This article provides information about how to use the STM32 sniffer for Bluetooth® Low Energy with Wireshark. For this tutorial, we presume that you've already installed the sniffer, but if this is not the case, you can follow this guide.
1. Starting the capture
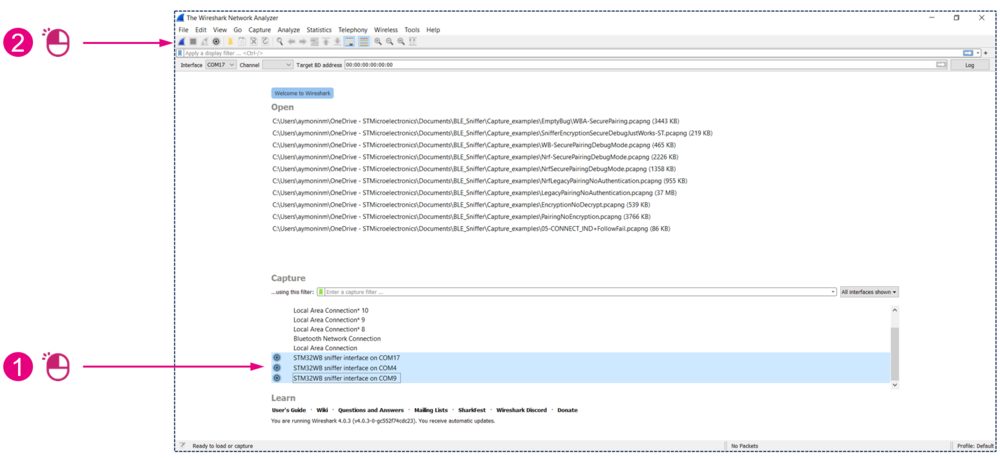
Plug in your sniffer board and open Wireshark.
1.1. Optional configuration
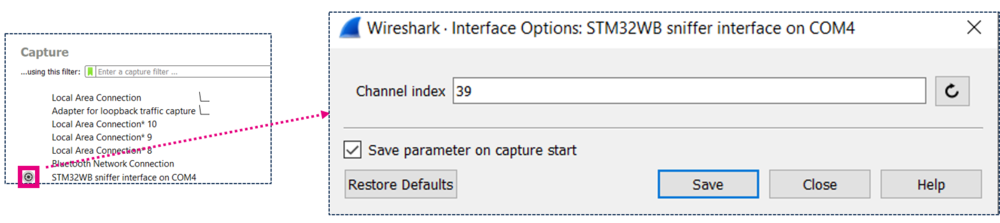
- In Wireshark, click on the wheel on the left side of the STM32 sniffer interface to open the interface configuration menu.
- The channel index parameter is the channel on which the sniffer will listen when started. It can be changed on the fly later on. The default channel index is 39.
- This is the channel index, not the frequency index (the primary advertising channel indexes are 37, 38, and 39).
| Channel index |
|---|
1.2. Launching the capture
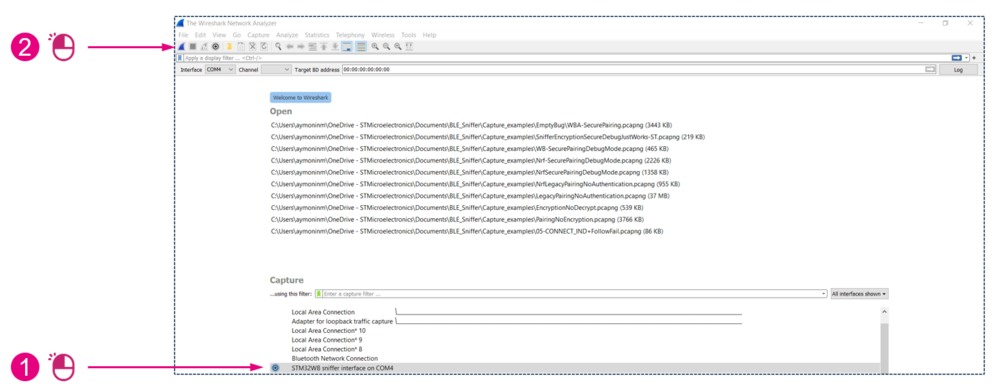
To start the capture:
or
| Starting the capture |
|---|
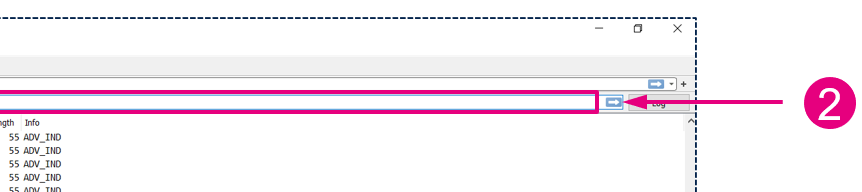
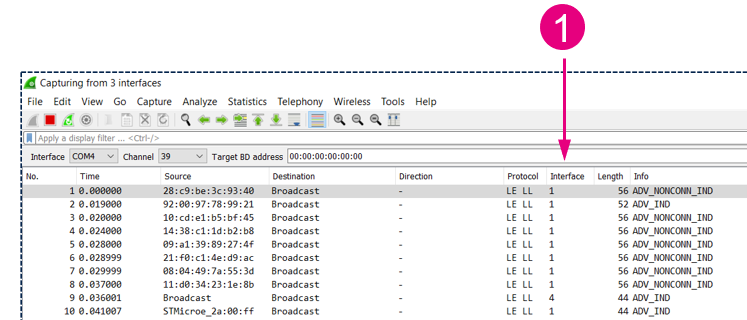
1.3. Sniffer started
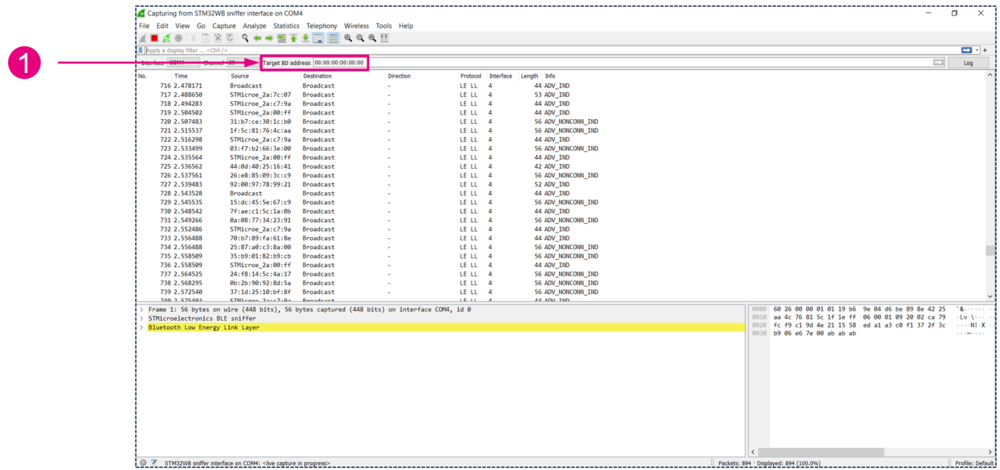
You should now see the advertising packets on the channel you configured.
| Target BD address |
|---|
2. Following a connection
When the sniffer is running, it reports advertising, scan requests and scan requests of all devices. You can then set the BD address of the target device that you want to follow when a connection to it occurs.
| Setting a target to follow |
|---|
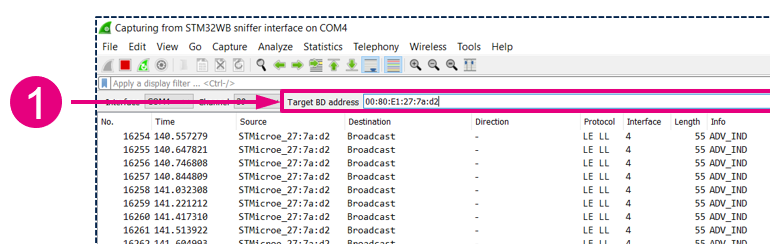
Now you should only see:
- Advertising and scan response packets from the target.
- Scan requests to the target.
- Connection packets from and to the target.
| Target set |
|---|
If after setting the target there are no more incoming packets, either:
- There is no device with this BD address advertising on this channel.
- The sniffer has not received the command; set the target again (you will need to make a change to be able to apply changes. Just delete the last number and re-enter it).
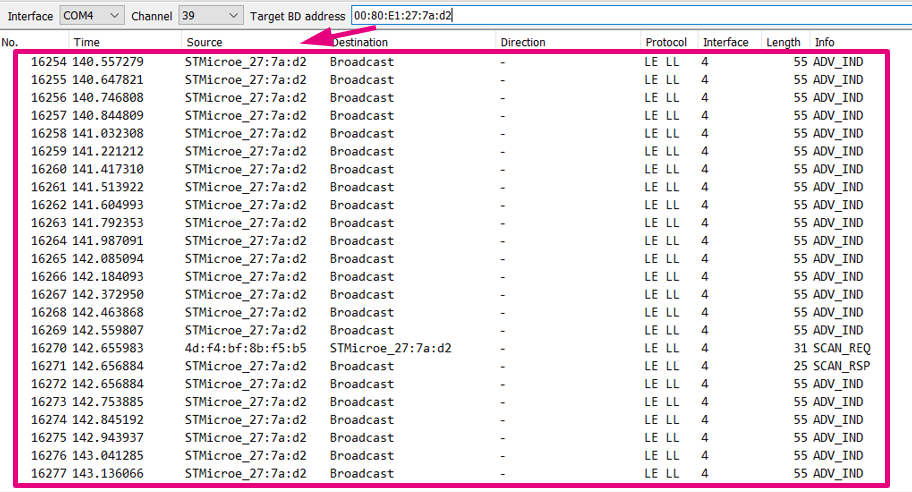
Now if a device connects to your target and the sniffer intercepts the CONNECT_IND packet, you will start to see the communication between the two devices.
| Connection intercepted |
|---|
Now you have some additional data:
- The direction column indicates the direction of the packets.
- The color of the lines alternates with each connection event.
If the connection is terminated or if the sniffer loses it, it will return to the advertising channel you configured before.
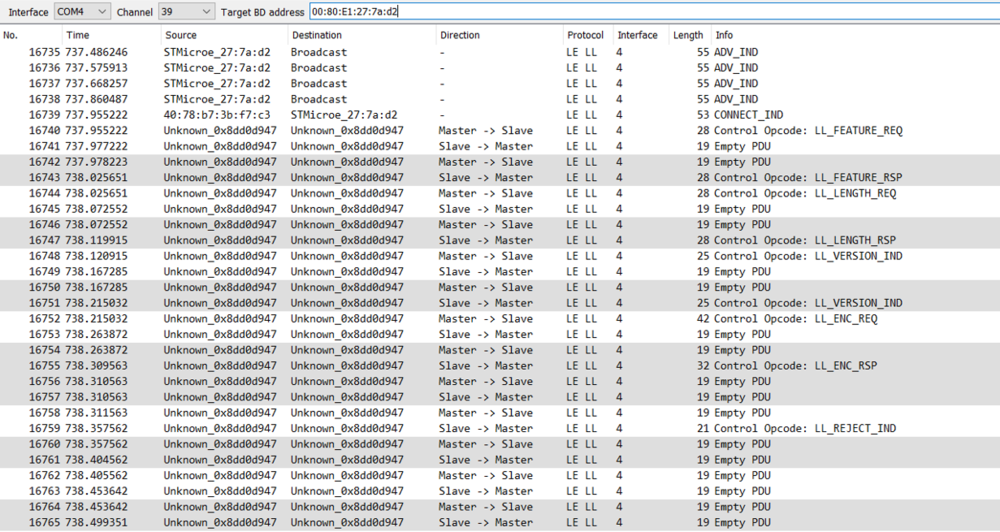
3. Multiple interfaces capture
Because the sniffer can listen to only one channel at a time, capturing from multiple hardware interfaces can be very useful. You can capture the traffic on all advertising channel and pick up the connect request no matter on which channel it happens. You can also follow multiple links.
To capture with multiple sniffers, plug your boards and to start the capture:
| Start capturing from multiple interfaces |
|---|
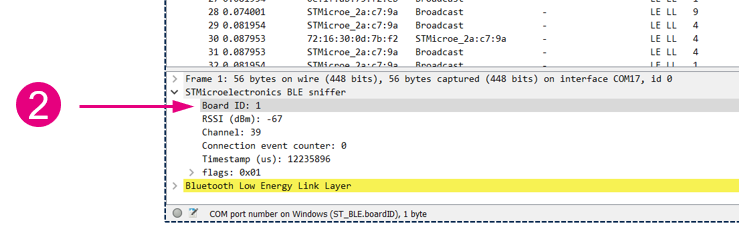
During the capture you can identify on which sniffer the packets have been captured:
| Capture example from multiples interfaces |
|---|
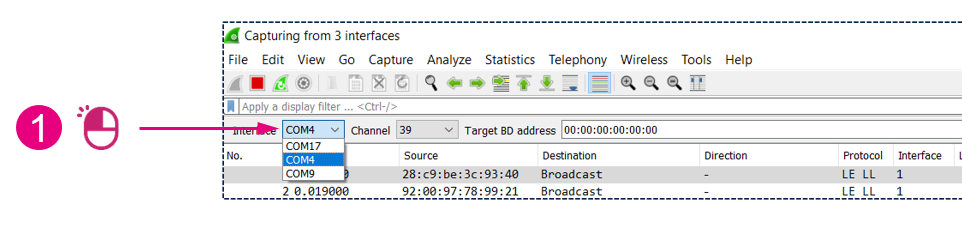
To control each sniffer:
| Controlling multiples interfaces |
|---|
In case you want each sniffer to be able to intercept a connection, enter for each sniffer the target BD address.
4. Key input
For links that will be encrypted without debug mode or legacy pairing just work, the sniffer needs additional data to decrypt the traffic. On the right side of the toolbar, you have a key type selector and an associated value field. This input gives you the possibility to provide additional data that the sniffer can't know just by listening to the over the air communications. You can give the following data:
- Legacy passkey: The key entered shall be 128 bits wide. The PassKey shall be zero-padded. For example, if the passkey was 401190 (decimal) -> 0x61F26 (hexa) you shall enter : 000000000000000000000000000061F6.
- Legacy OOB data: The key entered shall be 128 bits wide. The value shall be entered with the MSO on the leftmost byte.
- LTK: The key entered shall be 128 bits wide. The value shall be entered with the MSO on the leftmost byte. The key will be used during a secure connection pairing if none of the devices are in debug mode.
The key shall be entered:
- The pairing start for legacy PassKey and OOB data
- Before the LL encryption start for the LTK
If you encounter problems, you can check the Troubleshooting article.