I-DK\ROT_Provisioning\SM\Binary
cp module.hex \STM32Cube_H5_V1.1.0\Firmware\Projects\STM32H573I-DK\ROT_Provisioning\SM\Binary
- modify \STM32Cube_H5_V1.1.0\Firmware\Projects\STM32H573I-DK\ROT_Provisioning\SM\provisioning.bat with
line 316:
add
set modules= --firmware "%projectdir%module.hex"
- modify \STM32Cube_H5_V1.1.0\Firmware\Projects\STM32H573I-DK\ROT_Provisioning\SM\provisioning.sh with
line 419:
add
set modules= --firmware "%projectdir%module.hex"
3.1.1.2. Step 1
Follow SMAK SFI image generation
After this step, the SFI image is generated.
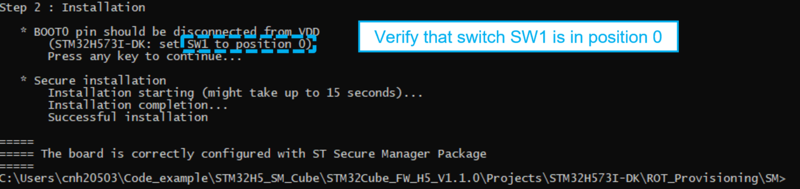
3.1.1.3. Step 2
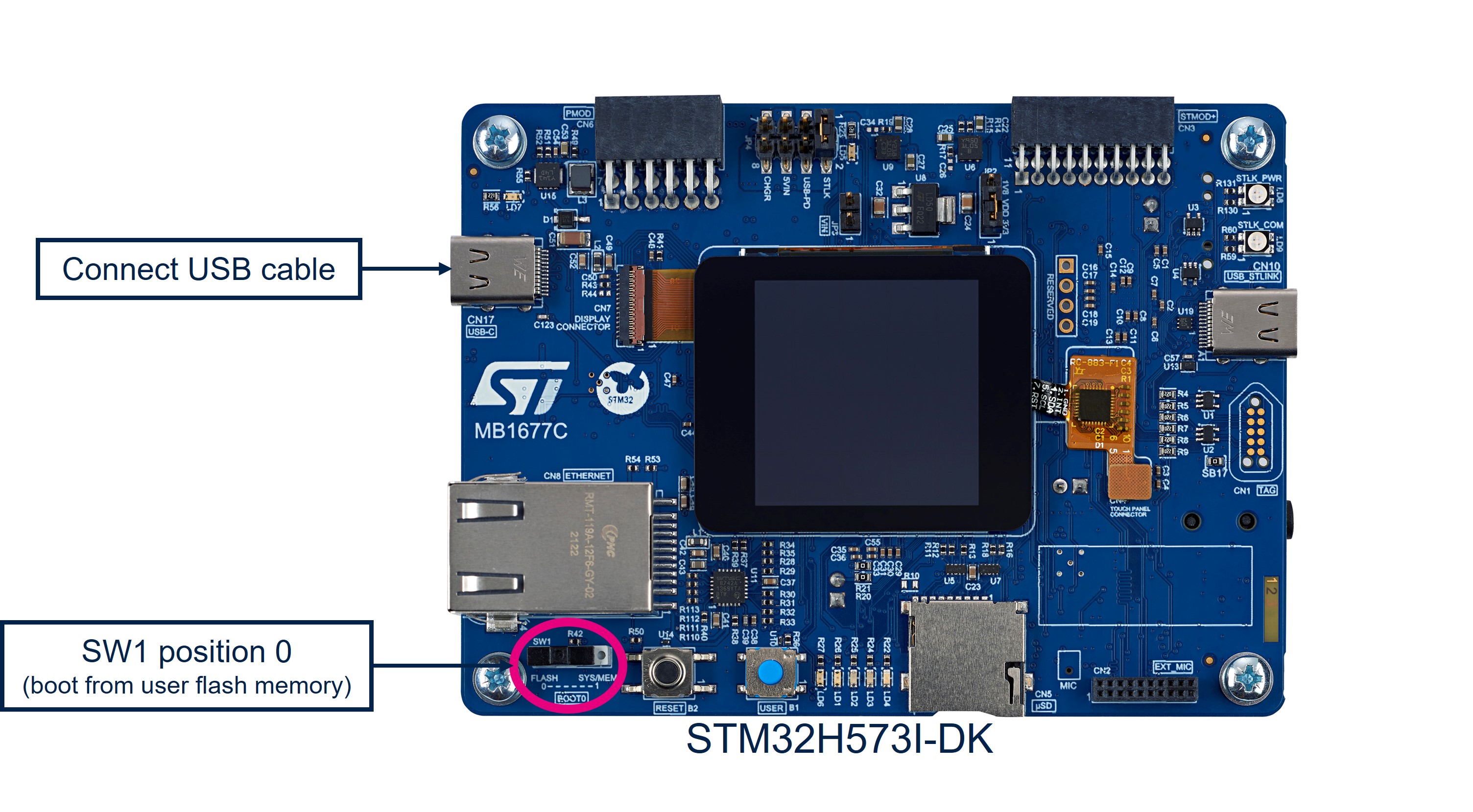
In order to test the generated SFI image, please follow the indications of the script as shown in the figure below.
The step 2 of the script installs the Secure Manager, the OEM application application and the module (if any).
Once the installation is complete, the OEM application is running on target.
In case of issue:
- Check the provisioning.log file (in directory: STM32Cube_H5_V1.1.0\Firmware\Projects\STM32H573I-DK\ROT_Provisioning\SM).
- Perform a regression (\STM32Cube_FW_H5\Firmware\Projects\STM32H573I-DK\ROT_Provisioning\DA\regression.bat) and restart at the beginning of this article.
3.1.2. SMAK production preparation phase outputs
Once the previous steps have been completed, the OEM holds:
- the tested SFI image ready for manufacturing (let's call it image.sfi)
- the SFI global license (let's call it sfi_global_license.bin)
- the module information in case of module with license (it is needed for the secure firmware installation) (let's call it module.mcsv)
3.2. HSM programming
inputs for HSM programming:
- OEM key (encryption AES key + nonce)
To program the HSM, you can follow the steps described in HSM programming using the STM32H573_DK MB1677 board.
After programming the HSM, it is now ready to be shipped to the CM together with the SFI package created before.
4. Manufacturing @ CM: Secure Firmware Installation
![]() 6min
6min
In this step, the CM receives from the OEM:
- the SFI image to be installed (image.sfi)
- the SFI global license (sfi_global_license.bin) or in case of sfi chip specific license, the HSM card provisioned with the OEM key and initialized with a max counter of licenses
- in case of licensed module:
- the module information (module.mcsv)
- the module global license file (module_global_license.bin) or in case of module chip specific license, the HSM card provisioned with the module secret key and initialized with a max counter of licenses
The SFI process could be performed through a regular JTAG/SWD interface or the system bootloader interface (you can refer to AN2606 for details on the supported interface for each microcontroller).
The following section covers JTAG/SWD and system bootloader interface - each section includes the following sections:
- Hardware connection
- Target initial state
- Secure Firmware Install
4.1. Hardware connection
4.1.1. Board
4.1.2. HSM card
Plug your HSM card provisioned with the SFI OEM key in case of SFI chip specific license.
Let's say the HSM card is plugged in smart card reader slot 0.
Plug your HSM card provisioned with the module secret key in case of module chip specific license.
Let's say the HSM card is plugged in smart card reader slot 1.
4.2. Software adaptation
Modify module.mcsv with the smart card reader slot index of the HSM card provisioned with the module secret key in case of module chip specific license (slot=1 in our example) or the path of the module global license.
4.3. Target initial state
The target shall be in Open product state.
If it is not the case, a DA full regression shall be performed.
After this step, the device is ready for the SFI process.
4.4. Firmware install
This command starts the SFI process:
- with sfi chip specific license
- with licensed module
and proceeds with the installation:
STM32_Programmer_CLI.exe -log .\sfi.log -c port=SWD mode=HOTPLUG -sfi .\image.sfi hsm=1 slot=0 -rsse C:\Program Files\STMicroelectronics\STM32Cube\STM32CubeProgrammer\bin\RSSe\H5\enc_signed_RSSe_SFI_STM32H5_v2.0.0.0.bin -mcsv .\module.mcsv
This command starts the SFI process with sfi global license and licensed module and proceeds with the installation:
STM32_Programmer_CLI.exe -log .\sfi.log -c port=SWD mode=HOTPLUG -sfi .\image.sfi hsm=0 license=.\sfi_global_license.bin -rsse C:\Program Files\STMicroelectronics\STM32Cube\STM32CubeProgrammer\bin\RSSe\H5\enc_signed_RSSe_SFI_STM32H5_v2.0.0.0.bin -mcsv .\module.mcsv
This command starts the SFI process with sfi global license and unlicensed module and proceeds with the installation:
STM32_Programmer_CLI.exe -log .\sfi.log -c port=SWD mode=HOTPLUG -sfi .\image.sfi hsm=0 license=.\sfi_global_license.bin -rsse C:\Program Files\STMicroelectronics\STM32Cube\STM32CubeProgrammer\bin\RSSe\H5\enc_signed_RSSe_SFI_STM32H5_v2.0.0.0.bin
You can check the log of the process saved in the file sfi.log:
-------------------------------------------------------------------
STM32CubeProgrammer v2.14.0
-------------------------------------------------------------------
ST-LINK SN : 003600374D46501220383832
ST-LINK FW : V3J10M3
Board : STM32H573I-DK
Voltage : 3.29V
SWD freq : 8000 KHz
Connect mode: Hot Plug
Reset mode : Software reset
Device ID : 0x484
Revision ID : --
Device name : STM32H5xx
Flash size : 2 MBytes
Device type : MCU
Device CPU : Cortex-M33
BL Version : 0xE4
SFSP Version: v2.4.0
Protocol Information : static
SFI File Information :
SFI file path : .\image.sfi
SFI license file path : .\HSM_License_V1.bin
SFI header information :
SFI protocol version : 2
SFI total number of areas : 11
SFI image version : 0
SFI Areas information :
Parsing Area 1/11 :
Area type : H
Area size : 16
Area destination address : 0x0
Parsing Area 2/11 :
Area type : O
Area size : 112
Area destination address : 0xFFD0100
Parsing Area 3/11 :
Area type : O
Area size : 272
Area destination address : 0xFFD0200
Parsing Area 4/11 :
Area type : O
Area size : 192
Area destination address : 0xFFD09D0
Parsing Area 5/11 :
Area type : O
Area size : 112
Area destination address : 0xFFD0A80
Parsing Area 6/11 :
Area type : S
Area size : 102952
Area destination address : 0x0
Parsing Area 7/11 :
Area type : S
Area size : 99350
Area destination address : 0x0
Parsing Area 8/11 :
Area type : F
Area size : 5744
Area destination address : 0x8100000
Parsing Area 9/11 :
Area type : K
Area size : 16
Area destination address : 0x0
Parsing Area 10/11 :
Area type : m
Area size : 131072
Area destination address : 0x8172000
Parsing Area 11/11 :
Area type : C
Area size : 48
Area destination address : 0x0
Warning: Option Byte: BOOT_UBE, value: 0xB4, was not modified.
Warning: Option Bytes are unchanged, Data won't be downloaded
Time elapsed during option Bytes configuration: 00:00:00.002
Reconnecting...
Reconnected !
Reconnecting...
Reconnected !
Time elapsed during option Bytes configuration: 00:00:02.442
ST-LINK SN : 003600374D46501220383832
ST-LINK FW : V3J10M3
Board : STM32H573I-DK
Voltage : 3.29V
SWD freq : 8000 KHz
Connect mode: Hot Plug
Reset mode : Software reset
Device ID : 0x484
Revision ID : --
Warning: Option Byte: SECBOOT_LOCK, value: 0xC3, was not modified.
Warning: Option Bytes are unchanged, Data won't be downloaded
Time elapsed during option Bytes configuration: 00:00:00.004
Warning: Option Byte: SECBOOTADD, value: 0xC0000, was not modified.
Warning: Option Byte: SECWM1_END, value: 0x7F, was not modified.
Warning: Option Byte: SECWM1_STRT, value: 0x0, was not modified.
Warning: Option Byte: SECWM2_END, value: 0x7F, was not modified.
Warning: Option Byte: SECWM2_STRT, value: 0x0, was not modified.
Warning: Option Byte: SRAM1_3_RST, value: 0x1, was not modified.
Reconnecting...
Reconnected !
Time elapsed during option Bytes configuration: 00:00:01.253
ST-LINK SN : 003600374D46501220383832
ST-LINK FW : V3J10M3
Board : STM32H573I-DK
Voltage : 3.29V
SWD freq : 8000 KHz
Connect mode: Hot Plug
Reset mode : Software reset
Device ID : 0x484
Revision ID : --
Reconnecting...
Reconnected !
Reconnecting...
Reconnected !
Time elapsed during option Bytes configuration: 00:00:02.884
ST-LINK SN : 003600374D46501220383832
ST-LINK FW : V3J10M3
Board : STM32H573I-DK
Voltage : 3.29V
SWD freq : 8000 KHz
Connect mode: Hot Plug
Reset mode : Software reset
Device ID : 0x484
Revision ID : --
Installing RSSe
Memory Programming ...
Opening and parsing file: enc_signed_RSSe_SFI_STM32H5_v2.0.0.0.bin
File : enc_signed_RSSe_SFI_STM32H5_v2.0.0.0.bin
Size : 53.81 KB
Address : 0x20054100
Erasing memory corresponding to segment 0:
Download in Progress:
File download complete
Time elapsed during download operation: 00:00:00.134
MCU Reset
ST-LINK SN : 003600374D46501220383832
ST-LINK FW : V3J10M3
Board : STM32H573I-DK
Voltage : 3.29V
SWD freq : 8000 KHz
Connect mode: Hot Plug
Reset mode : Software reset
Device ID : 0x484
Revision ID : --
Get RSSe status...
RSS version = 2.2.0
RSSe version = 2.0.0
Starting SFI
Processing license...
Get RSSe status...
Processing Image Header
Get RSSe status...
Processing Area 1...
Get RSSe status...
Area Address = 0x0
Area Type = H
Processing Area 2...
Get RSSe status...
Area Address = 0xFFD0100
Area Type = O
Processing Area 3...
Get RSSe status...
Area Address = 0xFFD0200
Area Type = O
Processing Area 4...
Get RSSe status...
Area Address = 0xFFD09D0
Area Type = O
Processing Area 5...
Get RSSe status...
Area Address = 0xFFD0A80
Area Type = O
Processing Area 6...
Get RSSe status...
Area Address = 0x0
Area Type = S
Processing Area 7...
Get RSSe status...
Area Address = 0x0
Area Type = S
Processing Area 8...
Get RSSe status...
Area Address = 0x8100000
Area Type = F
Processing Area 9...
Get RSSe status...
Area Address = 0x0
Area Type = K
MCSV file parsing...
Total modules number: 1
+ Module number : [0]
Name : .\module.smu
Type : Global license
Size : 128.00 KB
Address : 0x08172000
Prepare module payload with license data...
Processing Area 10...
Get RSSe status...
Area Address = 0x8172000
Area Type = m
Processing Area 11...
Can not verify last area
Area Address = 0x0
Area Type = C
SFI Process Finished!
SFI file .\image.sfi Install Operation Success
Time elapsed during SFI install operation: 00:00:18.984
At this step, the device is programmed with the Secure Manager and OEM non-secure application.
4.5. Troubleshooting
In case of failure, you can check sfi.log and run the \STM32Cube_FW_H5\Firmware\Projects\STM32H573I-DK\ROT_Provisioning\DA\regression.bat in order to come back in Open state and be able to launch a new SFI procedure.